By its original design, FTP (File Transfer Protocol) is not secure, meaning it doesn’t encrypt data being transmitted between two machines, along with user’s credentials. This poses a massive threat to data as well as server security.
In this tutorial, we will explain how to manually enable data encryption services in a FTP server in CentOS/RHEL 7 and Fedora; we will go through various steps of securing VSFTPD (Very Secure FTP Daemon) services using SSL/TLS certificates.
Prerequisites:
- You must have installed and configured a FTP server in CentOS 7
Before we start, note that all the commands in this tutorial will be run as root, otherwise, use the sudo command to gain root privileges if you are not controlling the server using the root account.
Step 1. Generating SSL/TLS Certificate and Private Key
1. We need to start by creating a subdirectory under: /etc/ssl/ where we will store the SSL/TLS certificate and key files:
# mkdir /etc/ssl/private
2. Then run the command below to create the certificate and key for vsftpd in a single file, here is the explanation of each flag used.
- req – is a command for X.509 Certificate Signing Request (CSR) management.
- x509 – means X.509 certificate data management.
- days – defines number of days certificate is valid for.
- newkey – specifies certificate key processor.
- rsa:2048 – RSA key processor, will generate a 2048 bit private key.
- keyout – sets the key storage file.
- out – sets the certificate storage file, note that both certificate and key are stored in the same file: /etc/ssl/private/vsftpd.pem.
# openssl req -x509 -nodes -keyout /etc/ssl/private/vsftpd.pem -out /etc/ssl/private/vsftpd.pem -days 365 -newkey rsa:2048
The above command will ask you to answer the questions below, remember to use values that apply to your scenario.
Country Name (2 letter code) [XX]:IN State or Province Name (full name) []:Lower Parel Locality Name (eg, city) [Default City]:Mumbai Organization Name (eg, company) [Default Company Ltd]:TecMint.com Organizational Unit Name (eg, section) []:Linux and Open Source Common Name (eg, your name or your server's hostname) []:tecmint Email Address []:[email protected]
Step 2. Configuring VSFTPD To Use SSL/TLS
3. Before we perform any VSFTPD configurations, let’s open the ports 990 and 40000-50000 to allow TLS connections and the port range of passive ports to define in the VSFTPD configuration file respectively:
# firewall-cmd --zone=public --permanent --add-port=990/tcp # firewall-cmd --zone=public --permanent --add-port=40000-50000/tcp # firewall-cmd --reload
4. Now, open the VSFTPD config file and specify the SSL details in it:
# vi /etc/vsftpd/vsftpd.conf
Look for the option ssl_enable and set its value to YES to activate the use of SSL, in addition, since TSL is more secure than SSL, we will restrict VSFTPD to employ TLS instead, using the ssl_tlsv1_2 option:
ssl_enable=YES ssl_tlsv1_2=YES ssl_sslv2=NO ssl_sslv3=NO
5. Then, add the lines below to define the location of the SSL certificate and key file:
rsa_cert_file=/etc/ssl/private/vsftpd.pem rsa_private_key_file=/etc/ssl/private/vsftpd.pem
6. Next, we have to prevent anonymous users from using SSL, then force all non-anonymous logins to use a secure SSL connection for data transfer and to send the password during login:
allow_anon_ssl=NO force_local_data_ssl=YES force_local_logins_ssl=YES
7. In addition, we can add the options below to boost up FTP server security. When option require_ssl_reuse is set to YES, then, all SSL data connections are required to exhibit SSL session reuse; proving that they know the same master secret as the control channel.
Therefore, we have to turn it off.
require_ssl_reuse=NO
Again, we need to select which SSL ciphers VSFTPD will permit for encrypted SSL connections with the ssl_ciphers option. This can greatly limit efforts of attackers who try to force a particular cipher which they probably discovered vulnerabilities in:
ssl_ciphers=HIGH
8. Now, set the port range (min and max port) of passive ports.
pasv_min_port=40000 pasv_max_port=50000
9. Optionally, allow SSL debugging, meaning openSSL connection diagnostics are recorded to the VSFTPD log file with the debug_ssl option:
debug_ssl=YES
Save all the changes and close the file. Then let’s restart VSFTPD service:
# systemctl restart vsftpd
Step 3: Testing FTP server With SSL/TLS Connections
10. After doing all the above configurations, test if VSFTPD is using SSL/TLS connections by attempting to use FTP from the command line as follows:
# ftp 192.168.56.10 Connected to 192.168.56.10 (192.168.56.10). 220 Welcome to TecMint.com FTP service. Name (192.168.56.10:root) : ravi 530 Non-anonymous sessions must use encryption. Login failed. 421 Service not available, remote server has closed connection ftp>

From the screen shot above, we can see that there is an error informing us that VSFTPD can only allow user to login from clients that support encryption services.
The command line does not offer encryption services thus producing the error. So, to securely connect to the server, we need a FTP client that supports SSL/TLS connections such as FileZilla.
Step 4: Install FileZilla to Securely Connect to a FTP Server
11. FileZilla is a modern, popular and importantly cross-platform FTP client that supports SSL/TLS connections by default.
To install FileZilla in Linux, run the command below:
--------- On CentOS/RHEL/Fedora --------- # yum install epel-release filezilla --------- On Debian/Ubuntu --------- $ sudo apt-get install filezilla
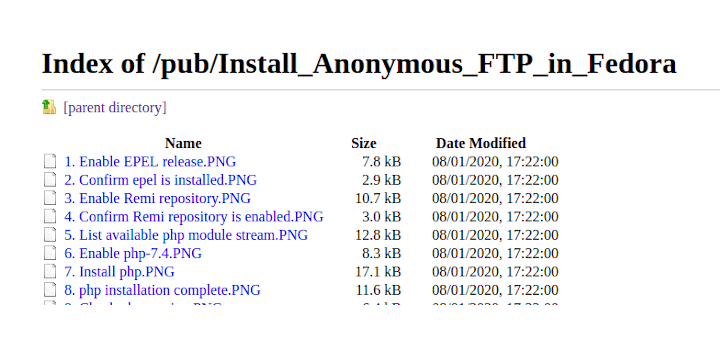
12. When the installation completes (or else if you already have it installed), open it and go to File=>Sites Manager or (press Ctrl+S) to get the Site Manager interface below.
Click on New Site button to add a new site/host connection details.

13. Next, set the host/site name, add the IP address, define the protocol to use, encryption and logon type as in the screen shot below (use values that apply to your scenario):
Host: 192.168.56.10 Protocol: FTP – File Transfer Protocol Encryption: Require explicit FTP over #recommended Logon Type: Ask for password #recommended User: username

14. Then click on Connect to enter the password again, and then verify the certificate being used for the SSL/TLS connection and click OK once more to connect to the FTP server:

At this stage, we should have logged successfully into the FTP server over a TLS connection, check the connection status section for more information from the interface below.

15. Last but not least, try transferring files from the local machine to the FTP sever in the files folder, take a look at the lower end of the FileZilla interface to view reports concerning file transfers.

That’s all! Always keep in mind that FTP is not secure by default, unless we configure it to use SSL/TLS connections as we showed you in this tutorial. Do share your thoughts about this tutorial/topic via the feedback form below.


Getting errors. Looking for help. Can buy you a coffee & lunch. Thanks.
@Ravi,
What errors are you getting? could you share here?
Putting the private key and the certificate in the same storage file may not be safe. what do you think?
Great article!
One question, how to regenerate the certificate once it expired?
Many thanks.
@Oppa
Just follow the same steps in the article.
If I want to open on browser, it’s showing “530 Non-anonymous sessions must use encryption“. I know you have discussed this and given solution to open over Filezilla. Is their any way to open the connection securely over browser
@sivatheja
We have to do a little research on this, i mean connecting securely over a browser to your vsftp server. But for the mean time, consider using the solution we have provided, that way, all your connections will be secure.
Once we find a way, we will keep you posted. Thanks for the feedback.
Dear Aaron,
Great article.
I did all steps but unfortunately Filezilla says it can’t retrieve directory listing when connecting to the FTP server. Do you have any idea what could be wrong? I’m installing on Fedora 25 Server.
@Jasper
Hope you enjoyed it! Try to enable proper permissions for the connected user’s ftp directory. Follow How to Install, Configure and Secure FTP Server in CentOS 7 – [Comprehensive Guide] to do this.
Something like this:
# mkdir /home/ravi/ftp/files
# chown ravi:ravi /home/ravi/ftp/files
# chmod 0700 /home/ravi/ftp/files/
Thanks for appreciating out work. In case it doesn’t work, get back to us.
Dear Aaron
Thanks for sharing above article, I felt very useful. I followed the instruction and everything went smoothly, while I try to connect using FileZilla showing an error “Error: GnuTLS error -15: An unexpected TLS packet was received. Error: Could not connect to server, need your help and I tried with WinSCP software, showing an another error ”
Server asks for authentication with a client certificate.
Using TLSv1.2, cipher TLSv1/SSLv3: DHEGH-RSA-AES256-GCM-SHA384, 2048 bit RSA, DHEGH-RSA-AES256-GCM-SHA384 TLSv1.2 Kx=DHEGH Au=RSA Enc=AESGCM(256) Mac=AEAD
SSL3 alert write: fatal: protocol version
wrong version number
Disconnected from server
Connection failed.
@Haneef
Welcome, thanks for appreciating our work. Try to use SSL/TLS version 1.2 by setting the directives below:
ssl_tlsv1_2=YES
ssl_sslv2=NO
ssl_sslv3=NO
Additionally, if you set the debug option, check out the vsftpd log file for more info.
I am getting the same error and am not sure what to do here, can you help me!
@tedtredzero
Try to upgrade vsftpd to the latest stable version like this:
Then restart the vsftpd service with this command:
yea i had to do something different, this tutorial worked for me to secure the FTP
https://www.youtube.com/watch?v=vpNSZUyuS5U
You can use lftp to securely connect SFTP through linux CUI.
@Vinodh
Okay, many thanks for sharing this with us, we’ll definitely give it a try.