The shutdown command schedules a time for a Linux system to be powered down, it may as well be used to halt, power-off or reboot the machine when invoked with particular options and reboot instructs the system to restart.
Certain Linux distros such as Ubuntu, Linux Mint, Mandriva just to mention but a few, make it possible to reboot/halt/shutdown the system as a normal user, by default. This is not ideal setting especially on servers, it must be something to worry about especially for a system administrator.
In this article, we will show how to disable shutdown and reboot commands for normal users in Linux.
Disable Shutdown and Reboot Commands in Linux
The easiest way to disable shutdown and reboot commands using the /etc/sudoers file, here you can specify a user (tecmint) or group (developers) which are not allowed to execute these commands.
# vi /etc/sudoers
Add these lines to Command Aliases section.
Cmnd_Alias SHUTDOWN = /sbin/shutdown,/sbin/reboot,/sbin/halt,/sbin/poweroff # User privilege specification tecmint ALL=(ALL:ALL) ALL, !SHUTDOWN # Allow members of group sudo to execute any command %developers ALL=(ALL:ALL) ALL, !SHUTDOWN
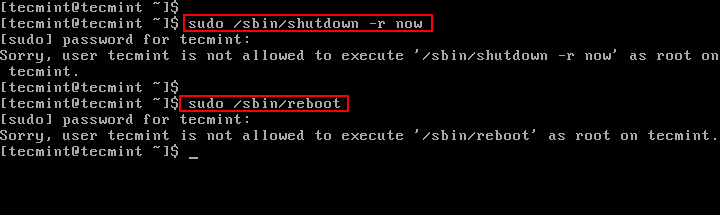
Now try to execute shutdown and reboot commands as normail user (tecmint).
Another way is to remove execution permissions on shutdown and reboot commands for all users except root.
# chmod o-x /sbin/shutdown # chmod o-x /sbin/reboot
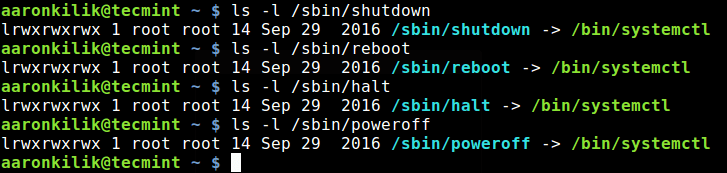
Note: Under systemd, these file(/sbin/shutdown, /sbin/reboot, /sbin/halt, /sbin/poweroff) are only symbolic links to /bin/systemctl:
# ls -l /sbin/shutdown # ls -l /sbin/reboot # ls -l /sbin/halt # ls -l /sbin/poweroff
To prevent other users from running these commands, you would simply remove execution permissions as explained above, but this is not effective under systemd. You can remove execution permissions on /bin/systemctl meaning all other users except root will only run systemctl.
# chmod o-x /bin/systemctl
You may also want to learn how to disable certain functionalities such as SSH root login and limit SSH access, SELinux, unwanted services in Linux by reading through these guides:
- How to Enable and Disable Root Login in Ubuntu
- How to Disable SELinux Temporarily or Permanently in RHEL/CentOS 7/6
- Disable or Enable SSH Root Login and Limit SSH Access in Linux
- How to Stop and Disable Unwanted Services from Linux System
That’s it! In this article, we showed how to disable shutdown and reboot commands for normal system users in Linux. Do you know of any other way of doing this, share it with us in the comments.



how to revert them?
@Dave,
You can remove execute perimssion as shown.
Hello, how many white spaces should I leave between the user and the rest of this sentence:
Same question for this one as well:
And this file needs to be reloaded after I modify it with some /etc/init.d … ? Thank you
How to bring back this commands for all users?
@Dimitry
Simply remove the
Cmnd_Alias SHUTDOWN = /sbin/shutdown,/sbin/reboot,/sbin/halt,/sbin/poweroffline from sudoers file and !SHUTDOWN.sudo su
shutdown
“Security” breached. Probably only a few dozen other ways to bypass that restriction. If you give someone sudoers ALL then you’ve pretty much given them the keys to the kingdom.