GRand Unified Bootloader (GRUB) is a default bootloader in all Unix-like operating systems. As promised in our earlier article “How to reset a forgotten root password“, here we are going to review how to protect GRUB with a password.
As we mentioned before, someone can log in to single-user mode and change system settings, which is a big security risk. To stop unauthorized access, we need to protect Grub with a password in RHEL-based distributions such as Fedora, CentOS Stream, Rocky, and Alma Linux.
Here, we’ll learn how to stop users from getting into single-user mode and changing system settings, especially if they can directly access the system physically.
How to Password Protect GRUB Bootloader in Linux
Create a password for GRUB, be a root user, and open the command prompt, type the below command.
grub2-setpassword
When prompted type grub password twice and press enter.
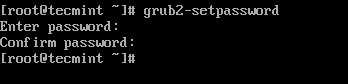
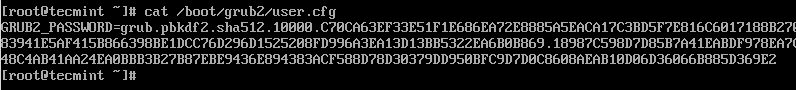
This will generate a hashed GRUB bootloader password in the file /boot/grub2/user.cfg file and can be viewed using the cat command as shown.
cat /boot/grub2/user.cfg
How to Generate New GRUB Configuration File
After creating the GRUB password, you need to re-create the new GRUB configuration file by running the following command.
grub2-mkconfig -o /boot/grub2/grub.cfg
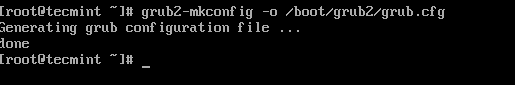
The above command will set the grub password in the configuration file. Now, reboot the system and check if the new GRUB password is set properly.
# reboot
How to Test GRUB Password Protection
After your system restarts, you will get the following GRUB screen, where you will get 5 seconds to break the normal boot process. So quickly press e key to breaking the boot process.
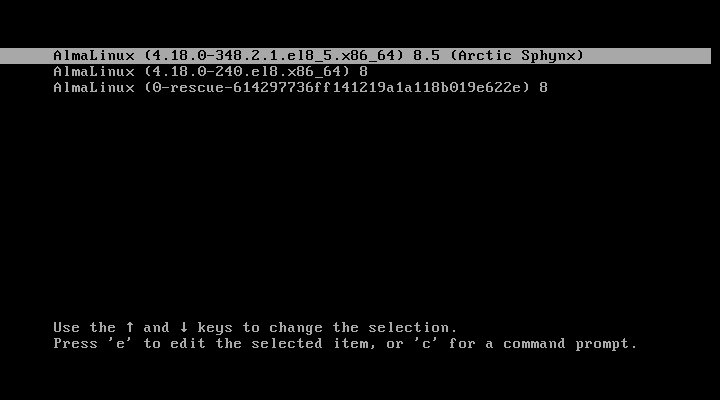
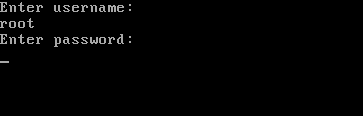
Once you press the e key it will prompt you to enter the GRUB password as shown.
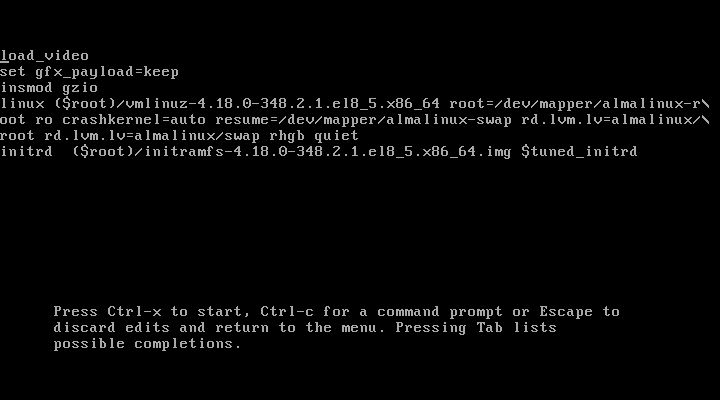
After entering the right username and password, you can edit GRUB parameters as shown.
How to Remove GRUB Password Protection
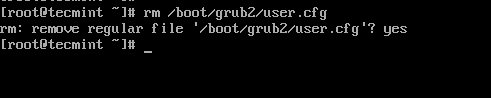
To remove GRUB password-protect from the boot menu, simply delete the file /boot/grub2/user.cfg.
rm /boot/grub2/user.cfg
This is how we can protect GRUB with passwords. Let us know how you secure your system? via comments.



Hi,
This article was helpful for me..
Thanks a lot
Excellent article
This will only protect the installed group, it’s still possible to boot up grub from a usb drive and then boot the Linux kernel in single-user mode from there.
But what about if you forbidden boot from USB?
Hi sir, this article was helpful, but terminal says grub command not found. What can be the issue?
What this equates to user commands ubuntu?
Thanks Alot
Hello , this was very help full for me
i have tried this it worked well and also i have tried removing the password in /etc/grub.conf file . i have doubt here if i forget the root password i will reset through single user mode . for suppose if i forget the password for both root and grub password . then hw can i recover it . please help me out in this
@Samanth,
Same way, go the the single user mode and remove the grub password from the grub menu configuration file and for resetting root password follow these guides.
https://www.tecmint.com/reset-forgotten-root-password-in-centos-7-rhel-7/
https://www.tecmint.com/reset-forgotten-root-password-in-rhel-centos-and-fedora/
@ravi Saive , thanks for the reply , actually my doubt is how can we enter into single user mode without providing the grub password . the e ( for edit ) it self is not shown there and only the ” p ” option is displaying. please let me know this . sorry for asking you the silly doubts i just want to clear my doubt . thanks in Advance .
@Samanth,
Sorry for my last comment, actually you can’t switch to single user mode when grub is password protected, the only way is to recover is using Linux Live CD. Boot into Linux using Linux Live CD, mount the root partition in rw mode and remove the password in the grub configuration file…
thank a lot, thank for the support @ravi Saive.
Hi,
I’m new in linux. We forgot both the root password and GRUB password.
How can I reset both? Also, how can i go to single user mode to remove the GRUB password?
Thank you
@Jun,
I hope these articles will help you out to recover your forgotten passwords..
i forgot the grub’s password, can you help me please. Thanks in advance.
@Omar,
Go to the single user mode and remove the Grub password…
FOR CENTOS…….LINUX
*HOW TO SET BOOT PASSWORD*
login root (#)
#vim /etc/grub.conf
:se nu
13 no line…… press enter key and go next line (14 no line)
password ******
:wq
hi
i followed the above steps in redhat linux . i did not get error . it didnt ask me the grub password …why ? can u tell me y its happened ………..
grub is not showing up all the installed operating systems.
I have rhel 6 64-bit os after that i installed centos 64-bit after installing centos rhel 6 is not showing up in grub..
whereas i am also having windows 7 which is active all the time
Thanks for your great info.
If e person boot via a Live CD or another OS, they can access to all HDD files & folders. How can we protect it?
How about Ubuntu? :/
Hai
how r u,
This is MOhan
I have one doubt How to change the grub password in Rhel 6
Regards
Mohan
mail:[email protected]
Please go through the article, we already explained very clearly how to protect grub with password. Follow same procedure for changing.
No there are different files in 18 because it uses grub 2 it does not work
What about Fedora 17/18? I think your solution won’t work with the latest versions.
I think it should work with latest Linux versions too,because the grub file is the same and procedure also. Why not you try and tell us.