This tutorial only covers general security tips for CentOS 8/7 which can be used to harden the system. The checklist tips are intended to be used mostly on various types of bare-metal servers or on machines (physical or virtual) that provide network services.
However, some of the tips can be successfully applied to general-purpose machines too, such as Desktops, Laptops, and card-sized single-board computers (Raspberry Pi).
Requirements
1. Physical Protection
Lockdown your server rooms access, use racks locking and video surveillance. Take into consideration that any physical access to server rooms can expose your machine to serious security issues.
BIOS passwords can be changed by resetting jumpers on the motherboard or by disconnecting the CMOS battery. Also, an intruder can steal the hard disks or directly attach new hard disks to the motherboard interfaces (SATA, SCSI, etc), boot up with a Linux live distro, and clone or copy data without leaving any software trace.
2. Reduce Spying Impact
In case of highly sensitive data, you should probably use advanced physical protection such as placing and locking the server into a Faraday Cage or use a military TEMPEST solution in order to minimize the impact of spying the system via radio or electrical leaking emanations.
3. Secure BIOS/UEFI
Start the process of hardening your machine by securing BIOS/UEFI settings, especially set a BIOS/UEFI password and disable boot media devices (CD, DVD, disable USB support) in order to prevent any unauthorized users from modifying the system BIOS settings or altering the boot device priority and booting the machine from an alternate medium.
In order to apply this type of change to your machine you need to consult the motherboard manufacturer manual for specific instructions.
4. Secure Boot Loader
Set a GRUB password in order to prevent malicious users to tamper with kernel boot sequence or run levels, edit kernel parameters or start the system into a single-user mode in order to harm your system and reset the root password to gain privileged control.
5. Use Separate Disk Partitions
When installing CentOS on systems intended as production servers use dedicated partitions or dedicated hard disks for the following parts of the system:
/(root) /boot /home /tmp /var
6. Use LVM and RAID for Redundancy and File System Growth
The /var partition is the place where log messages are written to disk. This part of the system can exponentially grow in size on heavily traffic servers that expose network services such as web servers or file servers.
Thus, use a large partition for /var or consider setting up this partition using logical volumes (LVM) or combine several physical disks into one larger virtual RAID 0 device to sustain large amounts of data. For data, redundancy consider on using the LVM layout on top of the RAID 1 level.
For setting up LVM or RAID on the disks, follow our useful guides:
- Setup Disk Storage with LVM in Linux
- Create LVM Disks Using vgcreate, lvcreate and lvextend
- Combine Several Disks into One Large Virtual Storage
- Create RAID 1 Using Two Disks in Linux
7. Modify fstab Options to Secure Data Partitions
Separate partitions intended for storing data and prevent the execution of programs, device files or setuid bit on these type of partitions by adding the following options to fstab file as illustrated on the below excerpt:
/dev/sda5 /nas ext4 defaults,nosuid,nodev,noexec 1 2
To prevent privilege-escalation and arbitrary script execution create a separate partition for /tmp and mount it as nosuid, nodev, and noexec.
/dev/sda6 /tmp ext4 defaults,nosuid,nodev,noexec 0 0
8. Encrypt the Hard Disks at block level with LUKS
In order to protect sensitive data snooping in case of physical access to machine hard drives. I suggest you to learn how to encrypt disk by reading our article Linux Hard Disk Data Encryption with LUKS.
9. Use PGP and Public-Key Cryptography
In order to encrypt disks, use PGP and Public-Key Cryptography or OpenSSL command to encrypt and decrypt sensitive files with a password as shown in this article Configure Encrypted Linux System Storage.
10. Install Only the Minimum Amount of Packages Required
Avoid installing unimportant or unnecessary programs, applications, or services to avoid package vulnerabilities. This can decrease the risk that the compromise of a piece of software may lead to compromise other applications, parts of the system, or even file systems, finally resulting in data corruption or data loss.
11. Update the system frequently
Update the system regularly. Keep Linux kernel in sync with the latest security patches and all the installed software up-to-date with the latest versions by issuing the below command:
# yum update
12. Disable Ctrl+Alt+Del
In order to prevent users to reboot the server once they have physical access to a keyboard or via a Remote Console Application or a virtualized console (KVM, Virtualizing software interface) you should disable Ctrl+Alt+Del key sequence by executing the below command.
# systemctl mask ctrl-alt-del.target
13. Remove Unnecessary Software Packages
Install minimal software required for your machine. Never install extra programs or services. Install packages only from trusted or official repositories. Use minimal installation of the system in case the machine is destined to run its entire life as a server.
Verify installed packages using one of the following commands:
# rpm -qa
Make a local list of all installed packages.
# yum list installed >> installed.txt
Consult the list for useless software and delete a package by issuing the below command:
# yum remove package_name
14. Restart Systemd Services after Daemon Updates
Use the below command example to restart a systemd service in order to apply new updates.
# systemctl restart httpd.service
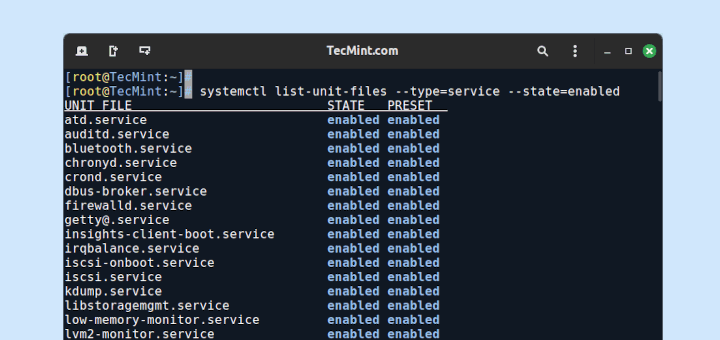
15. Remove Unneeded Services
Identify the services that are listening on specific ports using the following ss command.
# ss -tulpn
To list all installed services with their output status issue the below command:
# systemctl list-units -t service
For instance, CentOS default minimal installation comes with Postfix daemon installed by default which runs by the name of a master under port 25. Remove Postfix network service in case your machine will not be used as a mail server.
# yum remove postfix
16. Encrypt Transmitted Data
Do not use unsecured protocols for remote access or file transfer such as Telnet, FTP, or other plain text high protocols such as SMTP, HTTP, NFS, or SMB which, by default, does not encrypt the authentication sessions or sent data.
Use only sftp, scp for file transfers, and SSH or VNC over SSH tunnels for remote console connections or GUI access.
In order to tunnel a VNC console via SSH use the below example which forwards the VNC port 5901 from the remote machine to your local machine:
# ssh -L 5902:localhost:5901 remote_machine
On the local machine run the below command in order to virtual connection to the remote endpoint.
# vncviewer localhost:5902
17. Network Port Scanning
Conduct external port checks using the Nmap tool from a remote system over the LAN. This type of scanning can be used to verify network vulnerabilities or test the firewall rules.
# nmap -sT -O 192.168.1.10
18. Packet-filtering Firewall
Use firewalld utility to protect the system ports, open or close specific services ports, especially well-known ports (<1024).
Install, start, enable, and list the firewall rules by issuing the below commands:
# yum install firewalld # systemctl start firewalld.service # systemctl enable firewalld.service # firewall-cmd --list-all
19. Inspect Protocol Packets with Tcpdump
Use tcpdump utility in order to sniff network packets locally and inspect their content for suspicious traffic (source-destination ports, TCP/IP protocols, layer two traffic, unusual ARP requests).
For a better analysis of the tcpdump captured file use a more advanced program such as Wireshark.
# tcpdump -i eno16777736 -w tcpdump.pcap
20. Prevent DNS Attacks
Inspect the contents of your resolver, typically /etc/resolv.conf file, which defines the IP address of the DNS servers it should use to query for domain names, in order to avoid man-in-the-middle attacks, unnecessary traffic for root DNS servers, spoof or create a DOS attack.
This is just the first part. In the next part we’ll discuss other security tips for CentOS 8/7.





Yeah, I agree, I would never even install updates, that is the safer way to keep a machine online.
“15. Remove Unneeded Services”
That assumes that one knows which services are needed and which are not. How do I learn which services are essential and which ones I can remove?
@Dragonmouth,
That you need to figure out based on the requirements, it is difficult to tell what services are running on the server…
You missed my point. It is easy to find out what services are running on any particular PC. Unless you are a Linux expert, it is hard to know which of the services are unneeded.
When I was still running Windows, I knew what services I could safely disable because there were couple of sites that described all the services that could possibly run under Windows. Is/are there similar sites for Linux? Or do I have to a ‘Net search for a description of each individual one?
While installing Linux, it installs a vast number of services to your system, but you need to know which services are needed or not by running netstat command.
The netstat command will show a list of all services that are presently running with the State of LISTEN. If you can’t recognize a service that is displayed, you probably don’t need it.
“If you can’t recognize a service that is displayed, you probably don’t need it.”
That is a very dangerous policy. I don’t mean to be a PITA but I ran the command you suggested and I do not recognize most of the services displayed. Somehow I do not think killing those I do not recognize would be a good idea.
My original question still stands- Is there any place where I can find descriptions of what each service does? Other than Google each service.
@Dragonmouth,
That’s difficult to figure out, only an experience system admin can figure out. Check out the following article, might it help you – https://www.tecmint.com/remove-unwanted-services-from-linux/
Thank you for the link, Ravi.
Any advice on the best way to modify mount points after the system has already been built? Thanks again!!!
Very nicely done!!! Have you made one of these for CentOS 8 yet? Thanks
@Gator,
There isn’t much difference between CentOS 7 and CentOS 8, so most of the commands work on CentOS 8 as well..
is there any forum , where can we get some assist about CentOs or linux. actually i am in trouble , accessing tortoise svn repository in centOs
It’s important to test updates on an alternative system.
Yes, less than 1024. th apps require root privileges to bind on a port less than 1024. sorry, my bad.
Matei, I found a typo: well-known ports are those ports less than 1024