Today, we will be discussing about how to sync files using rsync with non-standard SSH port. You might wonder why do we need to use non-standard SSH port? It is because of security reasons. Everybody knows 22 is the SSH default port.
So, It is mandatory to change your SSH default port number to something different which is very hard to guess. In such cases, how will you sync your files/folders with your Remote server? No worries, It is not that difficult. Here we will see how to sync files and folders using rsync with non-standard SSH port.
As you might know, rsync, also known as Remote Sync, is a fast, versatile, and powerful tool that can be used to copy and sync files/directories from local to local, or local to remote hosts. For more details about rsync, check man pages:
# man rsync
Or refer our previous guide from the link below.
Change SSH Port to Non-standard Port
As we all know, By default rsync uses default SSH port 22 to sync files over local to remote hosts and vice versa. We should change our remote server’s SSH port to tighten the security.
To do this, open and edit the SSH configuration /etc/ssh/sshd_config file:
# vi /etc/ssh/sshd_config
Find the following line. Uncomment and change the port number of your choice. I recommend you to choose any number which is very hard to guess.
Make sure you are using a unique number which is not used by existing services. Check this netstat article to know which services are running on which TCP/UDP ports.
For example, here I use port number 1431.
[...] Port 1431 [...]
Save and close the file.
In RPM based systems such as RHEL, CentOS, and Scientific Linux 7, you need to allow the new port through your firewall or router.
# firewall-cmd --add-port 1431/tcp # firewall-cmd --add-port 1431/tcp --permanent
On RHEL/CentOS/Scientific Linux 6 and above, you should also update selinux permissions to allow the port.
# iptables -A RH-Firewall-1-INPUT -m state --state NEW -m tcp -p tcp --dport 1431 -j ACCEPT # semanage port -a -t ssh_port_t -p tcp 1431
Finally, restart SSH service to take effect the changes.
# systemctl restart sshd [On SystemD] OR # service sshd restart [On SysVinit]
Now let us see how to sync files using rsync with non-standard port.
How to Rsync with non-standard SSH Port
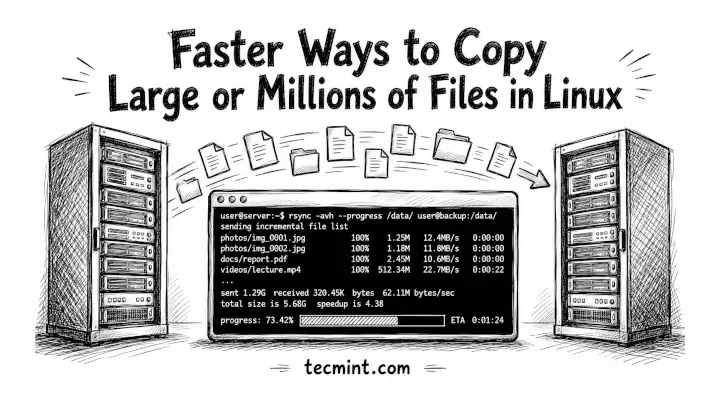
Run the following command from the terminal to sync files/folders using Rsync with non-standard ssh port.
Syntax:
# rsync -arvz -e 'ssh -p <port-number>' --progress --delete user@remote-server:/path/to/remote/folder /path/to/local/folder
For the purpose of this tutorial, I will be using two systems.
Remote System Details:
IP Address: 192.168.1.103 User name: tecmint Sync folder: /backup1
Local System Details:
Operating System: Ubuntu 14.04 Desktop IP Address: 192.168.1.100 Sync folder: /home/sk/backup2
Let us sync the contents of remote server’s /backup1 folder to my local system’s folder /home/sk/backup2/.
$ sudo rsync -arvz -e 'ssh -p 1431' --progress --delete [email protected]:/backup1 /home/sk/backup2
Sample Output
[email protected]'s password: receiving incremental file list backup1/ backup1/linux-headers-4.3.0-040300-generic_4.3.0-040300.201511020949_amd64.deb 752,876 100% 13.30MB/s 0:00:00 (xfr#1, to-chk=2/4) backup1/linux-headers-4.3.0-040300_4.3.0-040300.201511020949_all.deb 9,676,510 100% 12.50MB/s 0:00:00 (xfr#2, to-chk=1/4) backup1/linux-image-4.3.0-040300-generic_4.3.0-040300.201511020949_amd64.deb 56,563,302 100% 11.26MB/s 0:00:04 (xfr#3, to-chk=0/4) sent 85 bytes received 66,979,455 bytes 7,050,477.89 bytes/sec total size is 66,992,688 speedup is 1.00.
Let us check the contents of /backup1/ folder in the remote server.
$ sudo ls -l /backup1/
Sample Output
total 65428 -rw-r--r-- 1 root root 9676510 Dec 9 13:44 linux-headers-4.3.0-040300_4.3.0-040300.201511020949_all.deb -rw-r--r-- 1 root root 752876 Dec 9 13:44 linux-headers-4.3.0-040300-generic_4.3.0-040300.201511020949_amd64.deb -rw-r--r-- 1 root root 56563302 Dec 9 13:44 linux-image-4.3.0-040300-generic_4.3.0-040300.201511020949_amd64.deb
Now, let us check the contents of /backup2/ folder of local system.
$ ls /home/sk/backup2/
Sample Output
backup1
As you see in the above output, the contents of /backup1/ have been successfully copied to my local system’s /home/sk/backup2/ directory.
Verify /backup1/ folder contents:
$ ls /home/sk/backup2/backup1/
Sample Output
linux-headers-4.3.0-040300_4.3.0-040300.201511020949_all.deb linux-image-4.3.0-040300-generic_4.3.0-040300.201511020949_amd64.deb linux-headers-4.3.0-040300-generic_4.3.0-040300.201511020949_amd64.deb
See, both remote and local system’s folders have same files.
Conclusion
Syncing files/folders using Rsync with SSH is not only easy, but also fast and secure method. If you’re behind a firewall that restricts port 22, no worries. Just change the default port and sync files like a pro.



If you get this article then you HAVE to take it to the next level. And yes — there are various ‘better’ ways to change/specify the ssh port and the connection ABSOLUTELY should be key’d, but I digress…
The next level is doing a differential HARD-linked backup set.
ie: I’ve already backed up the remote directory to local backup “1”.
Put it all together (well, as I do it) for the second and onward backup:
# rsync -avx --human-readable --progress --stats --delete --ignore-errors --force --exclude-from=${EXCLUDE_FILE} \ --link-dest=/my_backups/1 -e 'ssh -p ${MY_PORT} ' ${USER}@${REMOTE_HOST}:/remote_directory/ /my_backups/2What this does only transfer new (or changed) files via rsync, otherwise we already have the file in the previous backup set, HARD-link to the file.
This takes up no more space (except using another inode pointing to the data) — and the data exists until the last linked file is deleted.
I have servers rsync’ing multiple times per hour allowing for snapshots, if you will, going back many many months with minimal overhead for ALL those backups (hundreds) — only new data. Wipe the oldest as space requires…
lol. Security reasons.. did you ever hear about certificates?
at least explain your concerns.
in my case I noticed a Rapid decrease in attempts to login to my Servers by just removing root from password as well as key auth.
unless someone knows your account name nobody could Start bruteforcing your password. though its better to just rely to passphrased ssh Keys only.
Just define your non-standard ssh ports in ~/.ssh/config file like so:
Host 192.168.1.103
Port 1431
Now all ssh based tools will just work without any extra command line hassle.
The right way to do this is to put the port in the .ssh/config file, that way you don’t need to remember the port numbers. In addition to security the other advantage is that it allows you access many machines from a single IP address. On your router you need to port forward each port to the appropriate machine then you need to alias the different names to the same IP (this is easy to do if you are using dyn.com as your dynamic DNS service, I’m sure it’s trivial with any DNS service). Once you’ve done that you can ssh into different machines by specifying the port number. Below is an example .ssh/config.
Host tom.foobar.com
Port 21010
BatchMode yes
Compression no
KeepAlive yes
Host jerry.foobar.com
Port 21011
BatchMode yes
Compression no
KeepAlive yes
You can also use rsyn -e “ssh -i private.key” together with custom SSH port for paswordless logins, quite handy.
And you should put your non-standard ssh key files in ~/.ssh/config too using the IdentityFile setting. Note that whenever you specify an IdentityFile you should also turn on IdentitiesOnly.