Lynis is an open-source and much powerful auditing tool for Unix/Linux-like operating systems. It scans the system for security information, general system information, installed and available software information, configuration mistakes, security issues, user accounts without a password, wrong file permissions, firewall auditing, etc.
Lynis is one of the most trusted automated auditing tools for software patch management, malware scanning, and vulnerability detecting in Unix/Linux-based systems. This tool is useful for auditors, network and system administrators, security specialists, and penetration testers.
Since Lynis is flexible, it is used for various different purposes that include:
- Security auditing
- Compliance testing
- Penetration testing
- Vulnerability detection
- System hardening
A new major version of Lynis 3.0.4 is released, after months of development, which comes with some new features and tests, and many small improvements. I encourage all Linux users to test and upgrade to this most recent version of Lynis.
In this article, we are going to show you how to install Lynis 3.0.4 (Linux Auditing Tool) in Linux systems using source tarball files.
Please Read Also :
- Install ConfigServer Security & Firewall (CSF)
- Install Linux Rkhunter (Rootkit Hunter)
- Install Linux Malware Detect (LMD)
Installation of Lynis in Linux
Installing Lynis via a system package manager is one of the easiest ways to get started with Lynis. To install Lynis on your distribution, follow the instructions below.
Install Lynis on Debian, Ubuntu & Mint
$ sudo apt-key adv --keyserver keyserver.ubuntu.com --recv-keys C80E383C3DE9F082E01391A0366C67DE91CA5D5F $ sudo apt install apt-transport-https $ echo "deb https://packages.cisofy.com/community/lynis/deb/ stable main" | sudo tee /etc/apt/sources.list.d/cisofy-lynis.list $ apt update $ apt install lynis $ lynis show version
Install Lynis on CentOS, RHEL, and Fedora
# yum update ca-certificates curl nss openssl # cat >/etc/yum.repos.d/cisofy-lynis.repo <<EOL [lynis] name=CISOfy Software - Lynis package baseurl=https://packages.cisofy.com/community/lynis/rpm/ enabled=1 gpgkey=https://packages.cisofy.com/keys/cisofy-software-rpms-public.key gpgcheck=1 priority=2 EOL # yum makecache fast # yum install lynis
Install Lynis on openSUSE
$ sudo rpm --import https://packages.cisofy.com/keys/cisofy-software-rpms-public.key $ sudo zypper addrepo --gpgcheck --name "CISOfy Lynis repository" --priority 1 --refresh --type rpm-md https://packages.cisofy.com/community/lynis/rpm/ lynis $ sudo zypper repos $ sudo zypper refresh $ sudo zypper install lynis
Installation of Lynis Using Source
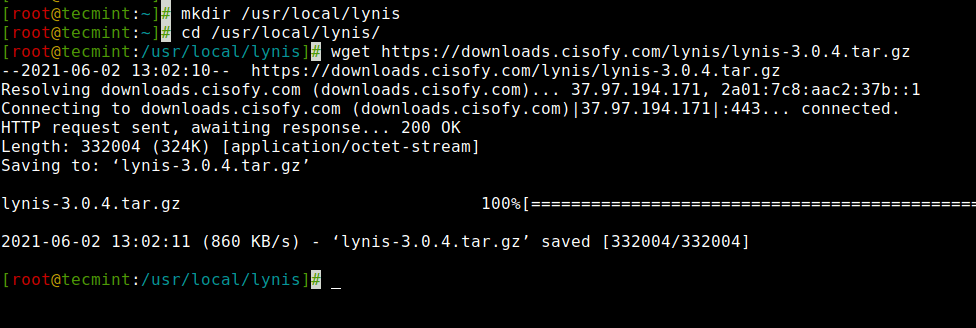
If you don’t want to install Lynis, you can download the source file and run it directly from any directory. So, it is a good idea to create a custom directory for Lynis under /usr/local/lynis.
# mkdir /usr/local/lynis
Download a stable version of Lynis source files from the trusted website using the wget command and unpack it using the tar command as shown below.
# cd /usr/local/lynis # wget https://downloads.cisofy.com/lynis/lynis-3.0.4.tar.gz
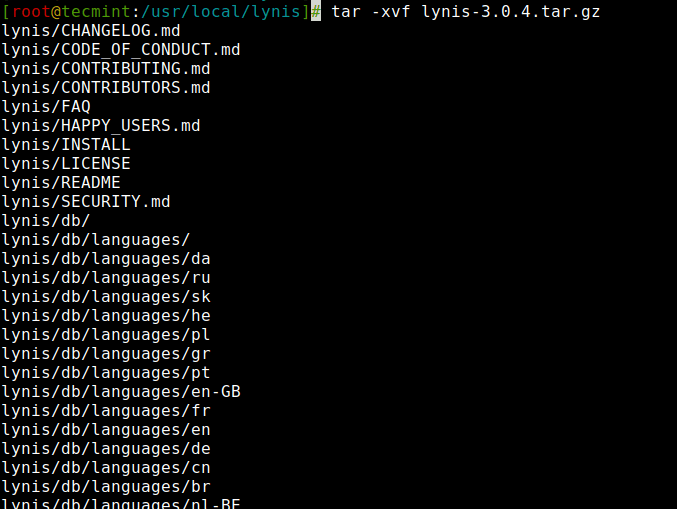
Unpack the tarball
# tar -xvf lynis-3.0.4.tar.gz
Running and Using Lynis Basics
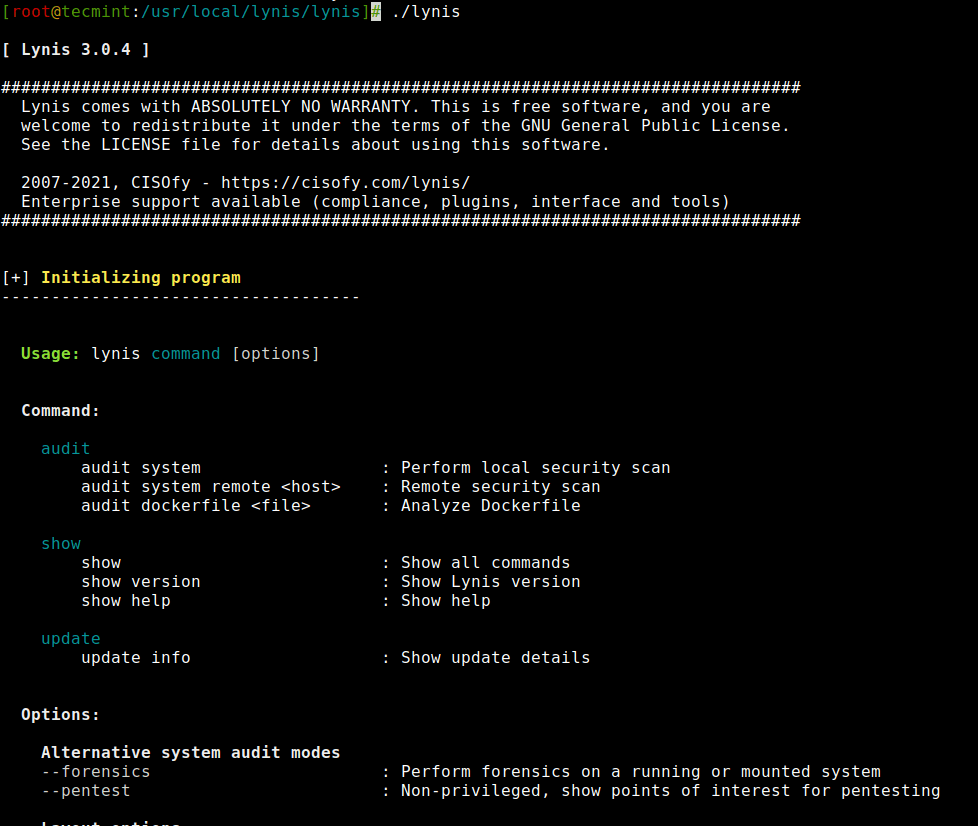
You must be the root user to run Lynis because it creates and writes output to /var/log/lynis.log file. To run Lynis execute the following command.
# cd lynis # ./lynis
By running ./lynis without any option, it will provide you a complete list of available parameters and goes back to the shell prompt. See figure below.
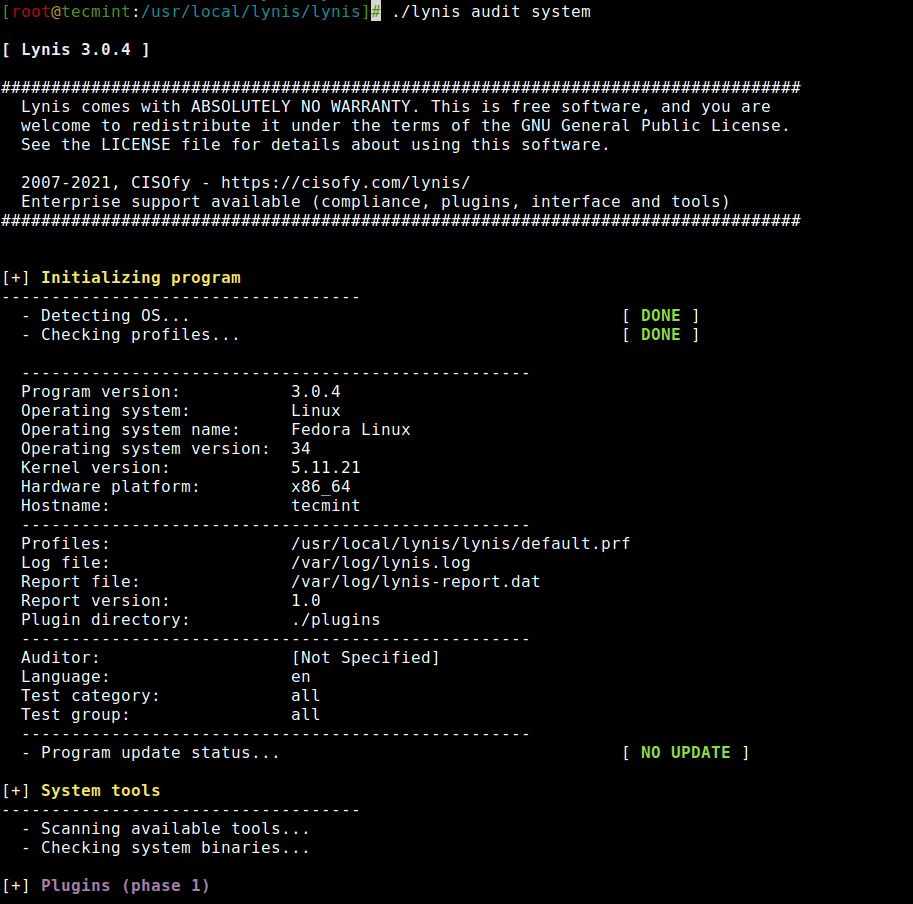
To start the Lynis process, you must define a audit system parameter to begin scanning your entire Linux system. Use the following command to start a scan with parameters as shown below.
# ./lynis audit system Or # lynis audit system
Once, you execute the above command it will start scanning your system and ask you to press [Enter] to continue, or [CTRL]+C to stop) every process it scans and completes. See the screenshot attached below.
Creating Lynis Cronjobs
If you would like to create a daily scan report of your system, then you need to set a cron job for it. Run the following command at the shell.
# crontab -e
Add the following cron job with the option --cronjob all the special characters will be ignored from the output and the scan will run completely automated.
30 22 * * * root /path/to/lynis -c -Q --auditor "automated" --cronjob
The above example cron job will run daily at 10:30 pm in the night and creates a daily report under /var/log/lynis.log file.
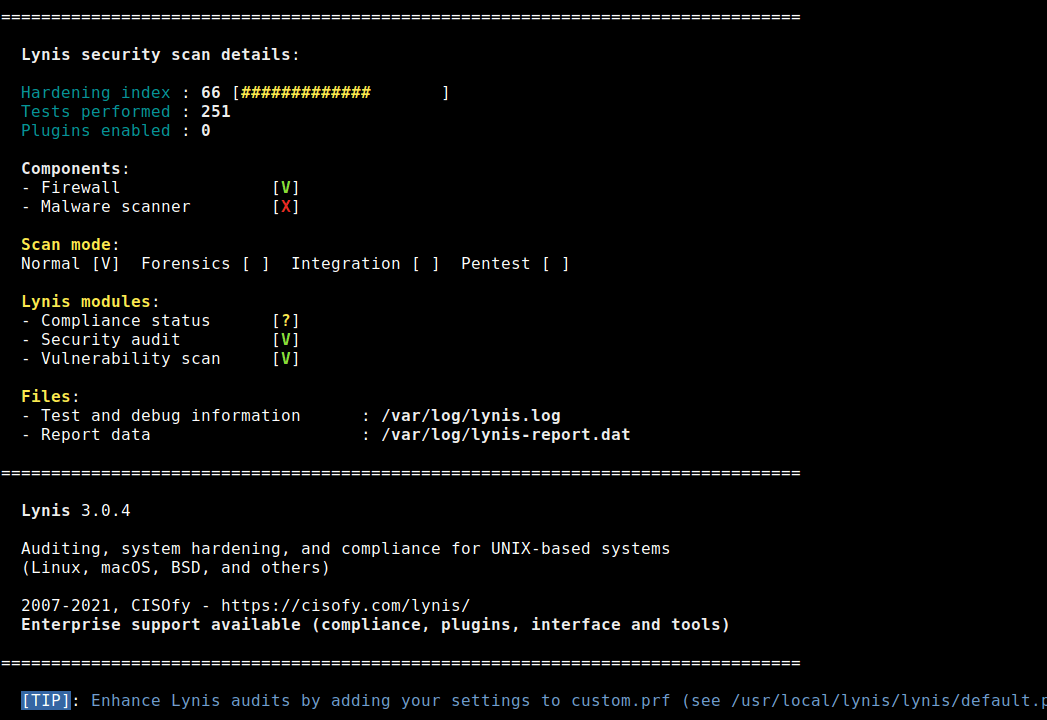
Lynis Scanning Results
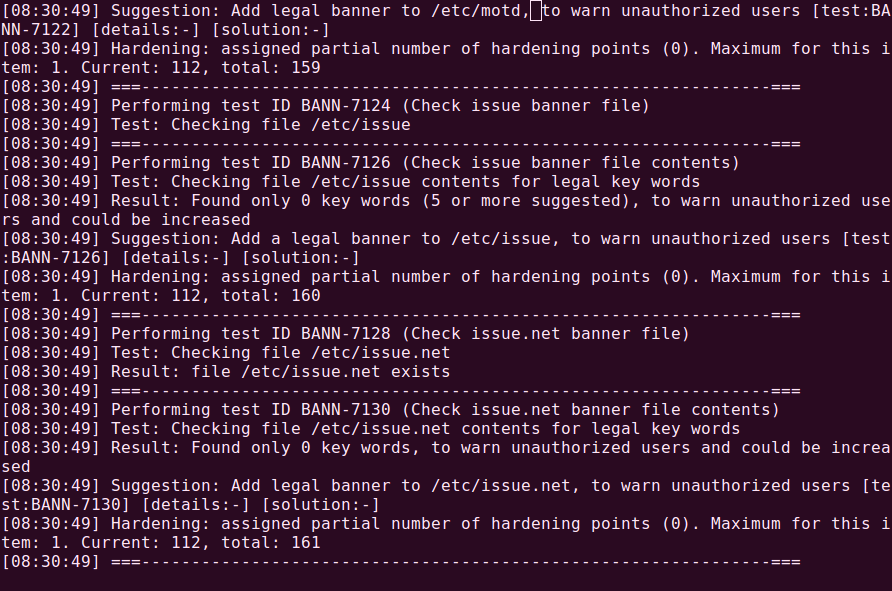
While scanning you will see the output as [OK] or [WARNING]. Where [OK] considered a good result and [WARNING] as bad. But it doesn’t mean that the [OK] result is correctly configured and [WARNING] doesn’t have to be bad. You should take corrective steps to fix those issues after reading logs at /var/log/lynis.log.
In most cases, the scan provides suggestions to fix problems at the end of the scan. See the attached figure that provides a list of suggestions to fix problems.
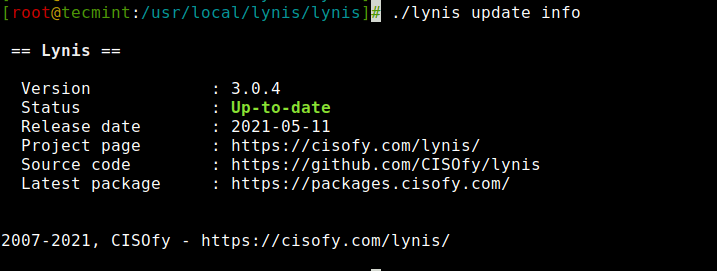
Updating Lynis
If you want to update or upgrade the current lynis version, simply type the following command it will download and install the latest version of lynis.
# ./lynis update info Or # lynis update info
See the attached output of the above command in the figure. It says our Lynis version is Up-to-date.
Lynis Parameters
Some of the Lynis parameters for your reference.
- audit system – Perform a system audit.
- show commands – Show available Lynis commands.
- show help – Provide a help screen.
- show profiles – Display discovered profiles.
- show settings – List all active settings from profiles.
- show version – Display current Lynis version.
--cronjob: Runs Lynis as a cronjob (includes -c -Q).--help or -h: Shows valid parameters.--quick or -Q: Don’t wait for user input, except on errors.--version or -V: Shows Lynis version.
That’s it, we hope this article will be much helpful to figure out security issues in running Linux systems. For more information visit the official Lynis page at https://cisofy.com/download/lynis/.


New to Lynis–tried to input –cronjob in terminal = no joy, don’t know how article not helpful in that respect.
Hi,
Thanks a lot
Very nice and useful article
When I run Lynis, my security report is stored in /var/log/lynis-report.dat – This the file you must read to see all the warnings and suggestions.
/var/log/lynis.log stores the Lynis activity record as it runs. You may find the warnings and suggestions in this file but it is difficult since this file is about 10 times as big as the report.dat file.
BTW – the most current version of Lynis is 3.0.4.
This article should be updated. The newest version of this is now 2.5.5. If you’re an ARCH user all you need to do is run a ↵ “sudo pacman -S lynis” and you’ll get this: “community/lynis 2.5.5-1“.
@Piers,
Thanks for informing us about new Lynis update, we’ve updated the installation instructions in the article to latest Lynis version..
So what security criteria standards does this check against?
I receive the following error when I try to update Lynis from 2.1.1 to 2.2.0:
“Error: Unknown protocol, please specify (http, https) in profile (update_server_protocol)[-30C”
What can I do in this situation?
Thanks.
I got the same error…
I got the same error too…
is there a way to scan a remote server or workstation with Lynis? or does the client have to be installed on the local machine in order to run the scan?
@Deezl,
Unfortunately, you can’t scan a remote Linux server or workstation with Lynis and there isn’t any client that do the job as you looking for, all you need to do is install the Lynis tool on each machine and set a auto cron to do the scan..
you are so great sir..you have guided so many newbee of linux like me..keep it up..
Hi Ravi
Thanks for easy to follow instructions. Also thanks with help with RKhunter but have since removed it and installed Lynis 2.1.1 as from what I gather RKhunter has been replaced by Lynis.
I have 1 question. How do I get the daily scanned results to be emailed to me.
@Hany,
Thanks for finding these instructions easy to follow, yes you right even I noticed last that RKhunter replaced by Lynis and think Rkhunter no more into development. Regarding daily mail from cron, you need to set the following parameter with email id shown:
Hi Ravi,
Thanks for reply. I followed instructions and yes I got an email, right on specified time. However I receive an error in my message as follows:
/bin/sh: root: command not found
Can you please let me know what I need to change.
@Hany,
It seems may be there’s something wrong with your cron entry, I suggest you to add like this:
Hello,
does lynis is only used to scan The server or also i can scan one user(One Website)?
Thanks
Am i wrong what i do is the following
1. mkdir /usr/local/lynis
2. cd /usr/local/lynis
3. wget http://cisofy.com/files/lynis-1.6.3.tar.gz
4. tar -xvf lynis-1.6.3.tar.gz
5. cd /lynis-1.6.3 i got this message (-bash: cd: /lynis-1.6.3: No such file or directory)
What is wrong with me
Hope to help
Step 5th is wrong, as you extracted the content of lynis-1.6.3.tar.gz in current working directory, so the command is:
I tried to download lynis but it failed to download after hitting save and clicking twice on option to open.
@John,
How you downloading using wget command or anything else. which version of OS you using?
hai, i wanna audit open-audit on localsystem in ubuntu……so please give me suggestions