SSH (Secure SHELL) is an open-source and trusted network protocol that is used to log in to remote servers for the execution of commands and programs.
It is also used to transfer files from one computer to another computer over the network using a secure copy (SCP) command and rsync command.
In this article, we will show you how to set up password-less login on RHEL-based Linux distributions such as CentOS, Fedora, Rocky Linux & AlmaLinux, and Debian-based distributions such as Ubuntu & Mint using ssh keys to connect to remote Linux servers without entering a password.
Using Password-less login with SSH keys will increase the trust between two Linux servers for easy file synchronization or transfer.
My Setup Environment
SSH Client : 192.168.0.12 ( Fedora 36 ) SSH Remote Host : 192.168.0.11 ( CentOS 8 )
If you are dealing with several Linux remote servers, then SSH Password-less login is one of the best ways to automate tasks such as automatic backups with scripts, synchronization files using the SCP command, and remote command execution.
In this example, we will set up SSH password-less automatic login from server 192.168.0.12 as user tecmint to 192.168.0.11 with user sheena.
Step 1: Create Authentication SSH-Keygen Keys on – (192.168.0.12)
First login into server 192.168.0.12 with user tecmint and generate a pair of public keys using the following command.
$ ssh-keygen -t rsa Generating public/private rsa key pair. Enter file in which to save the key (/home/tecmint/.ssh/id_rsa): [Press enter key] Created directory '/home/tecmint/.ssh'. Enter passphrase (empty for no passphrase): [Press enter key] Enter same passphrase again: [Press enter key] Your identification has been saved in /home/tecmint/.ssh/id_rsa. Your public key has been saved in /home/tecmint/.ssh/id_rsa.pub. The key fingerprint is: 5f:ad:40:00:8a:d1:9b:99:b3:b0:f8:08:99:c3:ed:d3 [email protected] The key's randomart image is: +--[ RSA 2048]----+ | ..oooE.++| | o. o.o | | .. . | | o . . o| | S . . + | | . . . o| | . o o ..| | + + | | +. | +-----------------+

Step 2: Upload SSH Key to – 192.168.0.11
Use SSH from server 192.168.0.12 and upload a newly generated public key (id_rsa.pub) on server 192.168.0.11 under sheena‘s .ssh directory as a file name authorized_keys.
$ ssh-copy-id [email protected]
Make sure that the correct permissions are set on the ~/.ssh directory and the ~/.ssh/authorized_keys file on the remote server.
$ ssh [email protected] "chmod 700 ~/.ssh && chmod 600 ~/.ssh/authorized_keys"
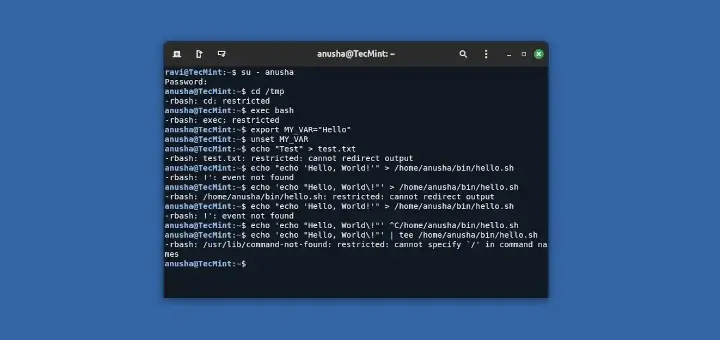
Step 3: Disable Password Authentication (Optional)
For increased security, you can disable password authentication on the remote server and only allow SSH key authentication. To do this, open the SSH server configuration file on the remote server:
$ sudo nano /etc/ssh/sshd_config OR $ sudo vi /etc/ssh/sshd_config
Find the line containing PasswordAuthentication and set it to no.
PasswordAuthentication no
Save the file and restart the SSH service.
$ sudo systemctl restart sshd
Step 4: Test SSH Passwordless Login from 192.168.0.12
From now onwards you can log into 192.168.0.11 as a sheena user from server 192.168.0.12 as a tecmint user without a password.
$ ssh [email protected]
In this article, you’ve learned how to set up an SSH Passwordless login using an ssh key. I expect that the process was straightforward. If you have any questions, please post them in the comment section below.

nice write up. !
Why not use ed25519 (elliptic curve) as key type?
Good one! Worked like a charm on CentOS 7.
This also worked for connecting my MacBook air to my ubuntu media server.
Thank you for this one. It really helps me in doing SSH public key.
This setup is for one id. how can we set it up for all users?
Doesn’t a passwordless login compromise security?
@Dragonmouth,
Passwordless authentication is safe, secure, and easy to use, as it reduces attack vectors by eliminating password management practices…
It was really helpful. You saved my day. Thanks :)
ssh root@IPaddress
root@IPaddress’s password:
Permission denied, please try again.
root@IPaddress’s password:
Permission denied, please try again.
root@IPaddress’s password:
Permission denied (publickey,gssapi-keyex,gssapi-with-mic,password,hostbased).
The problem is I tried the methods related to public key generation. But no matter I do what it always keeps asking for a password and my permission gets denied.
All conventional methods have failed.
Need urgent help.
Step 1: ssh-keygen -t rsa
Step 2: ssh root@IPaddress mkdir -p .ssh
root@IPaddress’s password:
Permission denied, please try again.
root@IPaddress’s password:
Permission denied, please try again.
root@IPaddress’s password:
Permission denied (publickey,gssapi-keyex,gssapi-with-mic,password,hostbased).
Please help. It’s urgent
Hey,
I’m just copy-paste for the same command. But it’s asking password!
Please guide me for the same :
SSH Client : 10.10.10.4
SSH Remote Host: 10.10.10.5
Step 1: Create Authentication SSH-Keygen Keys on – (10.10.10.4)
Step 2: Create .ssh Directory on – 10.10.10.5
Step 3: Upload Generated Public Keys to – 10.10.10.5
Step 4: Set Permissions on – 10.10.10.5
Step 5: Login from 10.10.10.4 to 10.10.10.5 Server without Password
CRDB@Consul-Server1:/root$ ssh [email protected].5
[email protected].5’s password:
Thanks
Raj
Hi, I was in the same situation, but I make the next simple and more natural steps (from an SSH perspective)
After you create keygen, make:
So the server print: “Identity added: (id_rsa)”.
next
System request the CRDB password and later the server print: “Number of keys (s) added: 1”
finally, you can do:
Also, you must check the /eth/ssh/sshd_config in your remote server (in your case 10.10.10.5) and set the next values :
When making any change over ssh, will need to restart ssh service in your remote server:
Regards!
Juan
Really good site, thank you so much for your time in writing the posts.
Thank you so much for this very good explanation.
I searched multiple sites till I got here.
My issue resolved.
I have set the passwordless login, but after login, I have run the script in mid-time connection is closed. Where can set the timings for these connections?
You can try using the option “ConnectTimeout” with
-oas like.That is a wonderful article explaining passwordless authentication Ravi. I had been looking for something just like this.
Passwords are out there on their way. Many individuals are already comfortable with being authenticated without a password, such as using FaceID on iOS or scanning a fingerprint on Android, and organizations are gradually moving to passwordless authentication; a way to prove the identity of an online user for enhanced security purposes using an alternate factor other than a password.
I read a similar article about the same, the link of which I am sharing here:
https://www.loginradius.com/blog/start-with-identity/2019/10/passwordless-authentication-the-future-of-identity-and-security/I’ll be sharing your article with my friends and colleagues. Till then keep up the good work Ravi :)
This is a command to copy the key to server:
Typo: comment -> command
$ cat ~/bins/makessh1
ssh $@ mkdir -p .ssh
cat ~/.ssh/id_rsa.pub | ssh $@ ‘cat >> .ssh/authorized_keys’
ssh $@ “chmod 700 .ssh; chmod 640 .ssh/authorized_keys”
Thanks, very useful article…
It works perfectly for me.
Allow user agent on local/client host to ssh remote server ([email protected]) without a password.
.sshDirectory on the remote server.How do i undo this?
@Lee,
Just remove
.sshdirectory from both the machine…Thanks for nice article
A perfect article helped me to set up on my Linux server.
Thanks,
It worked and very useful.
Hi Ravi,
Wonderful post! Thank you! I have a question. I would like to be able to do this for multiple devices (say ssh from a Linux computer into multiple Raspberry Pi computers) When I try to do this for another Pi device, the previous one is forgotten. How can I use what you are showing here for multiple devices?
@Vincent,
Create one Authentication SSH-Keygen Keys on your Linux server, and upload the Generated Public Key to multiple remote machines under
.sshdirectory.Will these authorized_keys files be not expired even after patch deployment server restarts? Can you please reply to this?
@Revathi,
No these SSH authorized_keys files never expire and remain the same even after update or upgrade of server to newer releases…
Step 2 seems to be misleading, since creating a directory on the server is not feasible w/o this step
ssh-copy-id [email protected].Step 2 assumes there isn’t already an ssh directory on the server.
‘ssh-copy-id‘ is a shell script that will perform steps 2 and 3, but it is not present on every Linux device.
Following the instruction in step 2 will work in any case.
Thank you, it is very useful.
how to make password less ssh connectivity for sudo user/passwd
I am sorry, but this did not work. The key clearly did not do the needful, and SSH had to proceed to password.
debug1: Next authentication method: publickey
debug1: Offering public key: /home/rajarshi/.ssh/id_rsa RSA SHA256:fRkni96PqvRcjzDxjSKhLnNaCazOdOgTFzsKliz7fas
debug1: Authentications that can continue: publickey,gssapi-keyex,gssapi-with-mic,password
debug1: Trying private key: /home/rajarshi/.ssh/id_dsa
debug1: Trying private key: /home/rajarshi/.ssh/id_ecdsa
debug1: Trying private key: /home/rajarshi/.ssh/id_ed25519
debug1: Trying private key: /home/rajarshi/.ssh/id_xmss
debug1: Next authentication method: password
Very helpful article..
I’m getting the error “Permission denied (publickey).” I have pasted the public key in /home/ubuntu/.ssh/authorized_keys the server. But while establishing the connection, I’m getting the error.
Try:
chmod 600 ~/.ssh/authorized_keysIt should work
If you are getting prompted for SSH password then you missed a step :)
Make sure that you save the
id_rsa.pub(the public key) into the keys folder of the user that you wish to SSH into.So for example, if you want to SSH as root, then you need the key stored in
/root/.ssh/authorized_keys.If you want to ssh as ‘yourname‘ then it will be /home/yourname/.ssh/authorized_keys.
To set this up, you first need to SSH into the destination with username/password combination. Now you’re in, you can copy the ssh public key into the right location. This is why you see “enter your password here” above.
Really awesome article, thank you very much.
what is the password used in ENTER YOUR PASSWORD section
“YOUR PASSWORD” – all capitals. Easy to remember.
Thanks. It works in one go, without any error.
I’ve followed your very useful and detailed tutorial line for line but still get prompted for a password each time I ssh into the remote host. Are there any settings in ssh_config or sshd_config that need updating following this?
same issue here using Redhat 6.9
@RF and @AliAhmed
Try this:
On the machine where the ‘authorized_keys‘ file resides, set proper permissions for the directory .ssh and the file.
Then, to test:
In the SSHD config file: */etc/ssh/sshd_config*
Save, reload/restart sshd deamon.
This should solve the prompting password field.
Good luck.
The best and clear explanation ever. Thanks for doing this and keep it up with this excellent articles
Hi,
A very simple explanation with all descriptive steps. I win in the first attempt
Thanks for your efforts in this article.
awesome document about the remote ssh setup….
Here’s a much easier way to do it.
On the client:
Done!
Thanks, this worked like a charm!
I just learned recently that ssh has a simple command to automate the installation of the new public key on remote servers that does steps 2-4 automatically:
ssh-copy-id.Hey, how does it work if i want to shut-down 2 or more remote servers with this method, because when i try to do a 2nd remote then i can’t log into the 1st without password any more :(
That doesn’t make sense to me. Do you mean that you are trying to shutdown machine c from machine b? Or are you trying to shut down both b and c from a
Actually, I think you may be repeating the key gen step twice. Create the key once and copy to both targets.
Possible to update your publickey authentication method from ssh1 to ssh2 protocol-2 – as ssh1 is pretty much obsolete. As well proper use of ssh-keygen to generate higher value key-types for better ssh security!
Good, Nice article and easy to understand. keep posted these kind of technical stuff. will help to new people who is new the environments.
This seems very complicated all you have to do is use the command ssh-copy-id user@hostname and it would copy that id into the users authorized host files and you can ssh without a password.
Thanks buddy, you explained this well. I liked your explanation and it was helpful to me in creating a passwordless ssh on my single node cluster. I’ll try similar steps on my multinode hadoop cluster.
This will work for same users (with the name) on different servers to login into each other user without password? for me its asking password again while I try to login
i think you need to restart the sshd service
yes, it works for both hosts using the same user account. The service does not need to be restarted
Hi,
I have tried passwordless login and working fine from server A to server B. But reverse side it is not working and asking for password.
@Joy,
You need to setup same SSH Passwordless login on server B to A, to have passwordless login.
After this is done, can we login the client from the server w/o using password? What about doing this for multiple servers and clients?
Thank you!
@Lambert,
If you have followed instructions correctly, yes you will able to login to remote server without password. For multiple SSH passwordless logins, follow the same instructions on each server.
Hello Ravi,
This is because, if you check ssh config file.
Default path for ssh authorized keys are in .ssh directory at you home directory.
————————————————————————–
AuthorizedKeysFile .ssh/authorized_keys
————————————————————————–
You can change path if you wish :)
why we are going to create a
.sshdirectory on client server?@Ravi,
To store ssh key under this hidden .ssh directory, which is used to authenticate passwordless login.
After following above steps i’m unable to login for local host
@Yasir,
What error you getting while login to localhost using SSH?
After step 2, when I enter my password, I’ve been getting an error.
stty: standard input: invalid argument
Any comments on how to solve this?
@Sai,
I think you are using different shell other than Bash shell…
Any way to disable the typing animations? Even ebooks don’t have this. It in no way assists, just distracts & irritates.
Oh – the info is great btw, worked a treat.
It would really be much easier to read your article if you used “source server” and “destination server” instead of IP addresses.
Great One!!!
In step 1: “generate a pair of public keys”, it should be “generate a pair of public/private keys”.
Great tutorial! Very clear…I took 5 minutes to set up my computers
Great tutorial – best I’ve seen and I’ve been looking for a while. There are a couple of places where its not quite clear, for example “your password” presumably means you/me as root, but the reader might think its Sheen’s password (perhaps Sheena is the user/owner at the other end etc.. And if the destination machine has a different password presumably its for that machine for you/me and not the one for your/my source machine etc.
This is a great tutorial, nonetheless maybe it should be updated to learn folks how to generate even stronger RSA keys.
After the whole process I am not able to login without password.
Question: What happens if the users tecmint or sheena’s password are changed? Can sheena still log into 192.168.0.11 and then to server 192.168.0.12 as tecmint user without password to execute anything?
Thank you.
@Min,
Yes, even after password change user able to login without any password, as SSH works on Key authentication.
Amazing tutorial, you really saved me!
Outstanding tutorial! thumb up!
Tried using the -copy-id but got the error message command does not exist.
is it available in some newer vesrions
ssh-copy-id is a binary from standard package named ‘openssh-client’. If you are using system newer that 2010 I guess you should have it :)
Ever heard of ssh-copy-id ? :) You can replace this whole tutorial to just two steps :)
On machine from you login to other machine
1. ssh-keygen -t rsa
2. ssh-copy-id user@onthmachineyouwanttoconnect
3. provide password and voilla – that’s it
Interesting fact: the ssh-copy-id “binary” is actually a shell script located in the bin folder, marked executable. So, if you need to work with ssh servers that need to use (for instance) a port other than 22, you can edit the binary with a text editor.
Great thanks, it is awesome :)
Awesome!!!! I spent about 6 hours on this.