Failover is a type of backup operational mode in which the operations of a system components such as network are assumed by secondary system, only when the Primary system becomes unavailable due to system failure or any scheduled down times.

In this setup, we will see how to setup Failover and Load balancing to enable PFSense to load balance traffic from your LAN network to multiple WAN’s (here we’ve used two WAN connections, WAN1 and WAN2).
For example, If in-case, one of your WAN connection went offline due to some network connectivity issues, in this case your second WAN will be automatically shifted from WAN1 to WAN2 by pinging one of your system IP, if there isn’t any reply from system, it will automatically shift from WAN1 to WAN2 or vice-versa.
Load Balancer will combine our both WAN connections to become one powerful internet connectivity. For example, if you’ve 2MB connection for WAN1 and 2MB for WAN2, it will combine both into one with 4MB to stabilize the network connection speed.
To setup Failover Load Balancer, we need at least three Ethernet cards with minimum 100MB/1GB as follows. The first NIC is used for LAN with static IP and other two with DHCP.
My Environment Setup
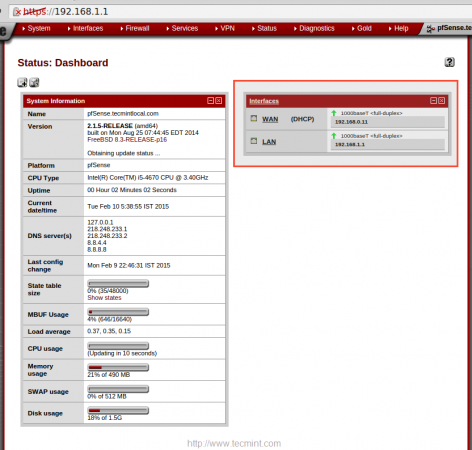
IP Address LAN : 192.168.1.1/24 IP Address WAN1 : From DHCP IP Address WAN2 : From DHCP
Before proceeding further, you must have a working PFSense installation, to know more on how to install pfsense, go through the following article.
Step 1: Configuring Network Interface
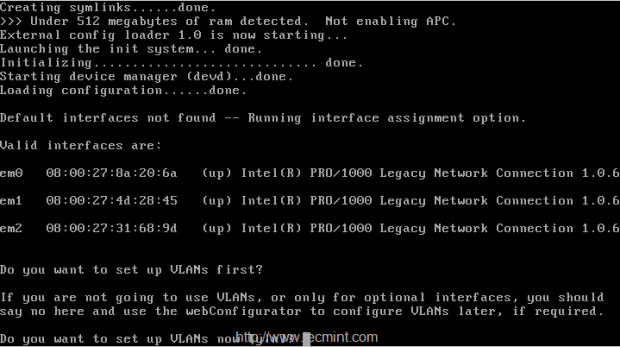
1. After installing PFSense, you will presented with the following screen with available interfaces to configure the network.
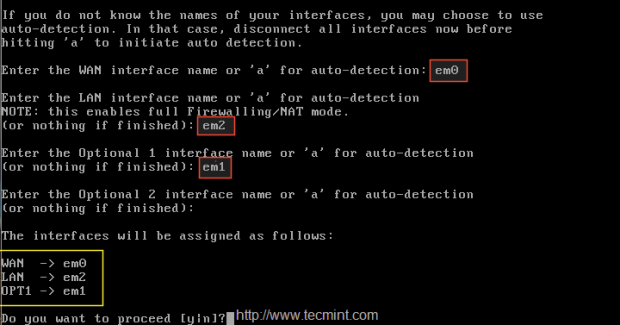
2. Choose 1st interface em0 as WAN1, IP will be assigned from DHCP, second interface will be em2 for LAN and add one more interface em01 (optional), this will be later changed to WAN2 with DHCP IP address. Here is the final interfaces assigned as follows.
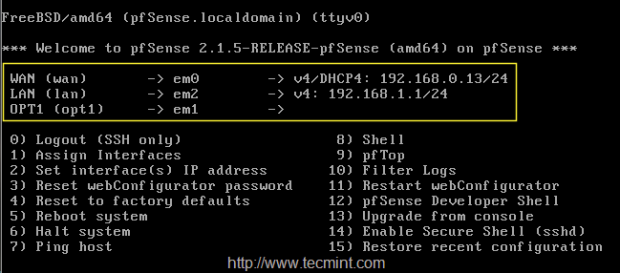
3. After configuring network interfaces, login into Pfsense dashboard at the following location and configure LoadBalancer.
https://192.168.1.1
4. After login into GUI, there you can see only WAN, LAN under the interface widgets as shown below.
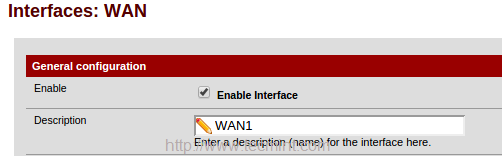
5. To configure Interface choose “Interface” from the TOP menu and click on WAN to add the description to WAN1, then click on Save to make changes.
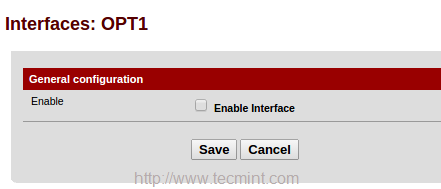
Again click on Interface and choose OPT1 and enable the interface to change description from OPT1 to WAN2.
Next, choose DHCP for IPv4 configuration type, or else choose IPv6 and configuration type as DHCP 6.
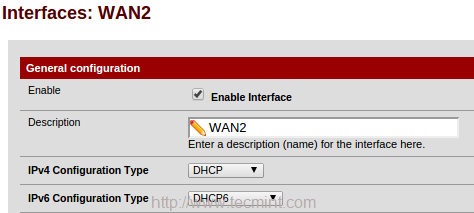
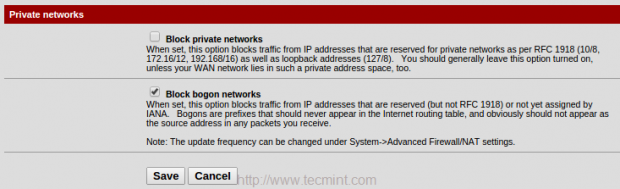
6. From the bottom of WAN2 page under Private networks, untick Block Private networks to unblock traffic from local networks, and block bogon networks. Save the changes by clicking on Save.
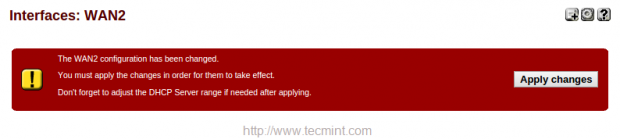
After making above changes, it will ask you to apply changes in the top of page, Click to confirm the changes.
Now you will get three interfaces in ‘Interface‘ widget in the Dashboard.
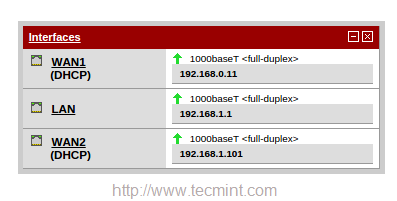
So, here we’ve configured 2 WAN for our pfsense. Now let us see how to configure our LoadBalancer for these configured WAN’s.
Step 2: Configuring Monitor IP
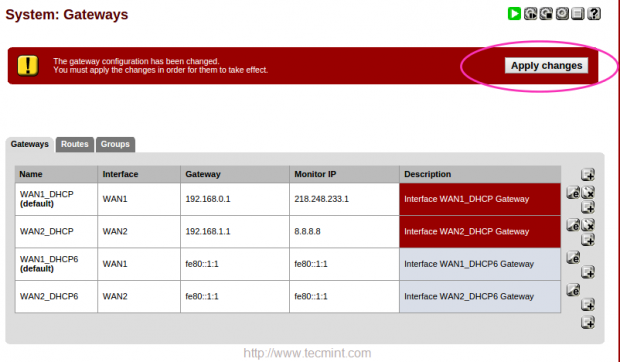
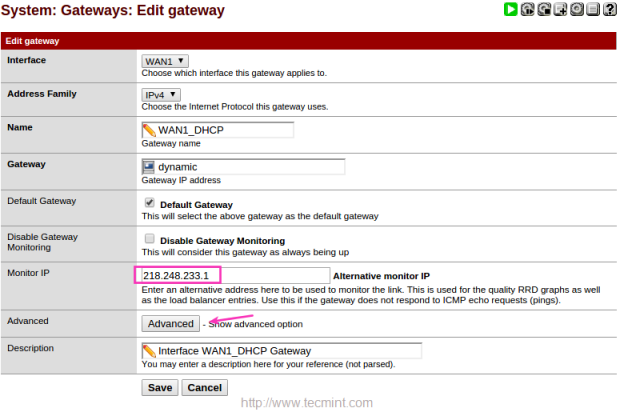
7. Before configuring Load Balance for pfsense, we need to configure a monitor IP for Load Balancer. Navigate to ‘System‘ menu in top and choose “Routing“.
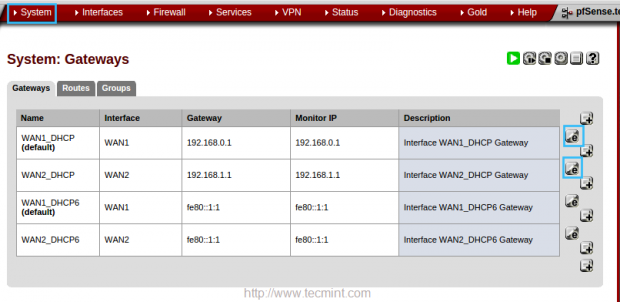
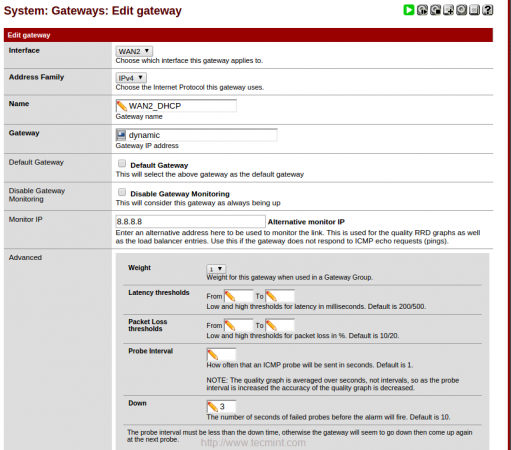
8. In the ‘Edit gateway‘ page, enter the IP address of monitor IP for both WAN1 and WAN2. In WAN1 I’m going to use my ISP DNS server IP 218.248.233.1. In WAN2 going to use Google public DNS 8.8.8.8.
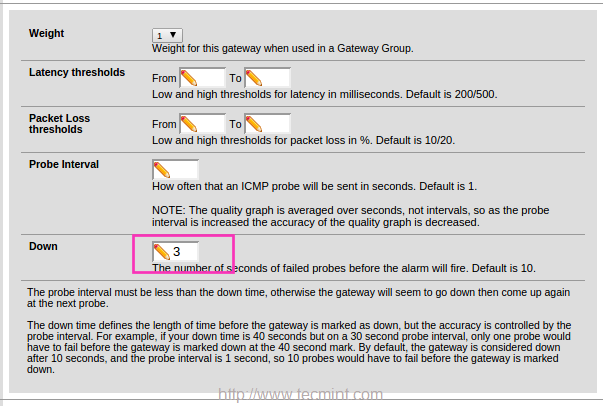
9. After adding Monitor IP, click on Advanced and give a low value for DOWN, here I’m using 3 seconds to monitor the IP. Default will be 10 Seconds.
Use same settings for WAN2. Here I have used Google DNS instead of using my ISP DNS. Click save to exit.
Click on Apply changes to make the changes permanent.