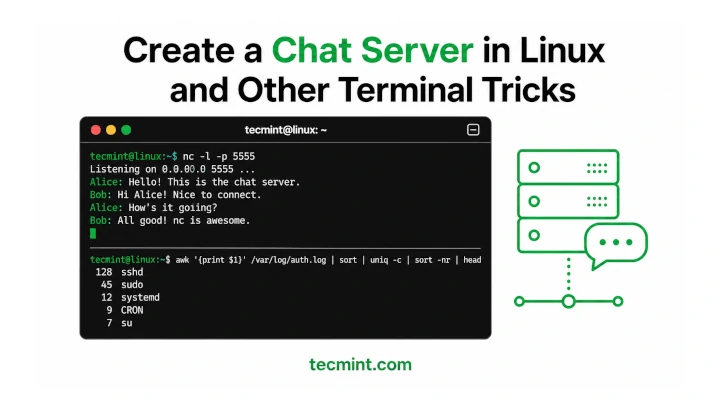
Computer networks have made it possible for end users to interact one with another in several ways. They have also provided a way to perform remote work without the hassle and the costs involved with traveling (or perhaps walking to a nearby office).
Recently, I discovered a program called conspy in the Debian stable repositories and was glad to find out that it is available for Fedora and derivatives as well.
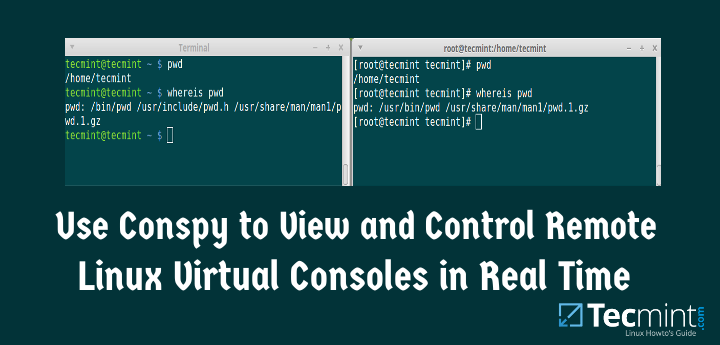
It allows a user to see what is being displayed on a Linux virtual console, and also to send keystrokes to it in real time. In a certain way, you can think of conspy as similar to VNC, with the difference that conspy operates in text mode (thus saving resources and making it possible to also support CLI-only servers) and in top of all that, does not require a server-side service to be installed prior to being used.
That said, you only need to make sure that there is network connectivity to the remote computer and you will learn to love conspy.
Installing conspy in Linux
In Debian 8 and derivatives, conspy is available directly from the repositories, so installing it is as simple as:
# aptitude update && aptitude install conspy
Whereas in CentOS 7 and other Fedora-based distros you first have to enable the Repoforge repository:
1. Go to http://pkgs.repoforge.org/rpmforge-release and search for the latest version of the repository (as of September 2015 the latest package is rpmforge-release-0.5.3-1.el7.rf.x86_64.rpm) and download it:
# wget http://pkgs.repoforge.org/rpmforge-release/rpmforge-release-0.5.3-1.el7.rf.x86_64.rpm
2. Install the repository package:
# rpm –Uvh rpmforge-release-0.5.3-1.el7.rf.x86_64.rpm
3. And then install the conspy package itself:
# yum update && yum install conspy
Testing Environment Used for conspy
To see how conspy works, we will ssh into a Debian 8 server [IP 192.168.0.25] (using Terminal or gnome ter, for example) where the ssh daemon is listening on port 11222:
# ssh –p 11222 [email protected]
Right next to our Terminal, we will place a Virtualbox window that will be used to display ttys. Remember that you will need to press Right Ctrl + F1 through F6 to switch between ttys inside a Virtualbox window, and Ctrl + Alt + F1 through F6 to switch between consoles in a real (i.e. not virtualized) server.
Using conspy to Display and Control ttys
To launch conspy, ssh into the remote server and then just type:
# conspy
followed by a tty number, (1 through 6). You will notice that the background color of your Terminal changes. We will use the tty command to identify the file name of the terminal currently connected to standard input. If a tty is not supplied as argument, the currently active virtual console is opened and tracked.
Note that after launching the program as:
# conspy 1
The first terminal (tty1) is displayed instead of pts/0 (the initial pseudo-terminal for a ssh connection):
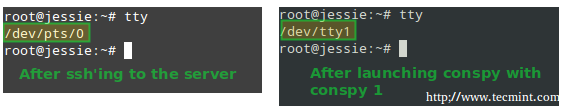
To exit, press Esc three times in quick succession.
Watch Conspy in Action
To better see conspy in action, please take a minute to watch the following screencasts:
1. Keystrokes being sent from the client to remote tty:
2. Tty contents are displayed in the client as they appear in the remote tty:
In the above videos you can see a couple of interesting things:
- You can run commands or type text in a pseudo-terminal and they will be visualized in the remote console, and viceversa.
- There is no need to launch a server-side program in the server at the distant location, as opposed to other tech support software that requires someone to start a service for you to connect remotely to.
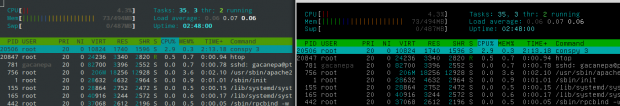
- Conspy also allows you to visualize in real time the output of programs such as top or ping which is refreshed or changed continuously with only a very slight delay. This includes ncurses-based programs such as htop – Linux Process Monitoring as well:
If you only want to view a remote terminal instead of sending keystrokes or commands, just launch conspy with the -v switch (view only).
Using conspy with Putty
If you use a Windows laptop or desktop for work you can still take advantage of conspy. After logging on to the remote system with Putty, the famous ssh client for Windows, you can still launch conspy as explained above, as shown in the following screencast:
Which goes to show that you can use this program regardless of the ssh client software that you use to remotely connect to a server.
Conspy Limitations
Despite its nice features, conspy also has some limitations, which you should take into account:
- It only allows you to view, connect to, or control real terminals (ttys), not pseudo ones (pts/Xs).
- It may display non-ASCII characters (á, é, ñ, to name a few examples) incorrectly or not at all:

It requires super user permissions (either as root or through sudo) to launch.
Summary
In this guide we have introduced you to conspy, a priceless tool to control remote terminals that consumes very little in terms of system resources.
I hope that you take the time to install and try out this great utility, and highly recommend you bookmark this article because in my humble opinion this is one of those tools that need to be a part of every system administrator’s skill set.
l look forward to receiving your feedback about this article. Feel free to drop me a line using the form below. Questions are also always welcome.



Does anyone know what that font is “Use Conspy to View and Control Remote Linux Virtual Consoles in Real Time” in the image at the top of this story?
I’ve searched for it – but cannot find it.
Was wondering what conspy can do that I can’t already do with tmux. I can already have many remote sessions with tmux, and even share keystrokes with them all, and much more.
@Fred,
If tmux meets all your needs, that’s great! One of the wonders of the FOSS ecosystem is that there are several ways to get things done. A simple example: you can change the group ownership of a file (let’s call it file1) to my_group with either of the following two commands:
chown :my_group file1
chgrp my_group file1
Of course we can have different opinions as to what is the best / most effective way to do things, but as long as the tools and the commands we choose get the job done, that’s a great thing IMHO.
True. I am always open to alternate ways of doing things. I have spent some time tooling tmux to meet my needs. There are other options for dealing with a large number of machines. I can perhaps deal with 10 machines concurrently with tmux, more if I push it. There’s an SSL option whose name escapes me.
Sorry for taking so long to respond to this. The notification wound up in my spam filter!!!
You can do that with GNU Screen too, so we have 3 tools to do the same task ;)
installed conspy in my machine and after ssh to the remote server and typed conspy. It says command not found. Using centos 6
@cjwalter,
Did you installed the right package for CentOS 6 and your architecture? Please note that this article was written for CentOS 7. Please make sure you installed the package listed in http://pkgs.repoforge.org/rpmforge-release/ for el6 and for x86_64 or i686 (depending on your system’s architecture). Please try and get back to us.
but when i type conspy in my local machine it is working.
Neat, I wasn’t aware of Conspy. You can also test using a local console: Press CTRL+ALT+F1 for tty1 or CTRL+ALT+F2 for tty2 etc
@Gitesh,
Thank you for your comment!