Being anonymous on the Internet is not particularly the same as surging the web safely, however, they both involve keeping oneself and one’s data private and away from the prying eyes of entities that may otherwise take advantage of system vulnerabilities in order to harm targeted parties.
There is also the risk of surveillance from the NSA and several other top-level organizations and this is why it is good that developers have taken it upon themselves to build privacy-dedicated distros that host an aggregate of tools that enable users to achieve both online autonomy and privacy.
In as much as these privacy-centric Linux distros are targetted at a niche in the Linux community, many of them are robust enough to be used for general-purpose computing and many more can be tweaked to support requirements for virtually any specific user base.
A common factor across almost all privacy-centric Linux distros is their relationship with Tor given that many of them come with Tor’s solid anonymity network service built-in.
Tor’s anonymity gives users an environment for them to live safely without any data logs whatsoever, unlike most VPN providers that will still log your real IP address while still being able to see whatever data you may be transmitting at the point of exit of VPN servers.
However, VPN still has a sheer amount of advantages over the former which makes it somewhat superior in a way (depending on your use case) – particularly, when you put P2P file-sharing, and general Internet speed into consideration, VPN wins here (more on that later).
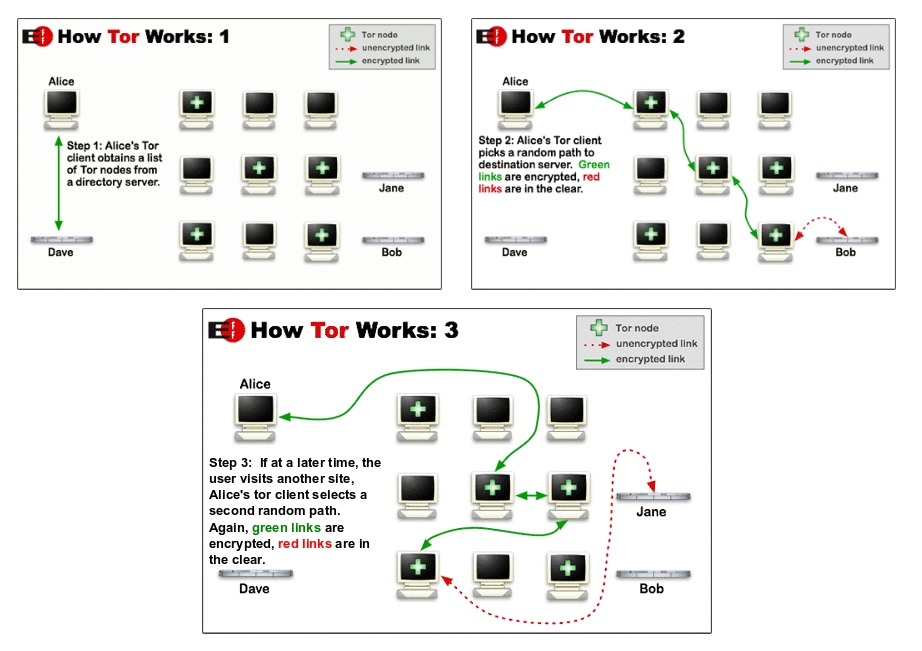
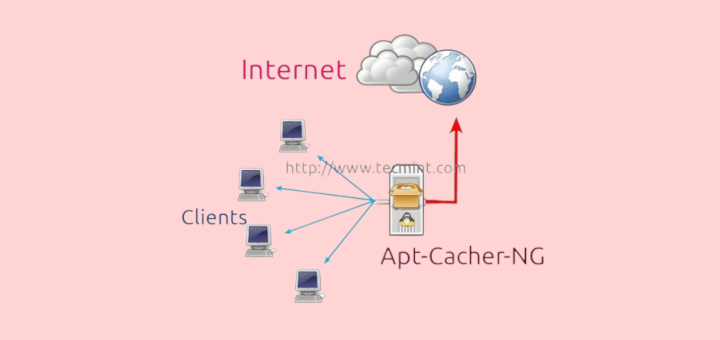
The Tor network secures all network traffic that goes through it by bouncing the data off several random nodes in order to reduce the traffic’s traceability chances.
Mind you, during this process, every piece of data is re-encrypted several times as it passes through the randomly selected nodes before finally reaching its destination as illustrated in the images below.
Most Secure Linux Distributions
Now that you have a basic understanding of how Tor works to the advantage of its users, here is our list of the Best Security-Centric Linux Distributions of this year.
1. Qubes OS
Qubes OS is a security-oriented Fedora-based distro that ensures security by implementing security compartmentalization. This happens by running every instance of running programs in an isolated virtual environment and then deleting all of its data when the program is closed.
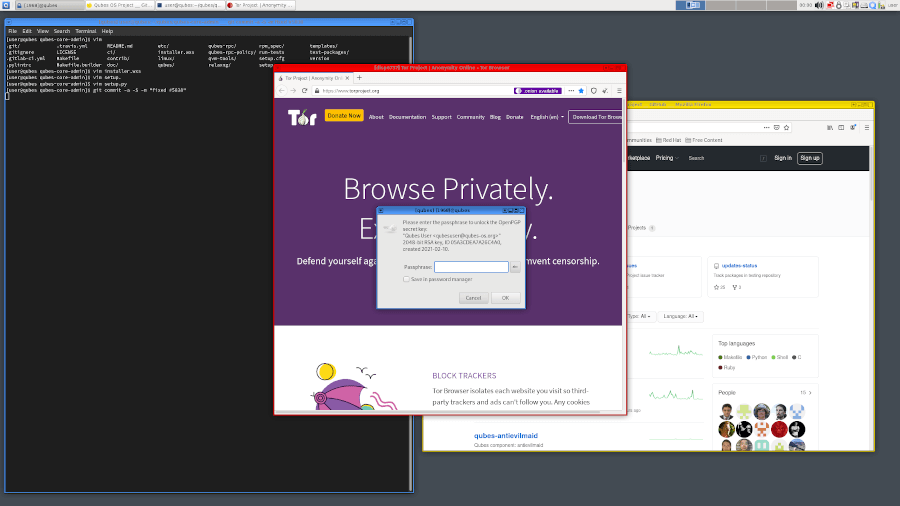
Qubes OS uses the RPM package manager and is capable of working with any desktop environment of choice without requiring a lot of computer resources.
Cited by Edward Snowden as the “best OS available today“, it is definitely a good choice if you want to make sure that your identity and data are yours alone whether online or offline.
2. TAILS – The Amnesiac Incognito Live System
Tails is a security-centric Debian-based distro designed to protect users’ identities online and keep them anonymous. Its name stands for The Amnesiac Incognito Live System and it is built to force all incoming and outgoing traffic through the Tor network while blocking all traceable connections.
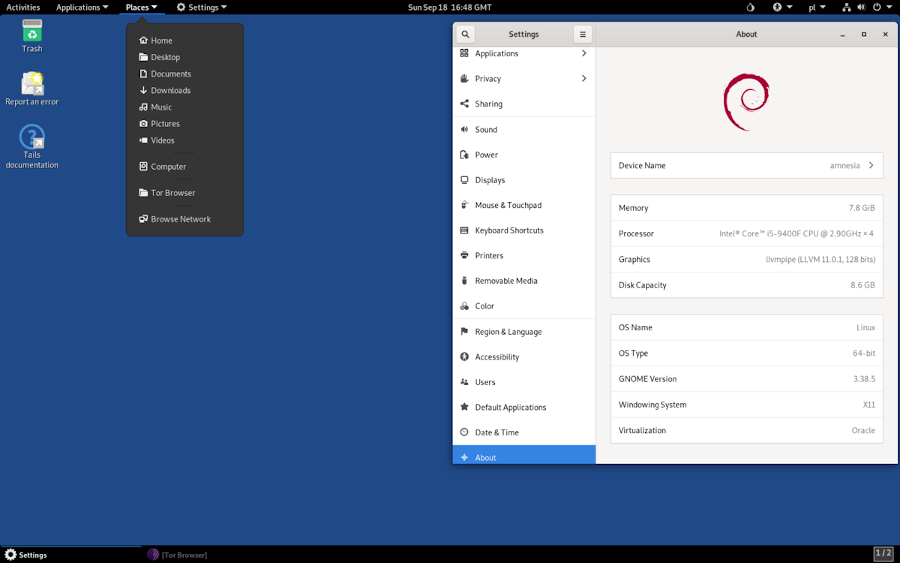
It uses Gnome as its default desktop environment and being a live DVD/USB, can be conveniently run from a pen drive when it stores all its data in the RAM.
It ships with open-source tools that are specially meant for privacy-specific reasons such as MAC address spoofing and windows camouflage, to mention a couple.
3. BlackArch Linux
BlackArch Linux is a lightweight Arch Linux-based distribution targetted at penetration testers, security experts, and security researchers.
It offers users all the features that Arch Linux has to offer combined with a ton of cybersecurity tools numbering 2000+ that can be installed either individually or in groups.
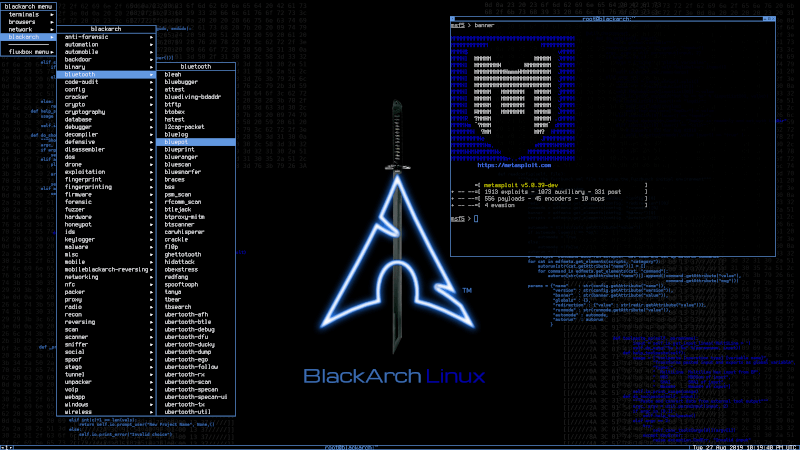
Compared to other distros on this list, BlackArch Linux is a relatively new project yet, it has been able to stand out as a reliable OS in the community of security experts.
It ships with the user option to choose any of these desktop environments: Awesome, Blackbox, Fluxbox, or Spectrwm, and as expected, it is available as a live DVD image and can be run from the convenience of a pen drive.
4. Kali Linux
Kali Linux (formerly BackTrack) is a free advanced Debian-based penetration testing Linux distribution designed for security experts, ethical hacking, network security assessments, and digital forensics.
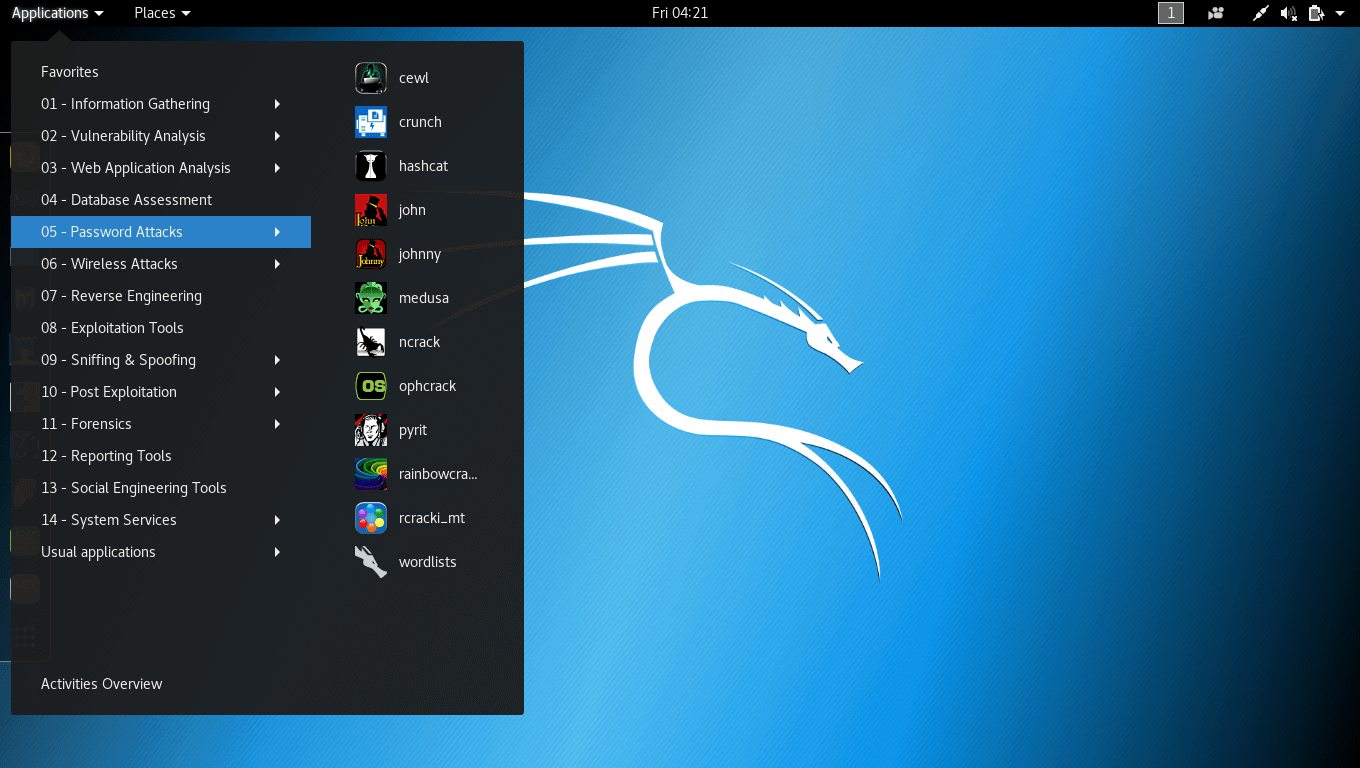
It is built to run smoothly on both 32 and 64-bit architectures and right out of the box it comes with a bundle of penetration testing tools that make it one of the most sort-after distros by security-conscious computer users.
There is a lot more that can be said about Kali Linux (as is the case with every other Operating System in this list) but I will leave the deeper digging for you to do.
5. JonDo/Tor-Secure-Live-DVD
JonDo Live-DVD is more or less a commercial anonymity solution that works in a similar fashion as Tor given the fact that it also routes its packets via specified “mixed servers” – JonDonym – (nodes in the case of Tor) having them re-encrypted each time.
It’s a viable alternative to TAILS especially if you are looking for something with a less restrictive UI (while still a live system) and a close-to-average user experience.

The distro is based on Debian and also includes an assortment of privacy tools and other commonly used applications.
JonDo Live-DVD is, however, a premium service (for commercial use) which explains why it is targeted at the commercial space. Like Tails, it doesn’t support any native way of saving files and it goes an extra mind to claim to offer users better computing speed.
6. Whonix
If you are looking for something a little different, Whonix takes quite a different approach from those mentioned above as it is not a live system but instead runs in a VM – Virtualbox to be specific – where it is isolated from your main OS in order to minimize the risk of DNS leakage or malware (with root privilege) infiltration.
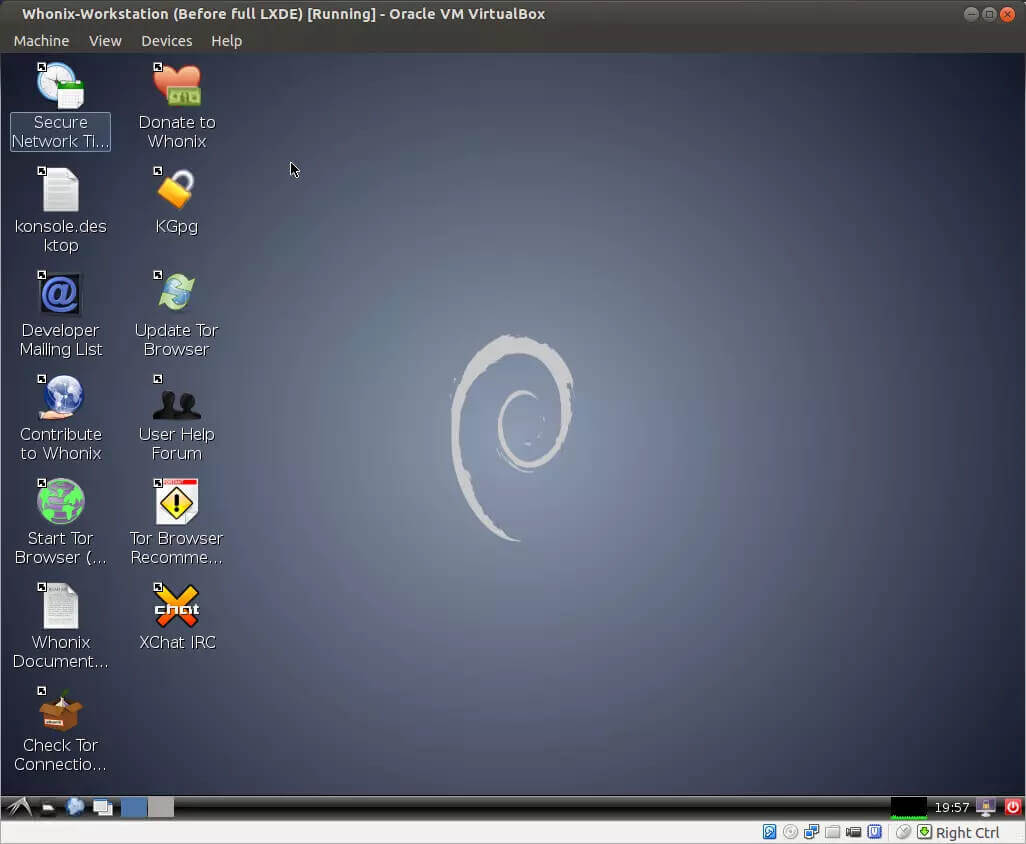
Whonix consists of two parts – the first is “Whonix Gateway” which acts as a Tor gateway while the other is “Whonix Workstation” – an isolated network that routes all its connections through the Tor gateway.
This Debian-based distro utilizes two VMs which makes it relatively resource hungry so you’ll experience lags every now and then if your hardware isn’t on the high end.
7. Discreete Linux
Discreet Linux, formerly UPR or Ubuntu Privacy Remix, is a Debian-based Linux distro designed to provide users with protection against trojan-based surveillance by completely isolating its working environment from locations with private data.
It is distributed as a live CD that cannot be installed on a hard disk and the network is deliberately disabled when it’s running.
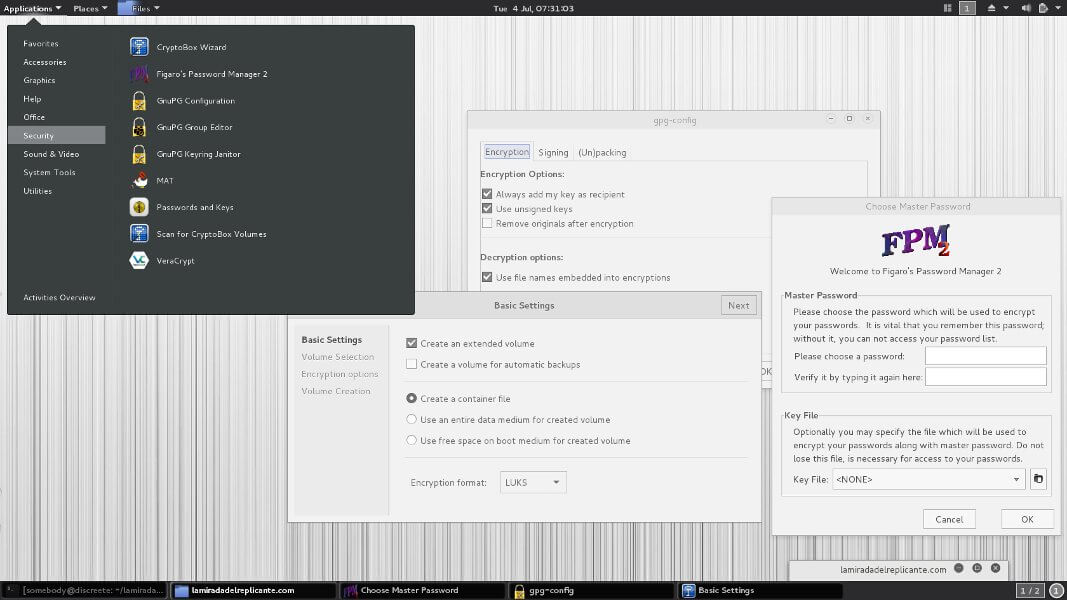
Discreet Linux is among the unique distros on this list and is evidently not intended for everyday computing tasks like word processing and gaming. Its source code is seldom updated given the little need for updates/fixes but it ships with the Gnome desktop environment for easy navigation.
8. Parrot Security OS
Parrot Security OS is another Debian-based distribution geared towards penetration testing, ethical hacking, and ensuring anonymity online.
It contains a robust and portable laboratory for digital forensics experts that not only includes software for reverse engineering, cryptography, and privacy but also for software development and surfing the Internet anonymously.
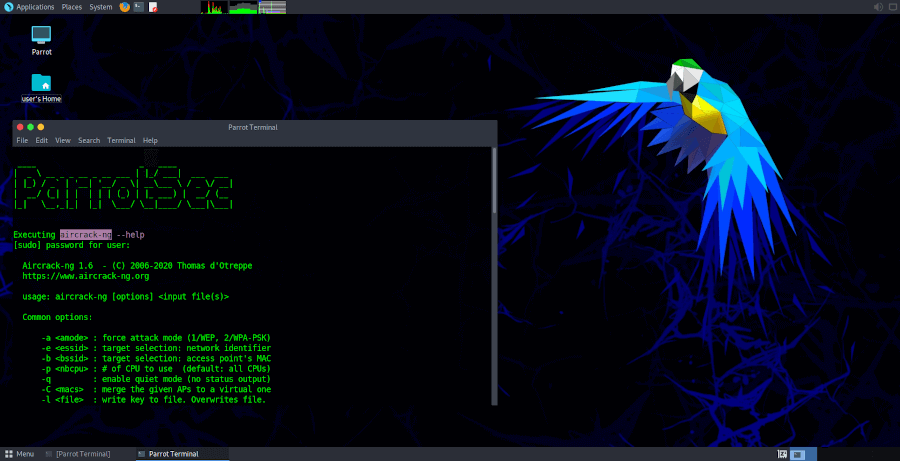
It is distributed as a rolling release that ships with only core applications such as Tor Browser, OnionShare, Parrot Terminal, and MATE as its default desktop environment.
9. Subgraph OS
Subgraph OS is a lightweight Debian-based distribution designed to be impervious to surveillance and interference from adversaries over any network no matter their level of sophistication.
It is created to use a hardened Linux kernel coupled with an application firewall to block certain programs from accessing the network and it forces all Internet traffic to go through the Tor network.
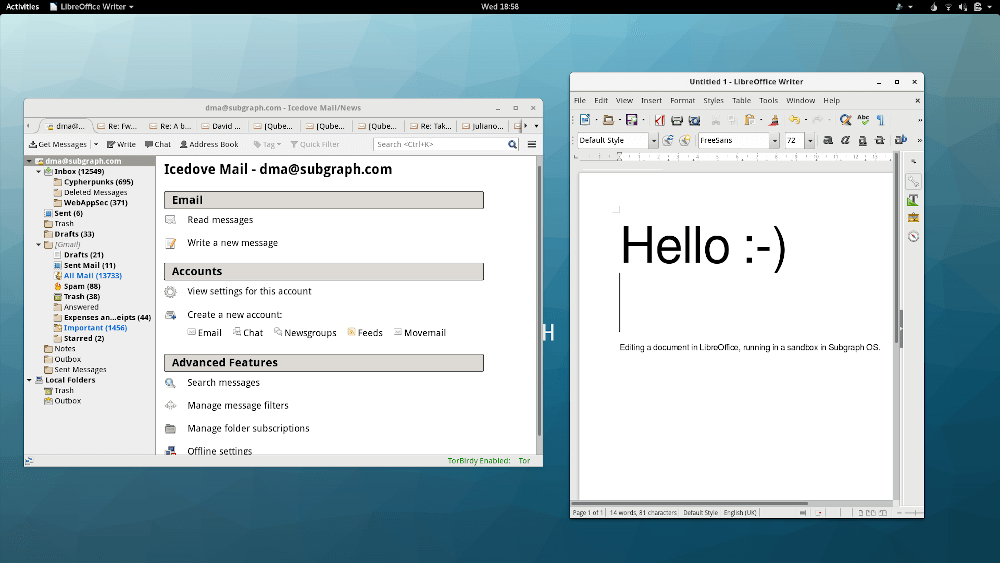
Designed as an adversary-resistant computing platform, Subgraph OS’s objective is to provide an easy-to-use OS with specific privacy tools without compromising usability.
10. Heads OS
Heads is a free and open-source Linux distro built with the aim of respecting users’ privacy and freedom and helping them to be secure and anonymous online.
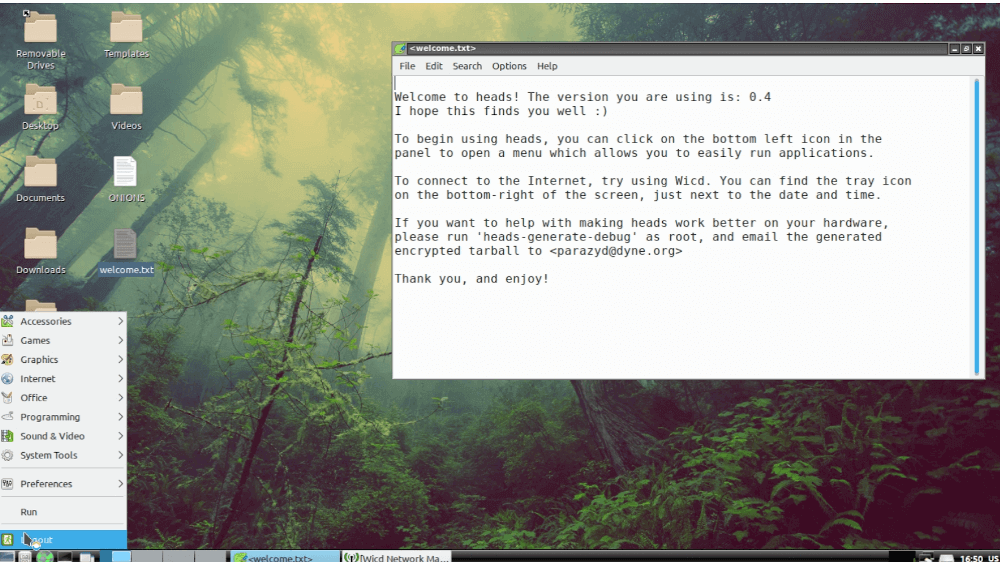
It was developed to be the answer to some of Tails’ “questionable” decisions such as using systemd and non-free software. That is to say, all the applications in Heads are free and open-source and it doesn’t use systemd as an init system.
11. Alpine Linux
Alpine Linux is a lightweight security-oriented open-source Linux distribution designed for resource efficiency, security, and simplicity based on BusyBox and musl libc.
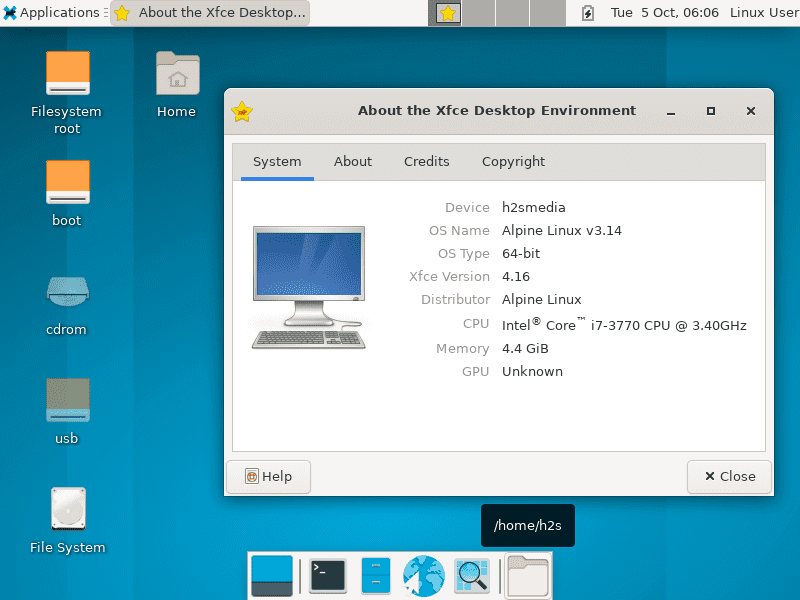
It has been in active development since its first release in August 2005 and has since become one of the most recommended images to use when working with Docker images.
12. PureOS
PureOS is a user-friendly Debian-based distribution built with a focus on user privacy and security by Purism – the company behind Liberem computers and smartphones.

It is designed to put its users in complete control of their computing system with full customizability, eye-catching animations, and minimal data vestiges. It ships with GNOME as its default desktop environment.
13. Linux Kodachi
Linux Kodachi is a lightweight Linux distribution designed to run from a pen drive or DVD. Right out of the bat, it filters all network traffic through a Virtual Proxy Network and the Tor network in order to obscure its user’s location and it goes the extra mile to remove any traces of its activities when it is done being used.
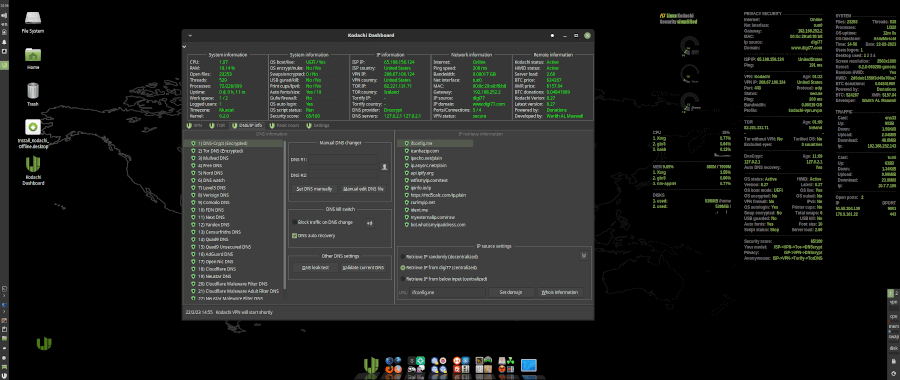
It is based on Xubuntu 18.04, ships with an XFCE desktop environment, and several built-in technologies to enable users to remain anonymous online as well as protect their data from getting into unwanted hands.
14. TENS
TENS (formerly Lightweight Portable Security or LPS) stands for Trusted End Node Security and it is a program that boots a barebone Linux OS from a portable storage device without mounting any data on the local disk.
TENS requires no administrator privileges to run, no contact with a local hard drive, nor installation, among several other advanced security-positive features.
Oh, and fun fact, TENS is managed and produced by the Air Force Research Laboratory’s Information Directorate, of the United States Air Force.
Conclusion
I don’t know how many of the distros in our list you have used before but choosing any one of them for a test drive is the first step to guaranteeing your security online and your ultimate pick is subject to your personal preference.
Which of the aforementioned security-centric distributions have you tried out in the past or which one are you willing to give a shot in the near future?
What has your experience with privacy-focused distros been like? Feel free to share your stories with us in the comments box below.




The last release of Heads was in march 2018. A 6 year old distro cannot be secure.
I don’t see anything about PureOS that should be included here, it’s just another Linux distro and its browser is not secure.
@John,
It’s important to remember that opinions about operating systems and their security can vary widely. PureOS is a Linux distribution that prioritizes privacy and security, and it’s designed to be as free and open-source as possible. While it may not be as well-known as some other distributions, it has gained a following among users who value these principles.
Regarding its browser, PureOS typically includes Firefox as the default web browser, which is known for its strong focus on security and privacy. However, the security of a browser can also depend on factors such as how it’s configured and the user’s browsing habits.
Ultimately, whether PureOS or any other Linux distribution is suitable for a particular user depends on their specific needs and preferences.
Subgraph hasn’t been updated since 2017 and even then it was just in the alpha stage. I enjoy your articles but please verify the sources before publishing. This is quite misleading.
Thank you, brother. This was a good post and brings light to a lot of the best online privacy and security for Linux users.
I love the article, but because you recycled part of it, JonDo/Tor-Secure-Live-DVD has been out of date since 2021 of august, and they no longer offer any services. There’s a banner on the website that includes the information.
I’m a big proponent of the rest of this article, including Alpine Linux, whonix, and Kali Linux which I used every day for security.
@Chris,
Thanks for the information, I will update the article…
Under Alpine, “inactive development” really should be changed to “inactive development” since the two are complete opposites. Alpine has been consistently releasing updates for years and is now at 3.11.5.
Thanks for catching that. I meant to write “in active development”.
you can save files with tails if you set up persistence. the thing about persistence is it is not hidden and in certain countries people can be compelled to fork over passwords to decrypt data or serve indefinite jail sentences. there should be an option to hide your persistence. no, it should automatically be hidden…
It is 2020 and I hope people know better
If you REALLY know what you’re doing. BlackArch is by far the best. Also, CyborgHawk, CyborgEssentials. The first one I ever used was Weakerthan 3.6. I think weaknetlabs now has it up to version 7.7.
It has a small community with great people and its not really known of, which is why I still use it from time to time. Right now, I have Back Box installed. But here in an hour or so I’m going to muilti boot my hard drive and put Kali, Ubuntu Studio, and possibly Quebes.
I have Tails 2.10 on an indestructible encrypted usb drive lol. Before my father passed away, he always said, “always be prepared, and always have backups for the backups”
Nice one
And yea your father was right
Your father was smart.
Kali Has always been my choice of distro for hacking/pen testing, although Parrot has become quit good and if there was a rolling release of that i know i would change to it permanently ..
i am looking for something that has everything of course I am better of building my own distro for that,
Hey, how’s the distro build coming?
what’s siteweb of Snowden ??