Normally, advanced users prefer to use and manage MySQL database management system from its command prompt, on the other side, this method has proved to be a great challenge for relatively new Linux users.
Therefore, in order to make things easy for the newbies, PhpMyAdmin was created.
PhpMyAdmin is a free and open source, web based MySQL/MariaDB administration software written in PHP. It offers users a easy way to interact with MySQL via a web browser.
Suggested Read: 5 Useful Tips to Secure SSH Server
In this article we will share some tips to secure your phpmyadmin installation on a LAMP or LEMP stack against the most common attacks carried out by malicious individuals.
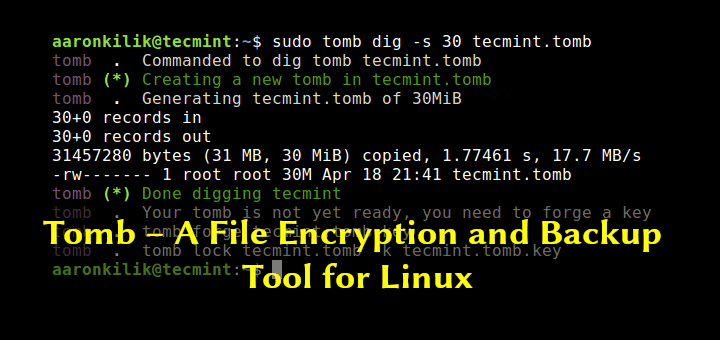
1. Change Default PhpMyAdmin Login URL
The first tip will help keep off attackers from effortlessly accessing your PhpMyAdmin application through the common and well known, default login URL located at http://<ip address>/phpmyadmin.
To change the default login URL of PhpMyAdmin, go through this article: Change Default PhpMyAdmin Login URL
2. Enable HTTPS on PhpMyAdmin
Secondly, this tip enables you learn how to use SSL (Secure Socket Layer) certificates to secure your PhpMyAdmin login page, by preventing your username and password from being transmitted in plain text, which attackers can easily sniff over a network.
Read this tip: Setup HTTPS (SSL Certificate) on PhpMyAdmin
3. Password Protect on PhpMyAdmin
This third tip shows you, how to use htpasswd utility to generate a password file for an account that shall be authorized to access the phpmyadmin login page using username and password.
Read this tip: Password Protect PhpMyAdmin Login Interface
4. Disable root Login to PhpMyAdmin
Last but not least, learn how to disable root access to your PhpMyAdmin, which is a recommended practice not only for phpmyadmin but for all web-based interfaces.
Read this tip: Disable root Database Access to PhpMyAdmin
In this article we have shared 4 tips to secure phpmyadmin. If you followed them step by step, you should now be able to manage your databases using a web interface instead of the command line.
Suggested Read: 15 Useful MySQL/MariaDB Performance Tuning Tips
Do you have any comments or suggestions about this article? Perhaps other tips we should consider? Feel free to drop us a note using the comment form below – we look forward to hearing from you!



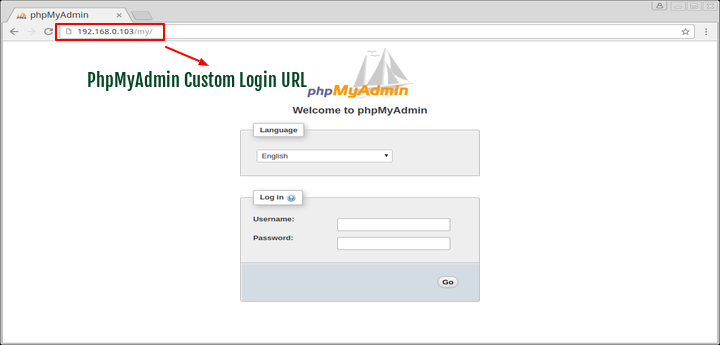
Use front end authentication on your PHPMyAdmin URL