Typically we all use SSH and FTP services often to access the remote servers and virtual private servers. As a Linux administrator, you must aware about how to block SSH and FTP access to specific IP or network range in Linux in order to tighten the security bit more.
This tutorial will show you how to block SSH and FTP access to a particular IP address and/or a network range in CentOS 6 and 7 server. This guide was tested on CentOS 6.x and 7.x versions, but it will probably work on other Linux distributions such as Debian, Ubuntu, and SUSE/openSUSE etc.
We’ll do it in two methods. The first method is using IPTables/firewallD and the second method is using TCP wrappers with the help of hosts.allow and hosts.deny file.
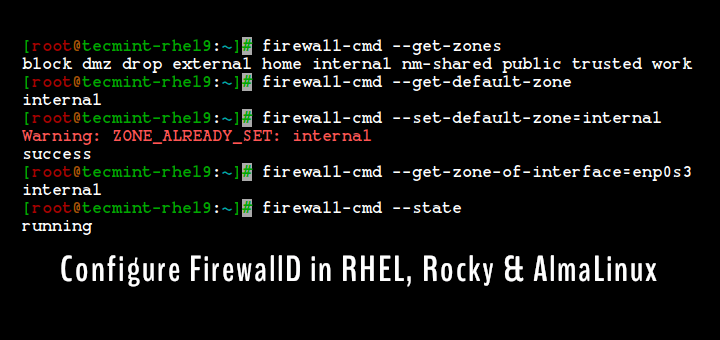
Refer the following guides to know more about IPTables and Firewalld.
- Basic Guide on IPTables (Linux Firewall) Tips / Commands
- How To Setup an Iptables Firewall to Enable Remote Access to Services in Linux
- How to Configure ‘FirewallD’ in RHEL/CentOS 7 and Fedora 21
- Useful ‘FirewallD’ Rules to Configure and Manage Firewall in Linux
Now you aware about what is IPTables and FirewallD and it’s basics.
Method 1: Block SSH and FTP Access Using IPTables/FirewallD
Now let us see how to block SSH and FTP access to a specific IP (for example 192.168.1.100) and/or network range (for example 192.168.1.0/24) using IPtables on RHEL/CentOS/Scientific Linux 6.x versions and FirewallD on CentOS 7.x.
Block or Disable SSH Access
--------------------- On IPtables Firewall --------------------- # iptables -I INPUT -s 192.168.1.100 -p tcp --dport ssh -j REJECT # iptables -I INPUT -s 192.168.1.0/24 -p tcp --dport ssh -j REJECT
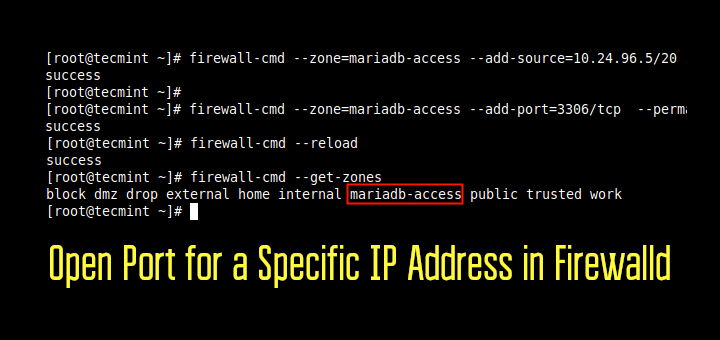
--------------------- On FirewallD --------------------- # firewall-cmd --direct --add-rule ipv4 filter INPUT 1 -m tcp --source 192.168.1.100 -p tcp --dport 22 -j REJECT # firewall-cmd --direct --add-rule ipv4 filter INPUT 1 -m tcp --source 192.168.1.100/24 -p tcp --dport 22 -j REJECT
To take new rules into effect, you need to use the following command.
# service iptables save [On IPtables Firewall] # firewall-cmd --reload [On FirewallD]
Now, try to SSH the server from the blocked host. Please be mindful that here 192.168.1.150 is the blocked host.
# ssh 192.168.1.150
You should see the following message.
ssh: connect to host 192.168.1.150 port 22: Connection refused
Unblock or Enable SSH Access
To unblock or enable SSH access, go to the remote server and run the following command:
--------------------- On IPtables Firewall --------------------- # iptables -I INPUT -s 192.168.1.100 -p tcp --dport ssh -j ACCEPT # iptables -I INPUT -s 192.168.1.100/24 -p tcp --dport ssh -j ACCEPT
--------------------- On FirewallD --------------------- # firewall-cmd --direct --add-rule ipv4 filter INPUT 1 -m tcp --source 192.168.1.100 -p tcp --dport 22 -j ACCEPT # firewall-cmd --direct --add-rule ipv4 filter INPUT 1 -m tcp --source 192.168.1.100/24 -p tcp --dport 22 -j ACCEPT
Save the changes using following to access your server via SSH.
# service iptables save [On IPtables Firewall] # firewall-cmd --reload [On FirewallD]
Block or Disable FTP Access
Typically, the default ports for FTP are 20 and 21. So, to block all FTP traffic using IPTables run the following command:
--------------------- On IPtables Firewall --------------------- # iptables -I INPUT -s 192.168.1.100 -p tcp --dport 20,21 -j REJECT # iptables -I INPUT -s 192.168.1.100/24 -p tcp --dport 20,21 -j REJECT
--------------------- On FirewallD --------------------- # firewall-cmd --direct --add-rule ipv4 filter INPUT 1 -m tcp --source 192.168.1.100 -p tcp --dport 20,21 -j REJECT # firewall-cmd --direct --add-rule ipv4 filter INPUT 1 -m tcp --source 192.168.1.100/24 -p tcp --dport 20,21 -j REJECT
To take new rules into effect, you need to use the following command.
# service iptables save [On IPtables Firewall] # firewall-cmd --reload [On FirewallD]
Now, try to access the server from the blocked host (192.168.1.100), with command:
# ftp 192.168.1.150
You’ll get an error message something like below.
ftp: connect: Connection refused
Unblock or Enable FTP Access
To unblock and enable FTP access back, run:
--------------------- On IPtables Firewall --------------------- # iptables -I INPUT -s 192.168.1.100 -p tcp --dport 20,21 -j ACCEPT # iptables -I INPUT -s 192.168.1.100/24 -p tcp --dport 20,21 -j ACCEPT
--------------------- On FirewallD --------------------- # firewall-cmd --direct --add-rule ipv4 filter INPUT 1 -m tcp --source 192.168.1.100 -p tcp --dport 20,21 -j ACCEPT # firewall-cmd --direct --add-rule ipv4 filter INPUT 1 -m tcp --source 192.168.1.100/24 -p tcp --dport 20,21 -j ACCEPT
Save the changes with command:
# service iptables save [On IPtables Firewall] # firewall-cmd --reload [On FirewallD]
Now, try to access the server via FTP:
# ftp 192.168.1.150
Enter your ftp username and password.
Connected to 192.168.1.150. 220 Welcome to TecMint FTP service. Name (192.168.1.150:sk): tecmint 331 Please specify the password. Password: 230 Login successful. Remote system type is UNIX. Using binary mode to transfer files. ftp>
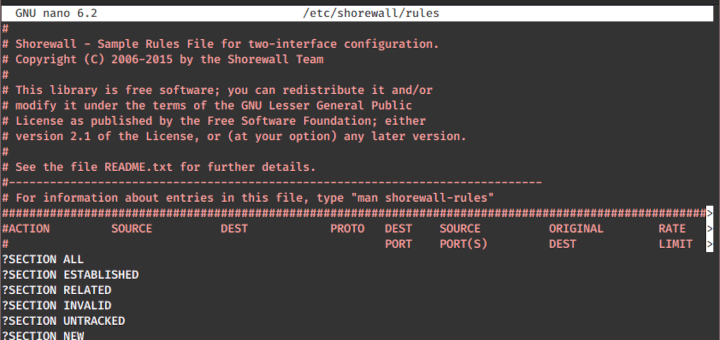
Method 2: Block SSH and FTP Access Using TCP Wrappers
If you don’t want to mess with IPTables or FirewallD, then TCP wrappers is the better way to block SSH and FTP access to a specific IP and/or a range of network.
OpenSSH and FTP are compiled with TCP wrappers support, which means you can specify which hosts are allowed to connect without touching your firewall in the following two important files and are:
- /etc/hosts.allow
- /etc/hosts.deny
As the name implies, the first file contains entries of allowed hosts, and the second contains addresses of blocked hosts.
For example, let us block the SSH and FTP access to host that has IP address 192.168.1.100 and network range 192.168.1.0. This method is same for CentOS 6.x and 7.x series. And, of course, it will work on other distributions such as Debian, Ubuntu, SUSE, openSUSE etc.
Open the /etc/hosts.deny file and add the following IP Addresses or network range you wish to block as shown below.
##### To block SSH Access ##### sshd: 192.168.1.100 sshd: 192.168.1.0/255.255.255.0 ##### To block FTP Access ##### vsftpd: 192.168.1.100 vsftpd: 192.168.1.0/255.255.255.0
Save and exit the file.
Now, restart sshd and vsftpd service to take new changes into effect.
--------------- For SSH Service --------------- # service sshd restart [On SysVinit] # systemctl restart sshd [On SystemD]
--------------- For FTP Service --------------- # service vsftpd restart [On SysVinit] # systemctl restart vsftpd [On SystemD]
Now, try to SSH the server or from a blocked host.
# ssh 192.168.1.150
You’ll see the following output:
ssh_exchange_identification: read: Connection reset by peer
Now, try to FTP the server or from a blocked host.
# ftp 192.168.1.150
You’ll see the following output:
Connected to 192.168.1.150. 421 Service not available.
To unblock or enable SSH and FTP services again, edit hosts.deny file and comment out all lines and finally restart vsftpd and sshd services.
Conclusion
That’s all for now. To summing up, today we learned how to block a specific IP address and network range using IPTables, FirewallD, and TCP wrappers. These methods are pretty easy and straightforward.
Even, a novice Linux administrator can do this in a couple minutes. If you know some other ways to block SSH and FTP access, feel free to share them in the comment section. And don’t forget to share our articles in your all social networks.


Senthil,
This is a nice article for iptables. I’m using it to block access from countries that we do not do business. Your readers could download the free list from ip2location.com/free/visitor-blocker and it is working fine using iptables.
Hey, you have mentioned what to do to allow few IP address or range for the FTP access. But before allowing them we have to block the FTP at all and then I’ll keep adding IDs which I want to be allowed.
So What will be the first step?
I not able to block facebook.com on lan (but in lan particular ip and i don’t want to use squid server for this ). i have two interface, eth0 is a WAN interface and eth1 is a lan interface.
I want to block facebook.com on 192.168.10.16 and rest able to access facebook.com. how can i do this and I am using Centos 6.7
@Ravinder,
You can block facebook.com for particular network IP address and rest allowed using iptables as shown.
Simply edit /etc/hosts and add line
127.0.0.1 facebook.com www.facebook.comand others what should be disabled. FB works on DNS, and this modification redirects all trafic to internal ip 127.0.0.1 .with TCP Wrappers you don’t have too restart sshd or vsftpd.
# firewall-cmd –direct –add-rule ipv4 filter INPUT 1 -m tcp –source 192.168.1.100/24 -p tcp –dport 22 -j REJECT <—-here can we put 192.168.1.0/24
#iptables -I INPUT -s 192.168.1.100/24 -p tcp –dport ssh -j ACCEPT <—-here can we put 192.168.1.0/24
Thanks for the tutorial. First of all can’t we do it with rich rule ?? I asked a question to many expert. I am having a FTP server , around 30 users from accross the world send some file on that server. previously i used iptable and give access to them and later i denied all . and that works fine. What is my question is that in firewalld richrule or direct rule do i need to do any deny rule after all the permit rule ??
I havn’t got any ans. regarding it . Could you please tell me do i need to and if so then what would be the systex ??
Thanks
Ehsan
Very nice and simple article !
Thanks !
You’re welcome. Stay tuned with TecMint for more useful articles.