As a web server administrator, it is important to monitor and analyze the traffic accessing your web server, which includes identifying the top IP addresses to gain insights into traffic patterns and potential security threats.
One good thing in identifying the top IP addresses accessing your web server is the existence of access log file(s) that store information about every access activity that happens on the server.
Working with log files is always very important because they give you an account of everything that has happened within a system or application in this case your Apache web server.
In case of any performance or access-related problems, then log files can help you point out what could be wrong or is happening.
In this article, we will explore how to find the top 10 IP addresses accessing your Apache or Nginx web server using commands in Linux.
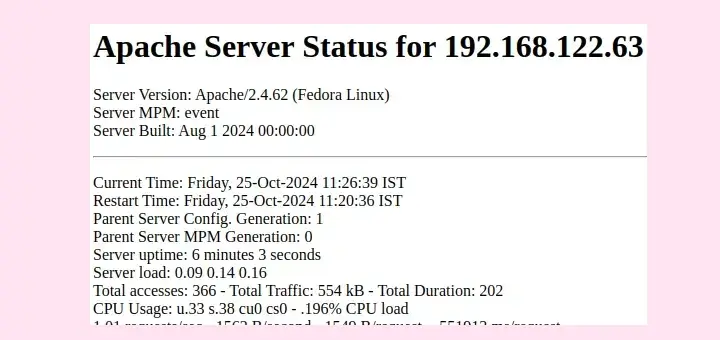
Accessing Web Server Log Files
The first step is to access the log files generated by your web server, which contain details of every request made to the server, including the IP addresses of the clients accessing it.
The default path for the Apache web server log is:
/var/log/httpd/access_log [For RedHat based systems] /var/log/apache2/access.log [For Debian based systems]
The default path for the Nginx web server log is:
/var/log/nginx/access_log
Use any text editor of your choice to view the logs. If your Apache server uses a different log file or location, adjust the command accordingly.
Find the Top 10 IPs of Web Server
To find out the top 10 IP addresses accessing your web server for the domain, you can use the awk command.
To find unique IP addresses of Apache web server, use:
awk '{print $1}' /var/log/apache2/access.log | sort | uniq -c | sort -nr | head -10
To find unique IP addresses of the Nginx web server, use:
awk '{print $1}' /var/log/nginx/access.log | sort | uniq -c | sort -nr | head -10
Sample Output:
5482 103.28.37.178 5356 66.249.78.168 1977 66.249.93.145 1962 157.55.39.251 1924 66.249.93.142 1921 66.249.93.148 1890 64.233.173.178 1860 108.61.183.134 1841 64.233.173.182 1582 157.55.39.251
Explanation of the above command:
awk '{print $1}'– Extract the first column (IP addresses) from the log.sort– helps to sort lines in an access.log file, the-noption compares lines based on the numerical value of strings and-roption reverses the outcome of the comparisons.uniq– helps to report repeated lines and the-coption helps to prefix lines according to the number of occurrences.head -n 10– Displays the top 10 IP addresses.
Alternatively, you can make use of the grep command to filter the access log for a specific time range or pattern matching.
grep "2023-10-10 12:00" /var/log/nginx/access.log | awk '{print $1}' | sort | uniq -c | sort -nr | head -10
To automate the process, you can create a script that runs at regular intervals to extract and analyze access logs. The script can then email the results or trigger alerts when certain IP addresses exceed defined thresholds.
#!/bin/bash
# Define variables
LOG_FILE="/var/log/nginx/access.log"
OUTPUT_FILE="/path/to/output.txt"
# Run the command and save the output
result=$(awk '{print $1}' "$LOG_FILE" | sort | uniq -c | sort -nr | head -10)
# Save the result to a file
echo "$result" > "$OUTPUT_FILE"
# Optionally, you can also send an email with the result
# mail -s "Top 10 IP Addresses Report" [email protected] < "$OUTPUT_FILE"
Remember to adjust the variables in the script according to your specific environment.
Summary
Many methods can be used to achieve this, if you know any better way do share in the comments, and also in case of any suggestions or questions, remember to leave a comment in the comments section below and we shall discuss it together.



Hi, Thanks for this wonderful article, helped a lot. But could you also help us if we need the IP address first and then the count. I tried to modify the code but unable to get the desired result. It would be great if you can help a bit.
Great article really useful.
Any more bits like this?
@BigJoe
Welcome, many thanks for the feedback.
Thank you. And if you want block:
unblock:
IP – remote addr
@Mike
Many thanks for the useful addition.
Nice one but it’s works on HP Unix>, please share if know anything about it.
@Pratham
Have you tried it out? It should work, first give it a try, and also let us know in case it doesn’t.
[lemp@lempstacker tmp]$ cat test.txt | awk ‘{arr[$1]+=1}END{flag=0;PROCINFO[“sorted_in”]=”@val_num_desc”;for (i in arr) if(flag<10) {print arr[i],i;flag++}}'
5 192.200.203.72
5 108.186.197.5
5 104.148.124.135
4 107.179.89.7
2 184.83.5.202
2 192.200.194.125
2 23.247.2.11
2 172.87.25.241
2 192.200.206.13
2 192.200.204.26
Good but lengthy method, though it gets the work done.
I love this Aaron, thanks for the information
Welcome, thank you for liking it.