This tutorial will cover some basic daily commands you need to use in order to manage Samba4 AD Domain Controller infrastructure, such as adding, removing, disabling or listing users and groups.
We’ll also take a look on how to manage domain security policy and how to bind AD users to local PAM authentication in order for AD users to be able to perform local logins on Linux Domain Controller.
Requirements
- Create an AD Infrastructure with Samba4 on Ubuntu 16.04 – Part 1
- Manage Samba4 Active Directory Infrastructure from Windows10 via RSAT – Part 3
- Manage Samba4 AD Domain Controller DNS and Group Policy from Windows – Part 4
Step 1: Manage Samba AD DC from Command Line
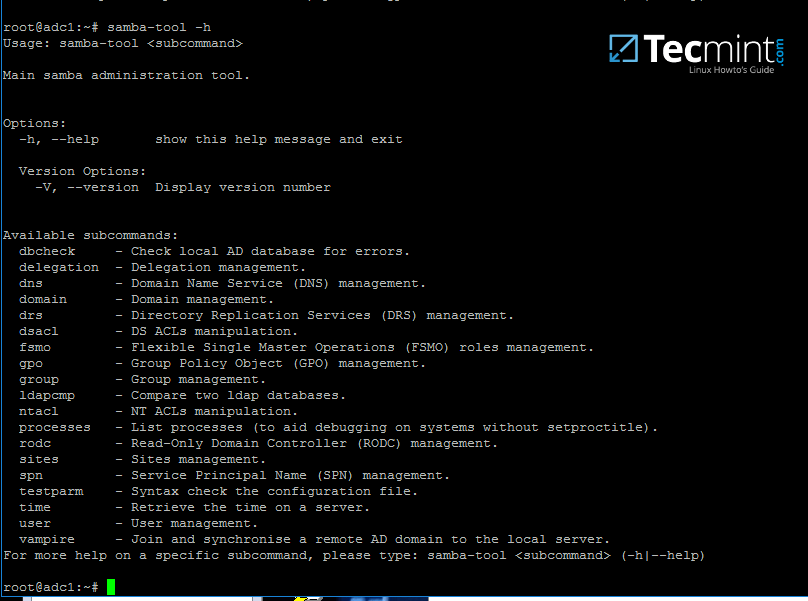
1. Samba AD DC can be managed through samba-tool command line utility which offers a great interface for administrating your domain.
With the help of samba-tool interface you can directly manage domain users and groups, domain Group Policy, domain sites, DNS services, domain replication and other critical domain functions.
To review the entire functionality of samba-tool just type the command with root privileges without any option or parameter.
# samba-tool -h
2. Now, let’s start using samba-tool utility to administer Samba4 Active Directory and manage our users.
In order to create a user on AD use the following command:
# samba-tool user add your_domain_user
To add a user with several important fields required by AD, use the following syntax:
--------- review all options --------- # samba-tool user add -h # samba-tool user add your_domain_user --given-name=your_name --surname=your_username [email protected] --login-shell=/bin/bash

3. A listing of all samba AD domain users can be obtained by issuing the following command:
# samba-tool user list

4. To delete a samba AD domain user use the below syntax:
# samba-tool user delete your_domain_user
5. Reset a samba domain user password by executing the below command:
# samba-tool user setpassword your_domain_user
6. In order to disable or enable an samba AD User account use the below command:
# samba-tool user disable your_domain_user # samba-tool user enable your_domain_user
7. Likewise, samba groups can be managed with the following command syntax:
--------- review all options --------- # samba-tool group add –h # samba-tool group add your_domain_group
8. Delete a samba domain group by issuing the below command:
# samba-tool group delete your_domain_group
9. To display all samba domain groups run the following command:
# samba-tool group list
10. To list all the samba domain members in a specific group use the command:
# samba-tool group listmembers "your_domain group"
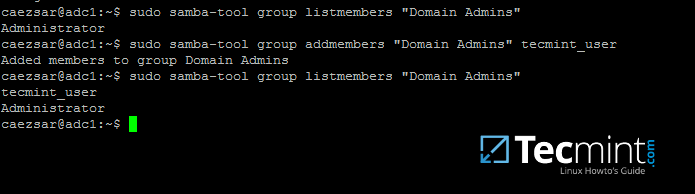
11. Adding/Removing a member from a samba domain group can be done by issuing one of the following commands:
# samba-tool group addmembers your_domain_group your_domain_user # samba-tool group remove members your_domain_group your_domain_user
12. As mentioned earlier, samba-tool command line interface can also be used to manage your samba domain policy and security.
To review your samba domain password settings use the below command:
# samba-tool domain passwordsettings show
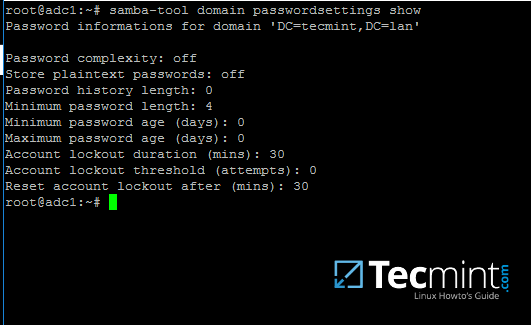
13. In order to modify samba domain password policy, such as the password complexity level, password ageing, length, how many old password to remember and other security features required for a Domain Controller use the below screenshot as a guide.
---------- List all command options ---------- # samba-tool domain passwordsettings -h

Never use the password policy rules as illustrated above on a production environment. The above settings are used just for demonstration purposes.
Step 2: Samba Local Authentication Using Active Directory Accounts
14. By default, AD users cannot perform local logins on the Linux system outside Samba AD DC environment.
In order to login on the system with an Active Directory account you need to make the following changes on your Linux system environment and modify Samba4 AD DC.
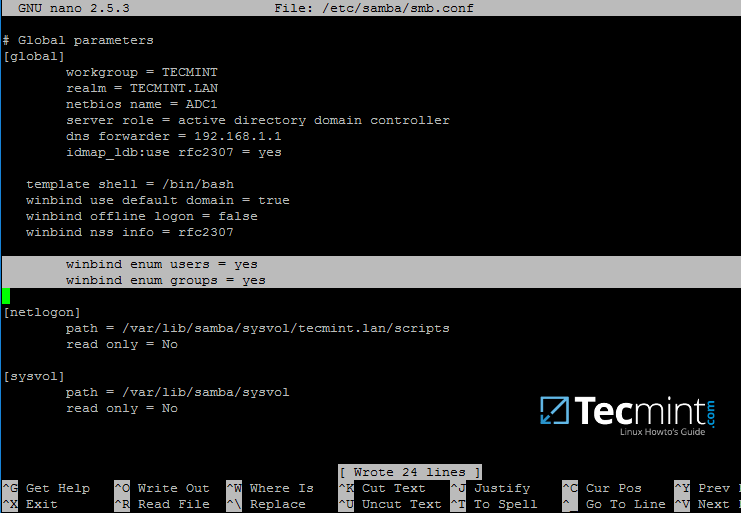
First, open samba main configuration file and add the below lines, if missing, as illustrated on the below screenshot.
$ sudo nano /etc/samba/smb.conf
Make sure the following statements appear on the configuration file:
winbind enum users = yes winbind enum groups = yes
15. After you’ve made the changes, use testparm utility to make sure no errors are found on samba configuration file and restart samba daemons by issuing the below command.
$ testparm $ sudo systemctl restart samba-ad-dc.service

16. Next, we need to modify local PAM configuration files in order for Samba4 Active Directory accounts to be able to authenticate and open a session on the local system and create a home directory for users at first login.
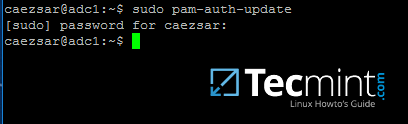
Use the pam-auth-update command to open PAM configuration prompt and make sure you enable all PAM profiles using [space] key as illustrated on the below screenshot.
When finished hit [Tab] key to move to Ok and apply changes.
$ sudo pam-auth-update

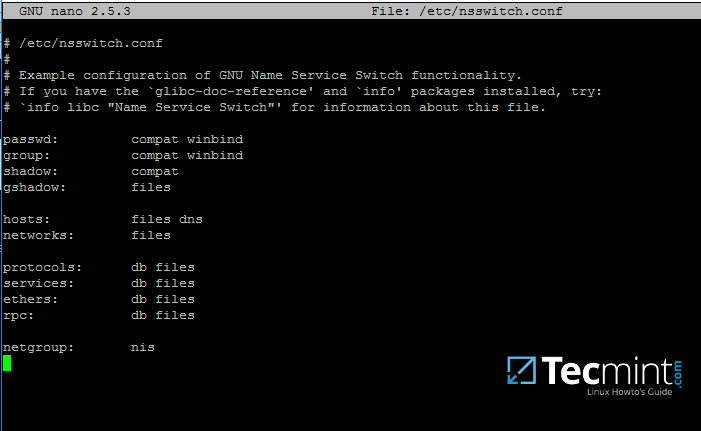
17. Now, open /etc/nsswitch.conf file with a text editor and add winbind statement at the end of the password and group lines as illustrated on the below screenshot.
$ sudo vi /etc/nsswitch.conf
18. Finally, edit /etc/pam.d/common-password file, search for the below line as illustrated on the below screenshot and remove the use_authtok statement.
This setting assures that Active Directory users can change their password from command line while authenticated in Linux. With this setting on, AD users authenticated locally on Linux cannot change their password from console.
password [success=1 default=ignore] pam_winbind.so try_first_pass
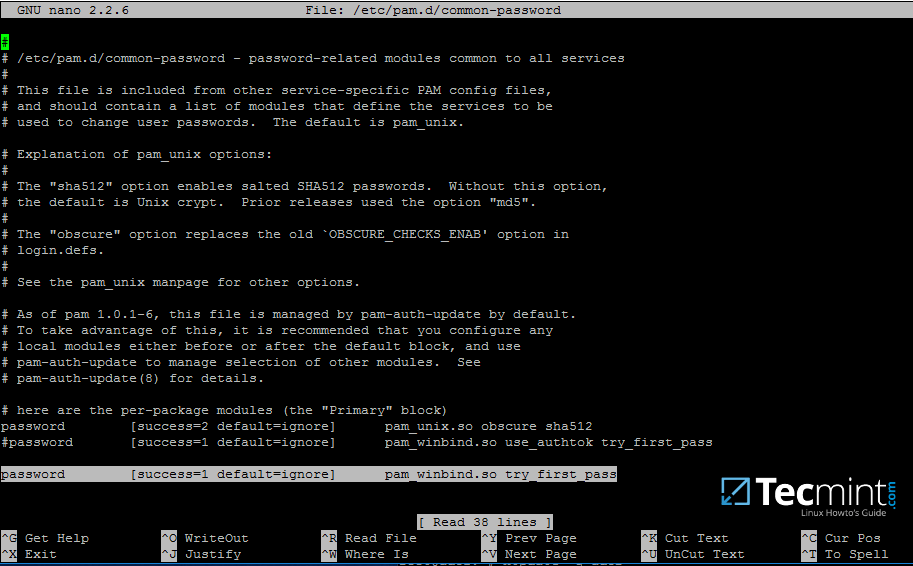
Remove use_authtok option each time PAM updates are installed and applied to PAM modules or each time you execute pam-auth-update command.
19. Samba4 binaries comes with a winbindd daemon built-in and enabled by default.
For this reason you’re no longer required to separately enable and run winbind daemon provided by winbind package from official Ubuntu repositories.
In case the old and deprecated winbind service is started on the system make sure you disable it and stop the service by issuing the below commands:
$ sudo systemctl disable winbind.service $ sudo systemctl stop winbind.service
Although, we no longer need to run old winbind daemon, we still need to install Winbind package from repositories in order to install and use wbinfo tool.
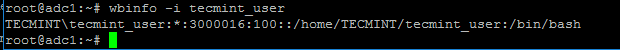
Wbinfo utility can be used to query Active Directory users and groups from winbindd daemon point of view.
The following commands illustrates how to query AD users and groups using wbinfo.
$ wbinfo -g $ wbinfo -u $ wbinfo -i your_domain_user

20. Apart from wbinfo utility you can also use getent command line utility to query Active Directory database from Name Service Switch libraries which are represented in /etc/nsswitch.conf file.
Pipe getent command through a grep filter in order to narrow the results regarding just your AD realm user or group database.
# getent passwd | grep TECMINT # getent group | grep TECMINT

Step 3: Login in Linux with an Active Directory User
21. In order to authenticate on the system with a Samba4 AD user, just use the AD username parameter after su - command.
At the first login a message will be displayed on the console which notifies you that a home directory has been created on /home/$DOMAIN/ system path with the mane of your AD username.
Use id command to display extra information about the authenticated user.
# su - your_ad_user $ id $ exit

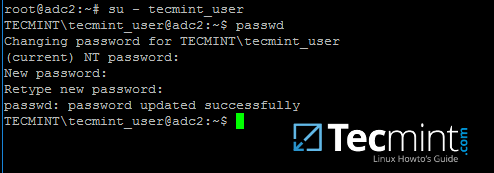
22. To change the password for an authenticated AD user type passwd command in console after you have successfully logged into the system.
$ su - your_ad_user $ passwd
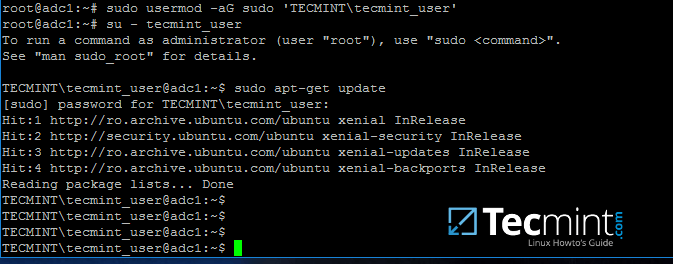
23. By default, Active Directory users are not granted with root privileges in order to perform administrative tasks on Linux.
To grant root powers to an AD user you must add the username to the local sudo group by issuing the below command.
Make sure you enclose the realm, slash and AD username with single ASCII quotes.
# usermod -aG sudo 'DOMAIN\your_domain_user'
To test if AD user has root privileges on the local system, login and run a command, such as apt-get update, with sudo permissions.
# su - tecmint_user $ sudo apt-get update
24. In case you want to add root privileges for all accounts of an Active Directory group, edit /etc/sudoers file using visudo command and add the below line after root privileges line, as illustrated on the below screenshot:
%DOMAIN\\your_domain\ group ALL=(ALL:ALL) ALL
Pay attention to sudoers syntax so you don’t break things out.
Sudoers file doesn’t handles very well the use of ASCII quotation marks, so make sure you use % to denote that you’re referring to a group and use a backslash to escape the first slash after the domain name and another backslash to escape spaces if your group name contains spaces (most of AD built-in groups contain spaces by default). Also, write the realm with uppercases.

That’s all for now! Managing Samba4 AD infrastructure can be also achieved with several tools from Windows environment, such as ADUC, DNS Manager, GPM or other, which can be obtained by installing RSAT package from Microsoft download page.
To administer Samba4 AD DC through RSAT utilities, it’s absolutely necessary to join the Windows system into Samba4 Active Directory. This will be the subject of our next tutorial, till then stay tuned to TecMint.


Hello All,
Anyone knows, why when I´m trying to create a new user, I get /bin/false on the login shell, I already try to modify it, and I can´t log in on the Linux host.
LUXSOLUCIONES\administrator:*:0:100::/home/LUXSOLUCIONES/administrator:/bin/false
LUXSOLUCIONES\cnarvaezhz:*:3000016:100::/home/LUXSOLUCIONES/cnarvaezhz:/bin/false
LUXSOLUCIONES\luxadmin:*:3000044:100::/home/LUXSOLUCIONES/luxadmin:/bin/false
I use this command to add another new user, and get the same result:
root@svuadc2lux:~# samba-tool user add luxadmin --given-name="System" --surname="Administrator" --login-shell=/bin/bash
when i check the samba DB i get this:
Sample Output
You really should add more warnings for editing the sudoers file.
If it breaks sudo stops working, which probably means that it is non-trivial to fix the problem.
Basically you should always keep the file you are editing open, save it without closing it and try to log in from another terminal and check that sudo access still works before closing the file.
It’s very easy to introduce a syntax error somewhere and suddenly not have any root access, with today’s systems often running without access to a root-password you will have to boot into the single-user mode or a rescue-disk to solve the problem.
If you get this error: no directory logging in with
home=/.You can also modify /etc/pam.d/common-session to make it so that a user’s home directory will be created on the first login.
Add the following line to that file.
session required pam_mkhomedir.soThis is particularly useful if your system is on a network where the users are managed externally to your machine, by LDAP for instance.
Hello, I have a problem, when I create a user
root@server:~# samba-tool user create teste.testeNew Password:
Retype Password:
User ‘teste.teste’ created successfully
root@server:~# su - teste.testeNo passwd entry for user ‘teste.teste’
Found my error:
Check /etc/nsswitch.conf:
Hello,
I am Wilford and I have a hard time if you can help me it will be very good.
My case is as follows: I am tasked with integrating Linux (Ubuntu 19.04) into AD (Windows 2012) and can do very well through samba, but meanwhile, users are unable to log in outside the company’s internal network.
NOTE: I already tried the command winbind offline logon = true
This is a great tutorial
You should indicate how to add an organizational unit. That would be nice. Most of the samba-tool doesn’t work and their documentation sucks which is why people use other products.
Hi TecMint,
Is it possible join samba4 AD with ldap as backend ?
thank you
As mentioned above default shell for all user is /bin/false instead of /bin/bash.
Please let me know how can i update it.
resolve by adding below in smb.conf
template shell = /bin/sh
Thanks for the very useful article. I would like to know how to set the user password expiration warning (number of days) with samba-tool? Can we set it in domain level?
See point 13. Use samba-tool domain passwordsettings -h to see options and set expire warning.
There is no such option when use the command “samba-tool domain passwordsettings -h “. Seems Samba 4 doesn’t have the option.
Try to search deep through pdbedit command. Use pdbedit -u your_user -v to see user properties.
Can i get home directory where first login on samba via windows machine?
I can see my homes where login with user ad-dc, but i can access it because actually homes directory didn’t create on Linux server. home user actually create where i login direct Linux use command.
This input/output for example :
Thanks!
That’s the normal behaviour to create a home directory for a user when you first log on onto the Linux machine.
How can I change home directory “/home/$DOMAIN” ?
I would like to use, my own.
Thanks!
Why you need to change standard path from /home to other path? It can be done by editing smb.conf file and the following statement:
template homedir = /your/path/%D/%U
where %D represents the domain part and %U the username part.
Well the point is, when user is created, user home dir is created in the /home/domain/user.
I would like to use something diferent, like /srv/samba/homes/%U.
Thanks!
thanks for the tutorial. I can’t get the last part working “Login in Linux with an Active Directory User” because the su and id command do not find the users. The getent command is working… Any ideas ?
Thanks
Maybe you should precede the username with the domain part, such as: DOMAIN\your_domain_user
This is not working :
Ok now : the issue was due to not reloading the cache : service nscd restart
Why do you have only modify /etc/pam.d/common-password file and not /etc/pam.d/common-account, /etc/pam.d/common-auth, /etc/pam.d/common-session ?
Thanks for your response.
# getent passwd | grep TECMINT
# getent group | grep TECMINT
These lines are not functional because we must add these lines in /etc/samba/smb.conf
winbind enum users = yes
winbind enum groups = yes
On the next series of tutorials we will cover integrating Linux and Windows machines into Samba4 AD DC.
It is A nice tutorial. I’m curious about joining linux machine to samba4 active directory controller.
Please put more information which setting is in client section/side and which one is in server section/side.