Since computers seldom work as isolated systems, it is to be expected that as a system administrator or engineer, you know how to set up and maintain a network with multiple types of servers.
In this article and in the next of this series we will go through the essentials of setting up Samba and NFS servers with Windows/Linux and Linux clients, respectively.
This article will definitely come in handy if you’re called upon to set up file servers in corporate or enterprise environments where you are likely to find different operating systems and types of devices.
Since you can read about the background and the technical aspects of both Samba and NFS all over the Internet, in this article and the next we will cut right to the chase with the topic at hand.
Step 1: Installing Samba Server
Our current testing environment consists of two RHEL 7 boxes and one Windows 8 machine, in that order:
1. Samba / NFS server [box1 (RHEL 7): 192.168.0.18], 2. Samba client #1 [box2 (RHEL 7): 192.168.0.20] 3. Samba client #2 [Windows 8 machine: 192.168.0.106]

On box1, install the following packages:
# yum update && yum install samba samba-client samba-common
On box2:
# yum update && yum install samba samba-client samba-common cifs-utils
Once the installation is complete, we’re ready to configure our share.
Step 2: Setting Up File Sharing Through Samba
One of the reason why Samba is so relevant is because it provides file and print services to SMB/CIFS clients, which causes those clients to see the server as if it was a Windows system (I must admit I tend to get a little emotional while writing about this topic as it was my first setup as a new Linux system administrator some years ago).
Adding system users and setting up permissions and ownership
To allow for group collaboration, we will create a group named finance with two users (user1 and user2) with useradd command and a directory /finance in box1.
We will also change the group owner of this directory to finance and set its permissions to 0770 (read, write, and execution permissions for the owner and the group owner):
# groupadd finance # useradd user1 # useradd user2 # usermod -a -G finance user1 # usermod -a -G finance user2 # mkdir /finance # chmod 0770 /finance # chgrp finance /finance
Step 3: Configuring SELinux and Firewalld
In preparation to configure /finance as a Samba share, we will need to either disable SELinux or set the proper boolean and security context values as follows (otherwise, SELinux will prevent clients from accessing the share):
# setsebool -P samba_export_all_ro=1 samba_export_all_rw=1 # getsebool –a | grep samba_export # semanage fcontext –at samba_share_t "/finance(/.*)?" # restorecon /finance
In addition, we must ensure that Samba traffic is allowed by the firewalld.
# firewall-cmd --permanent --add-service=samba # firewall-cmd --reload
Step 4: Configure Samba Share
Now it’s time to dive into the configuration file /etc/samba/smb.conf and add the section for our share: we want the members of the finance group to be able to browse the contents of /finance, and save / create files or subdirectories in it (which by default will have their permission bits set to 0770 and finance will be their group owner):
[finance] comment=Directory for collaboration of the company's finance team browsable=yes path=/finance public=no valid users=@finance write list=@finance writeable=yes create mask=0770 Force create mode=0770 force group=finance
Save the file and then test it with the testparm utility. If there are any errors, the output of the following command will indicate what you need to fix. Otherwise, it will display a review of your Samba server configuration:
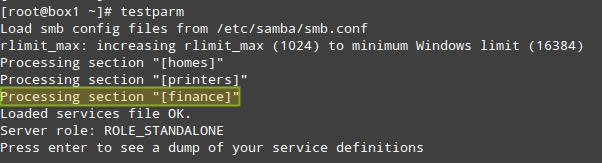
Should you want to add another share that is open to the public (meaning without any authentication whatsoever), create another section in /etc/samba/smb.conf and under the new share’s name copy the section above, only changing public=no to public=yes and not including the valid users and write list directives.
Step 5: Adding Samba Users
Next, you will need to add user1 and user2 as Samba users. To do so, you will use the smbpasswd command, which interacts with Samba’s internal database. You will be prompted to enter a password that you will later use to connect to the share:
# smbpasswd -a user1 # smbpasswd -a user2
Finally, restart Samba, enable the service to start on boot, and make sure the share is actually available to network clients:
# systemctl start smb # systemctl enable smb # smbclient -L localhost –U user1 # smbclient -L localhost –U user2
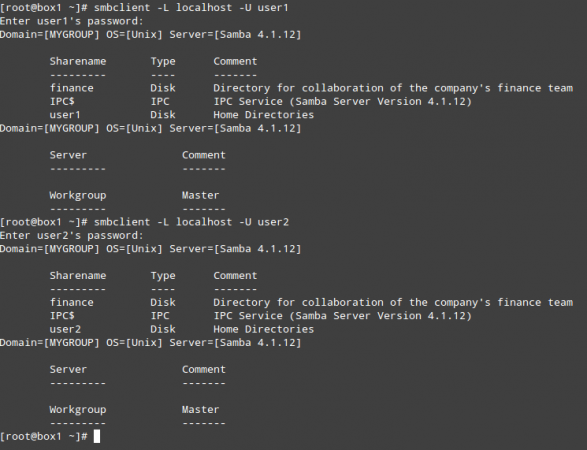
At this point, the Samba file server has been properly installed and configured. Now it’s time to test this setup on our RHEL 7 and Windows 8 clients.
Step 6: Mounting the Samba Share in Linux
First, make sure the Samba share is accessible from this client:
# smbclient –L 192.168.0.18 -U user2
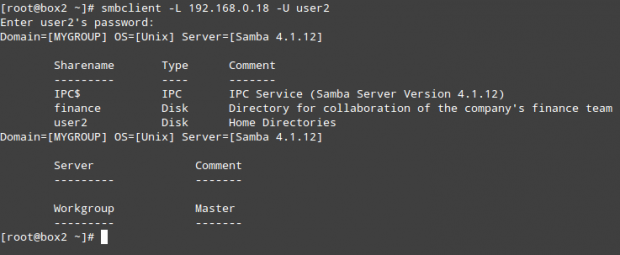
(repeat the above command for user1)
As any other storage media, you can mount (and later unmount) this network share when needed:
# mount //192.168.0.18/finance /media/samba -o username=user1
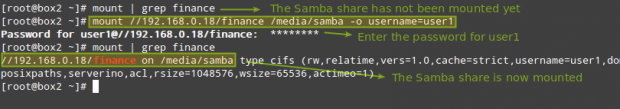
(where /media/samba is an existing directory)
or permanently, by adding the following entry in /etc/fstab file:
//192.168.0.18/finance /media/samba cifs credentials=/media/samba/.smbcredentials,defaults 0 0
Where the hidden file /media/samba/.smbcredentials (whose permissions and ownership have been set to 600 and root:root, respectively) contains two lines that indicate the username and password of an account that is allowed to use the share:
username=user1 password=PasswordForUser1
Finally, let’s create a file inside /finance and check the permissions and ownership:
# touch /media/samba/FileCreatedInRHELClient.txt
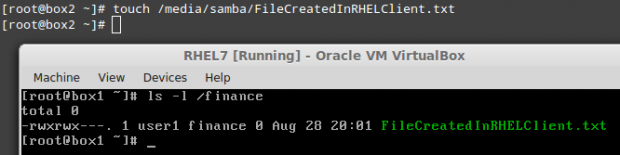
As you can see, the file was created with 0770 permissions and ownership set to user1:finance.
Step 7: Mounting the Samba Share in Windows
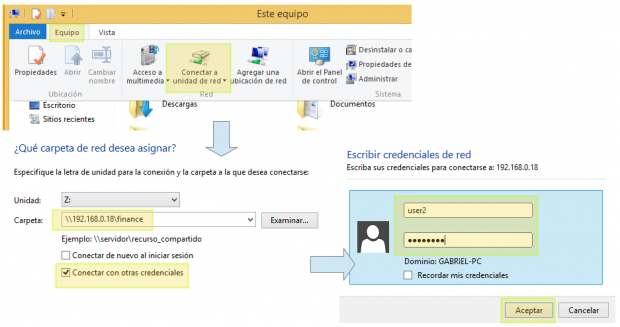
To mount the Samba share in Windows, go to My PC and choose Computer, then Map network drive. Next, assign a letter for the drive to be mapped and check Connect using different credentials (the screenshots below are in Spanish, my native language):
Finally, let’s create a file and check the permissions and ownership:
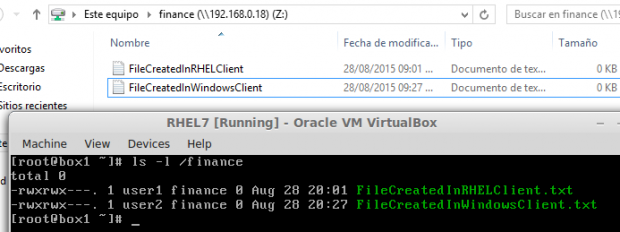
# ls -l /finance
This time the file belongs to user2 since that’s the account we used to connect from the Windows client.
Summary
In this article we have explained not only how to set up a Samba server and two clients using different operating systems, but also how to configure the firewalld and SELinux on the server to allow the desired group collaboration capabilities.
Last, but not least, let me recommend the reading of the online man page of smb.conf to explore other configuration directives that may be more suitable for your case than the scenario described in this article.
As always, feel free to drop a comment using the form below if you have any comments or suggestions.

“smbclient -L localhost –U user1” – is not working on rhel 7.4.
Please resolve this.
You need to install smbclient.
Dear All,
I have configured Samba on Centos 7.5 and now samba is working fine on few windows systems but on few windows systems, we are not able to connect. it is giving credential issue. but the same credentials it is working on a few windows systems.
Thanks i was able to resolve my problem
I followed the process thought above, this is the error i get. I don’t know to resolve this and i don’t know how i am getting this above error.
Please any help will be highly appreciated..
Could you help me to configure ready only samba but some user will be get read write access.
and also help me how to configure multi path NFS server. pls pls pls
I believe you should not be setting samba_export_all_ro and samba_export_all_rw to 1. This will allow Samba to access system files in an RO/RW mode outside of the /finance directory.
All that is needed is:
samba_export_all_ro:
Export any file or directory, allowing read-only permissions. This allows files and directories that are not labeled with the samba_share_t type to be shared through Samba. When the samba_export_all_ro Boolean is on, but the samba_export_all_rw Boolean is off, write access to Samba shares is denied, even if write access is configured in /etc/samba/smb.conf, as well as Linux permissions allowing write access.
samba_export_all_rw:
Export any file or directory, allowing read and write permissions. This allows files and directories that are not labeled with the samba_share_t type to be exported through Samba. Permissions in /etc/samba/smb.conf and Linux permissions must be configured to allow write access.
Thank you Gabriel Cánepa, your suggestions worked with Fedora 30 Server accessed from a Windows 10-i9-9900k machine running Windows 10 (1903/18362.10006).
Mmm… I am not so sure that Brian L Simonin’s comment (posted May 18, 2018 at 12:54 am) allows the continued work-ability of Gabriel’s excellent solution. When
*samba_export_all_ro:*and*samba_export_all_rw:*were both turned off (well set to 0 to be more accurate) a separate networked Windows 10 machine complained that it could not access shared files on an ntfs partition accessed with the ntfs-g3 setting in fstab; when I only tried turning back on*samba_export_all_ro:*it still could read the files and directories okay with*samba_export_all_rw:*still set to zero.Thank you again Gabriel for a well written article.
mp
Now i want to create a centralized file share server for 20 users, the each users has each folder and each folder has 10gb the users access only respective folder with credential how to do that.
@Pradeep,
Follow this guide, it explains everything you looking for your setup..
How to Install Samba4 on CentOS 7 for File Sharing on Windows
Thank you @Ravi for your help.
Hi,
thanks for your notes. i got the output from following your instructions.
but i have problem in understanding below selinux parameter, could you please explain that ?
fix permissions on new directories:
force directory mode = 0770
directory mask = 0770
Never mind Gabriel. I got it right now. Before now, I used sudo to do everything. But then I redid it in root account and thins worked fine
Thank you Gabriel for such nice tutorial. I hope you can still respond to my question. I followed those steps precisely and got this error on client side:
sam@samuel:~$ sudo mount //192.168.1.100/home/seun/finance /media/samba -o user=tosin
Password for tosin@//192.168.1.100/home/seun/finance: *****
Retrying with upper case share name
mount error(6): No such device or address
Refer to the mount.cifs(8) manual page (e.g. man mount.cifs)
sam@samuel:~$ smbclient -L 192.168.1.100
WARNING: The “syslog” option is deprecated
Enter sam’s password:
session setup failed: NT_STATUS_LOGON_FAILURE
sam@samuel:~$
I also got access denied error on windows 7 client too.
@Seun,
This is an authentication error. Make sure you’re using the password created using smbpasswd, and not your Linux credentials.
Thank you Gabriel for such a nice tutorial. I got stuck at a point where I had to mount the file on client side, with this error:
sam@samuel:~$ sudo mount //192.168.1.100/home/seun/finance /media/samba -o username=tosin
Password for tosin@//192.168.1.100/home/seun/finance: *****
Retrying with upper case share name
mount error(6): No such device or address
Refer to the mount.cifs(8) manual page (e.g. man mount.cifs)
sam@samuel:~$
sam@samuel:~$ smbclient -L 192.168.1.100
WARNING: The “syslog” option is deprecated
Enter sam’s password:
session setup failed: NT_STATUS_LOGON_FAILURE
sam@samuel:~$
On windows 7, I got access denied error. I followed the steps precisely as stated here. Now I don’t know what wrong steps I have taken here. I will appreciate your response Gabriel. Thank you. Nice one from you
HI Gabriel, I am unable to connect samba share with windows 7 within domain. Is there some extra configuration for this ?
@Gabriel Cánepa, I have followed instruction that mention in the post. it is working for windows 7 but I have not able to join ubuntu 14.04 client on samba domain controller.
@jitendra – OK, good to know that the Samba share is working for Windows 7. That said,
1) Have you installed the samba client packages in the Ubuntu machine? (sudo apt-get install cifs-utils samba-common system-config-samba samba winbind)?
2) Is the Samba server pingable from the Ubuntu machine?
3) Once you’ve checked #1 and #2, run
smbclient -L AAA.BBB.CCC.DDD
in your Ubuntu machine
(where AAA.BBB.CCC.DDD is the IP of your Samba server)
Do you get an error? What is it?
@Gabriel – Thanks for reply I have installed all necessary software , samba server is pingable with domain name “iq.maths.lab” and IP address. After running smbclient -L IP address and domain name .
Output :
root@fs:/home/fs# smbclient -L 192.168.1.181
WARNING: The “syslog” option is deprecated
Enter root’s password:
Domain=[SAMBADOMAIN] OS=[Unix] Server=[Samba 3.6.23-35.el6_8]
Sharename Type Comment
——— —- ——-
IPC$ IPC IPC Service (Samba PDC)
Domain=[SAMBADOMAIN] OS=[Unix] Server=[Samba 3.6.23-35.el6_8]
Server Comment
——— ——-
SAMBAPDC Samba PDC
SMB-PC
Workgroup Master
——— ——-
FUTURESCAPE DCFS
SAMBADOMAIN SAMBAPDC
WORKGROUP TOSHIBA-LPT
root@fs:/home/fs# smbclient -L iq.maths.lab
WARNING: The “syslog” option is deprecated
Enter root’s password:
Domain=[SAMBADOMAIN] OS=[Unix] Server=[Samba 3.6.23-35.el6_8]
Sharename Type Comment
——— —- ——-
IPC$ IPC IPC Service (Samba PDC)
Domain=[SAMBADOMAIN] OS=[Unix] Server=[Samba 3.6.23-35.el6_8]
Server Comment
——— ——-
SAMBAPDC Samba PDC
SMB-PC
Workgroup Master
——— ——-
FUTURESCAPE DCFS
SAMBADOMAIN SAMBAPDC
WORKGROUP TOSHIBA-LPT
root@fs:/home/fs#
What I do next
how to add ubuntu 14.04 in samba controller centos 6.7
@jitendra,
Did you follow the steps provided above? Please confirm and let us know where you got stuck and we can build from there.
restorecon -R -v /finance
Very nice tutorial Gabriel.
Great article. Thanks.
If you don’t want to allow exec perms over file then you must modify finance section like this
[finance]
comment=Directory for collaboration of the company’s finance team
browsable=yes
path=/finance
public=no
valid users=@finance
write list=@finance
writeable=yes
create mask = 0660
directory mask = 0770
force create mode = 0660
force directory mode = 0770
Hi,
Very nice article…
thanks a lot
@Jalal,
Thank you for taking the time to read this article and for your kind words. I appreciate it. Stay tuned for more of my articles in Tecmint.com!
Interesting I have learnt something
@Bob,
I am glad to hear that. What did you learn after reading this article? I hope you enjoyed reading it as much as I did while writing it.
Hi Gabriel I followed the same step but when i try to to access the file through the local host it says failed to start smb service but i started the smb service as well as in the firewall i have allowed smb service. I am confused in the smb.conf configuration i have added all the lines which u have mentioned in the last line of the conf file. but still not able to start,Can u help me out?
@rahul,
Of course I am more than glad to help! :)
What distribution and version are you using? (That is important to find the log location in order to find out more information). Have you installed both the server and client Samba packages?
In case you are using a distro with systemd, what does ‘journalctl -xe’ and ‘systemctl -l status smb’ AFTER starting the service?