9. Now it’s time to create the encrypted partition that will be the physical volume for encryption on top of which the LVM /var and /home partition will reside.
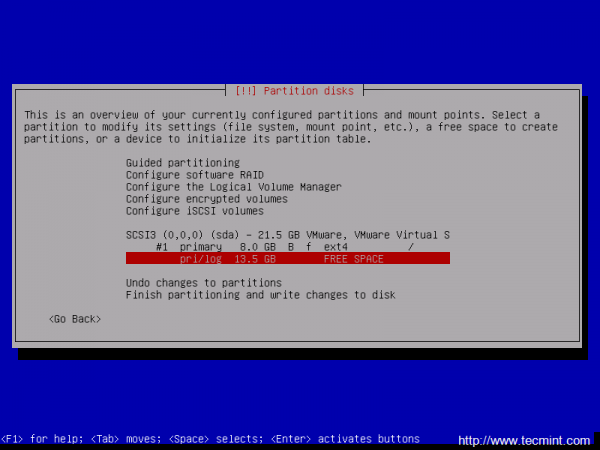
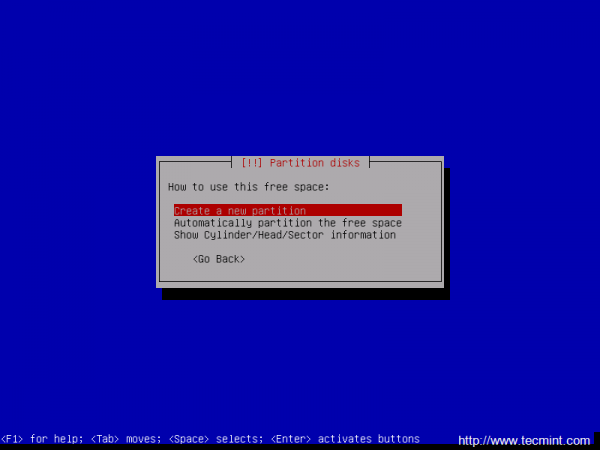
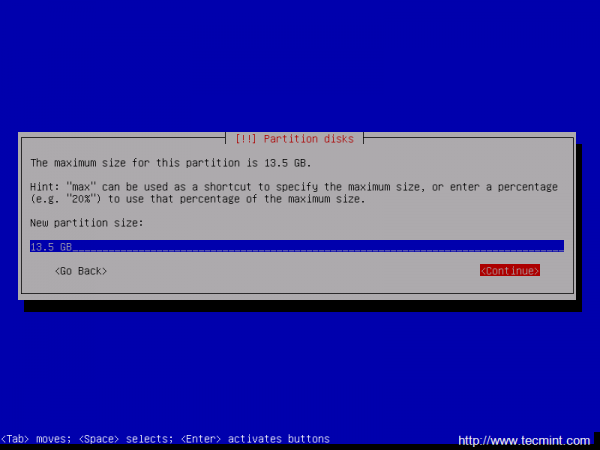
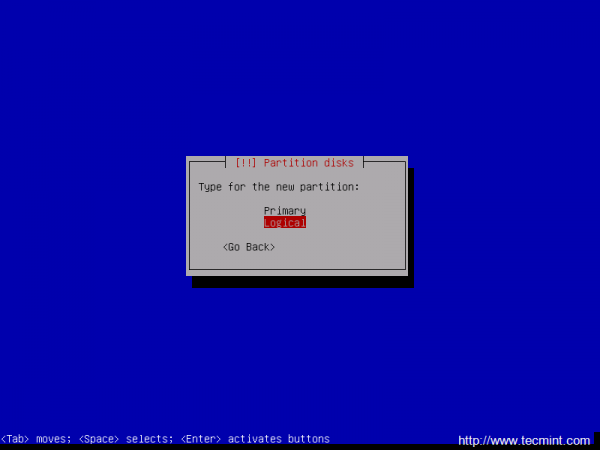
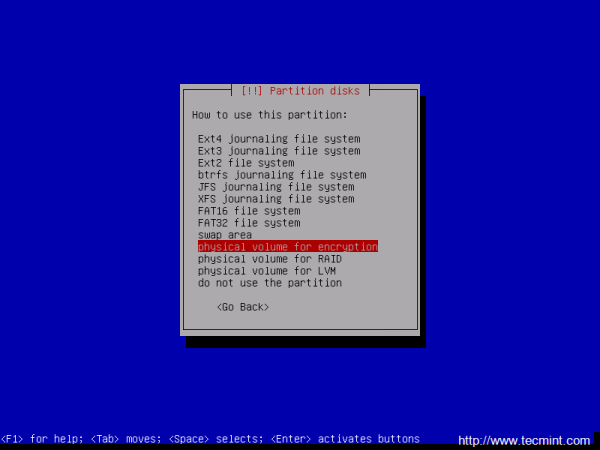
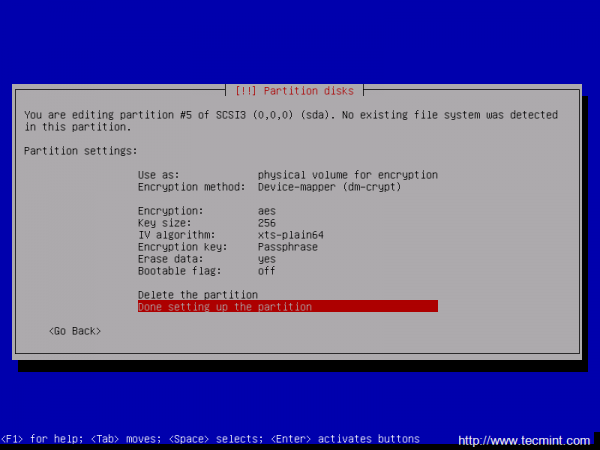
To do that, first choose the remaining FREE SPACE -> Create a new partition -> leave the partition size with the default value -> make it a Logical partition -> Use it as Physical volume for encryption -> Done setting up the partition.
Use the below screenshots as a guidance for this steps.
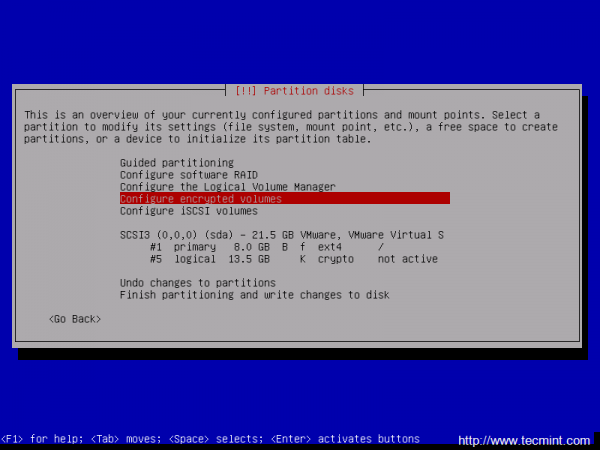
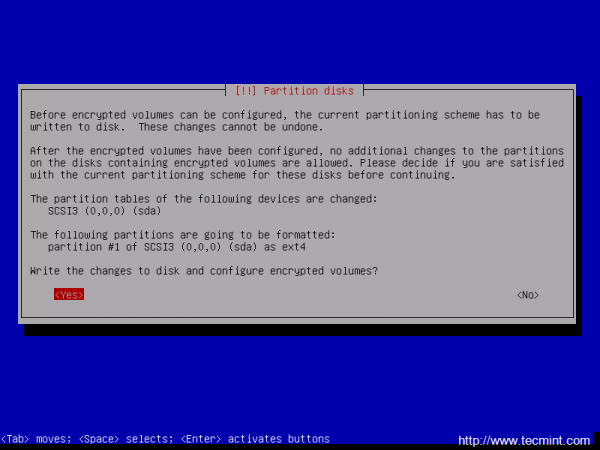
10. After the Physical volume for encryption has been created it’s time to configure the Encrypted volumes. If you have other partitions or hard drives that you want to use for encryption, now it’s time to create them all by repeating the above steps for each partition on hard drives.
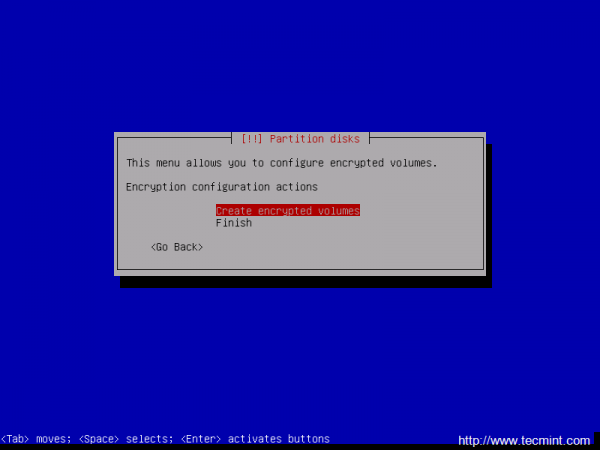
To move forward, next select Configure encrypted volumes and hit on Yes to write the changes to disk and start configure encrypted volumes.
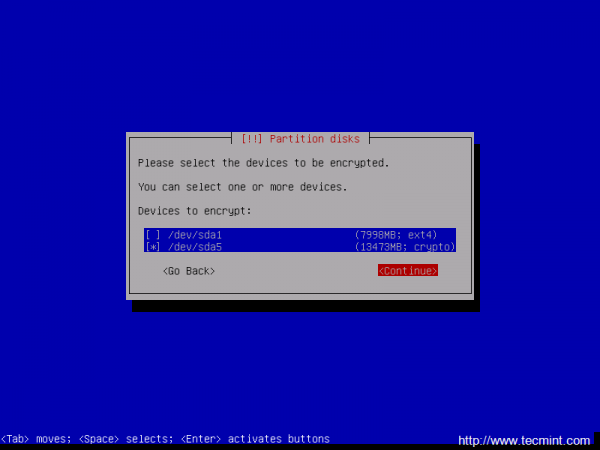
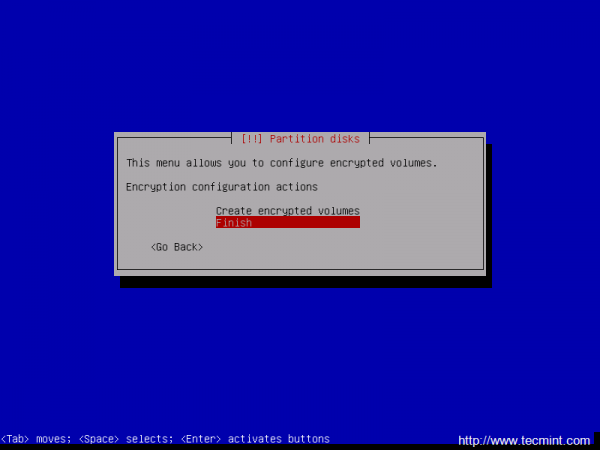
11. On the next screen choose Create encrypted volumes and choose the devices (partitions) to encrypt. If you have a hard time to recognize the correct devices that will be used for encryption after their partition number or size, just look after a crypto word at the end of each listed partition.
To select the partitions use up and down keys to navigate and press the space key to select the appropriate partitions and an asterisk should appear on the selected device. When you’re done with devices selection, hit the Tab key to jump on Continue and press Enter key to move forward and Finish.
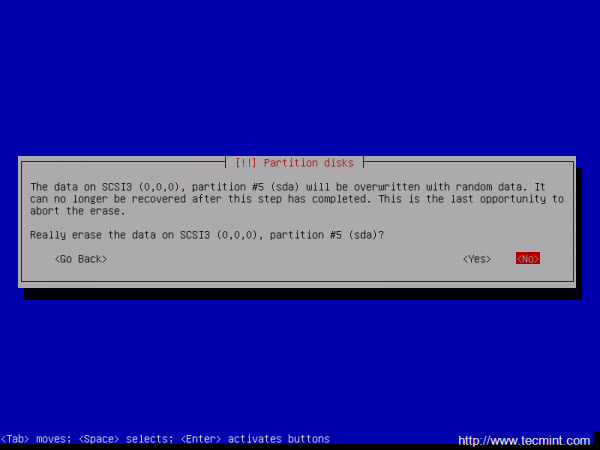
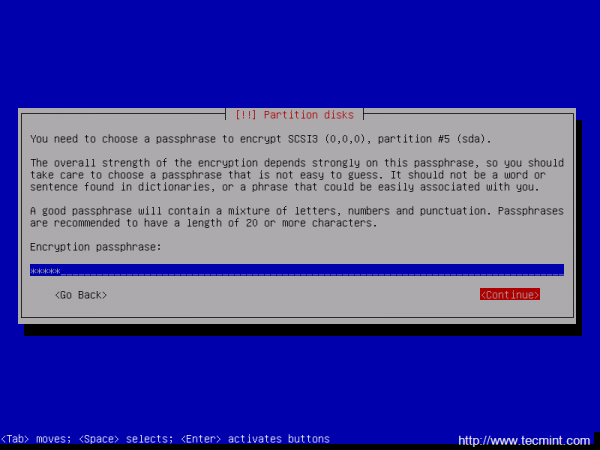
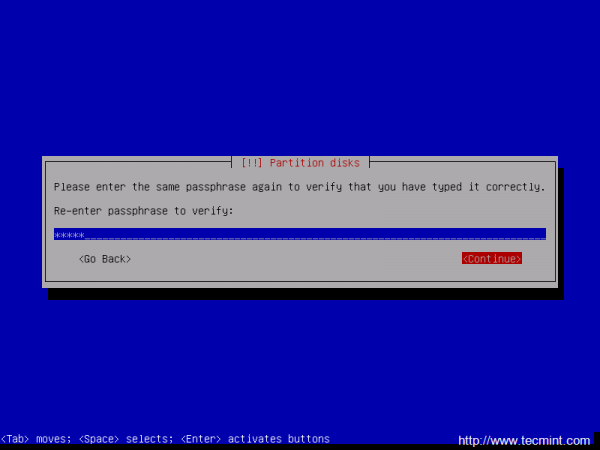
12. On the next screen the installer will ask you whether you want to erase the data on the encrypted partitions. Depending on your available time or if the hard disk it’s new and has just been partitioned, so it does not contain any data, choose No and provide a strong passphrase for the encrypted volume.
When you’re done with the passphrases hit Continue to return to main Partition menu and configure LVM volumes further.
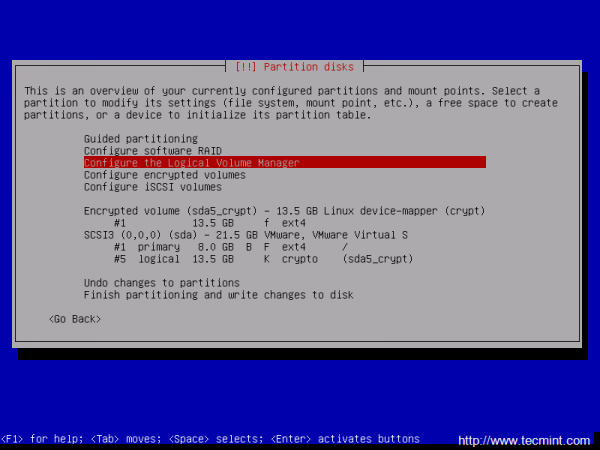
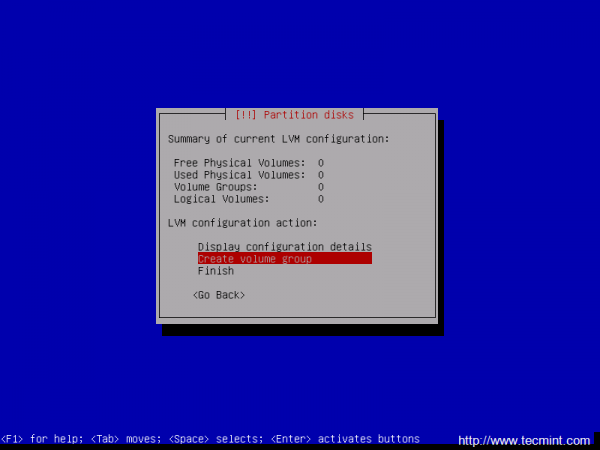
13. Once you have returned at the main Partition menu, it’s time to create the LVM partitions for /home and /var on top of the encrypted volume.
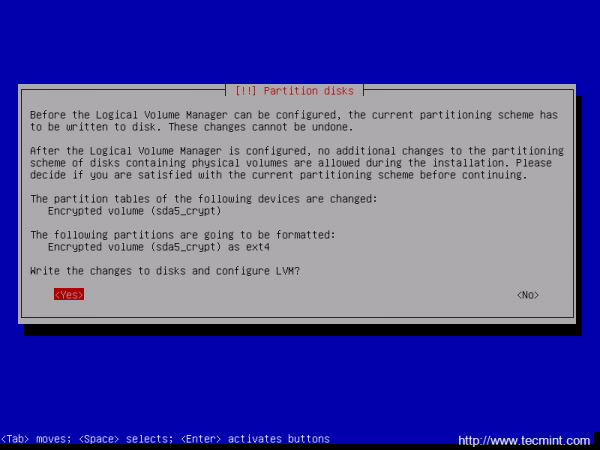
Next, select Configure the Logical Volume Manager and confirm (Yes) the new write changes to disk.
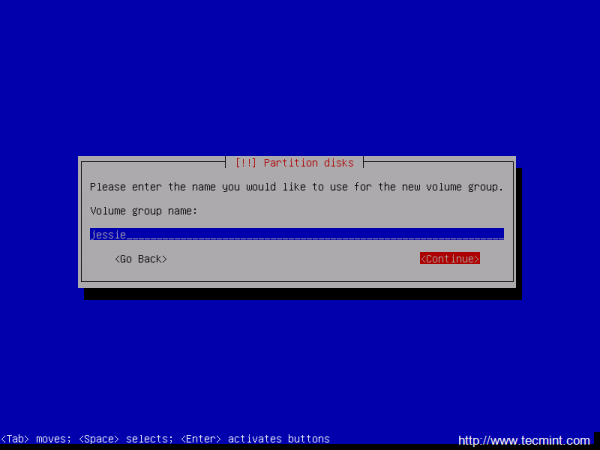
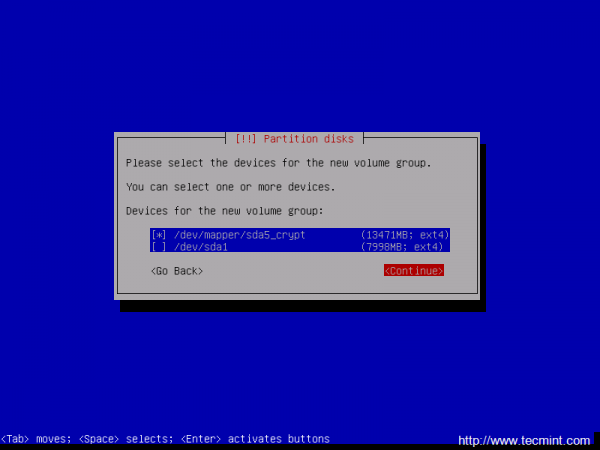
14. On the next step create a Volume Group using a descriptive name for this VG (for my setup I’ve used the name Jessie) and select the encrypted device (partition) that will be a part of the VG by pressing the space key. To jump to Continue menu press the Tab key.



hi guys
i want to know how to make passpshrase to automaticaly boot from usb.
Yeah, I’m not convinced automatic decryption works in Debian. If you issue ‘update-initramfs -u -k all’ you get the error, ‘cryptsetup: WARNING: target sdaX_crypt uses a key file, skipped.’ which will hang the system at boot.
https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=776409
They’re dicking around with systemd and can’t get it sorted out so it isn’t clear if you can use a keyscript in Jessie/Stable.
>All sensitive data stored in /home and /var partitions will be highly secured in case someone gains physical access to your machine hard-drive.
I’m sorry, how exactly is it gonna be secured from anyone when we’ve just configured these partitions to be mounted automatically without asking the passphrase so anyone will be able to login on our machine and read all the data from these partitions?
That’s just a simple trick used to decrypt the partitions. I wouldn’t suggest that you should host the key on any of internal hard-disks but you can use an external drive to keep the key secure and plug the drive.
If you can boot-up and login to the console check if the / partition is present on fstab (i’m guessing the root partition is not encrypted). Then update the initramfs image with the command ‘update-initramfs -u’
Hi, after “update-initramfs -u -k all” the system won’t boot anymore with the error “Unable to find LVM volume hostname-vg/root”. Without that command the passphrase as still asked at boot. Do I need to add anything to /etc/fstab?
Any other suggestion?
put the key on usb stick :)
After step 25 (add the key to encrypted LUKS device and enter the passphrase) the key is not be added to the slot, but I get a message “Failed to open key file”.
All previous steps went flawless.
What went wrong?
Check permissions on /root/cryptkey file.
Hi,
After the last step, to make the system use the key file, I had to :
update-initramfs -u -k all
WIthout this command, the passphrase was still asked at boot time.
But I’m really wondering… how is it secure to store the key on disk, in the case someone get physical access to your hard drive? If I do this on a netbook, and someone steal it, will he be able to unlock the crypted volume after he found this key file??
Thanks for the tutorial!
Mate, you describe the creation of dm-crypt containers, which are not really LUKS. Try changing the pasword on the volume you create (a trivial operation for LUKS), and let us know how it worked.
“All sensitive data stored in /home and /var partitions will be highly secured in case someone gains physical access to your machine hard-drive.”
–> huummm , seriously ?
@Lemoidului,
Yes, what’s wrong here? /home contains important user data and /var contains important server logs, these two partitions needs to be secured..Instead finding out errors in the article, appreciate the author for his work hard..
IMHO, having a encrypted partition with the encryption key stored in a clear text partition by its side, is useless. A false sense of security.
Couldn’t agree more. I can decrypt your drives in 60 seconds if you store decryption key that way.
This is just a very simple and convenient trick to automatically decrypt and load the encrypted volume in case you don’t have any physical access to the machine or it’s impossible to access or tamper with the boot sequence in order to manually supply the passphrase.
@Chris: Check if the key has been added to the encrypted device slot by issuing cryptsetup luksDump command.Also, and verify the content of /etc/crypttab file and ensure that the correct key with absolute path has been added.
” Failed to open key file. ”
So whan next?
Sorry if I missed something, but… what’s the point of having a encrypted partition and storing the encryption password in a unencrypted partition?