HAProxy stands for High Availability proxy. It is a Free and open source application written in C programming Language. HAProxy application is used as TCP/HTTP Load Balancer and for proxy Solutions. The most common use of the HAProxy application is to distribute the workload across multiple servers e.g., web server, database server, etc thus improving the overall performance and reliability of server environment.
The highly efficient and fast application is used by many of the world’s reputed organization which includes but not limited to – Twitter, Reddit, GitHub and Amazon. It is available for Linux, BSD, Solaris and AIX platform.
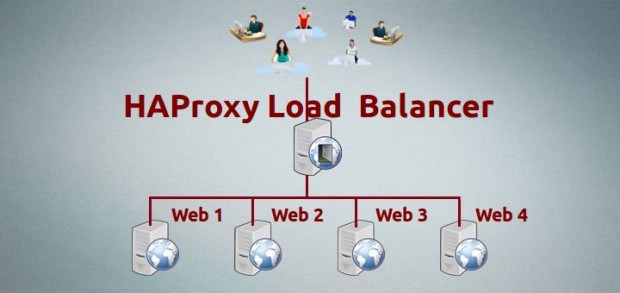
In this tutorial, we will discuss the process of setting up a high availability load balancer using HAProxy to control the traffic of HTTP-based applications (web servers) by separating requests across multiple servers.
For this article, we’re using the most recent stable release of HAProxy version i.e. 1.5.10 released on December 31st 2014. And also we’re using CentOS 6.5 for this setup, but the below given instructions also works on CentOS/RHEL/Fedora and Ubuntu/Debian distributions.
My Environment Setup
Here our load-balancer HAProxy server having hostname as websrv.tecmintlocal.com with IP address 192.168.0.125.
HAProxy Server Setup
Operating System : CentOS 6.5 IP Address : 192.168.0.125 Hostname : websrv.tecmintlocal.com
Client Web Servers Setup
The other four machines are up and running with web servers such as Apache.
Web Server #1 : CentOS 6.5 [IP: 192.168.0.121] - [hostname: web1srv.tecmintlocal.com] Web Server #2 : CentOS 6.5 [IP: 192.168.0.122] - [hostname: web2srv.tecmintlocal.com] Web Server #3 : CentOS 6.5 [IP: 192.168.0.123] - [hostname: web3srv.tecmintlocal.com] Web Server #4 : CentOS 6.5 [IP: 192.168.0.124] - [hostname: web4srv.tecmintlocal.com]
Step 1: Installing Apache on Client Machines
1. First we have to install Apache in all four server’s and share any one of site, for installing Apache in all four server’s here we going to use following command.
# yum install httpd [On RedHat based Systems] # apt-get install apache2 [On Debian based Systems]
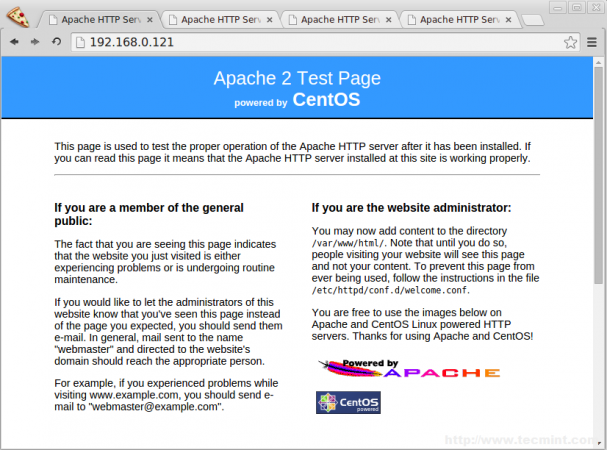
2. After installing Apache web server on all four client machines, you can verify anyone of the server whether Apache is running by accessing it via IP address in browser.
http://192.168.0.121
Step 2: Installing HAProxy Server
3. In most of the today’s modern Linux distributions, HAPRoxy can be easily installed from the default base repository using default package manager yum or apt-get.
For example, to install HAProxy on RHEL/CentOS/Fedora and Debian/Ubuntu versions, run the following command. Here I’ve included openssl package too, because we’re going to setup HAProxy with SSL and NON-SSL support.
# yum install haproxy openssl-devel [On RedHat based Systems] # apt-get install haproxy [On Debian based Systems]
Note: On Debian Whezzy 7.0, we need to enable the backports repository by adding a new file backports.list under “/etc/apt/sources.list.d/” directory with the following content.
# echo "deb http://cdn.debian.net/debian wheezy-backports main" >> /etc/apt/sources.list.d/backports.list
Next, update the repository database and install HAProxy.
# apt-get update # apt-get install haproxy -t wheezy-backports
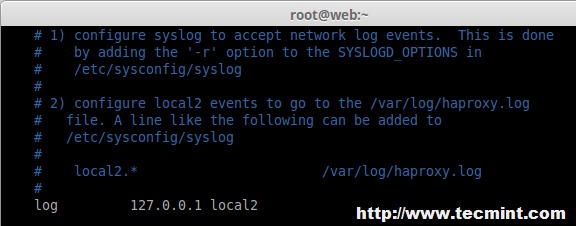
Step 3: Configure HAProxy Logs
4. Next, we need to enable logging feature in HAProxy for future debugging. Open the main HAProxy configuration file ‘/etc/haproxy/haproxy.cfg‘ with your choice of editor.
# vim /etc/haproxy/haproxy.cfg
Next, follow the distro-specific instructions to configure logging feature in HAProxy.
On RHEL/CentOS/Fedora
Under #Global settings, enable the following line.
log 127.0.0.1 local2
On Ubuntu/Debian
Under #Global settings, replace the following lines,
log /dev/log local0 log /dev/log local1 notice
With,
log 127.0.0.1 local2
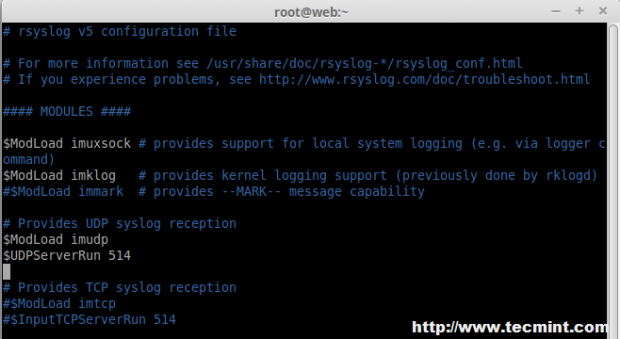
5. Next, we need to enable UDP syslog reception in ‘/etc/rsyslog.conf‘ configuration file to separate log files for HAProxy under /var/log directory. Open your your ‘rsyslog.conf‘ file with your choice of editor.
# vim /etc/rsyslog.conf
Uncommnet ModLoad and UDPServerRun, Here our Server will listen to Port 514 to collect the logs into syslog.
# Provides UDP syslog reception $ModLoad imudp $UDPServerRun 514
6. Next, we need to create a separate file ‘haproxy.conf‘ under ‘/etc/rsyslog.d/‘ directory to configure separate log files.
# vim /etc/rsyslog.d/haproxy.conf
Append following line to the newly create file.
local2.* /var/log/haproxy.log
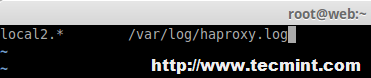
Finally, restart the rsyslog service to update the new changes.
# service rsyslog restart