In this article, we shall a list of useful Linux security features that every system administrator should know. We also share some useful tools to help a system admin ensure security on their Linux servers.
The list is as follows, and is not organized in any particular order.
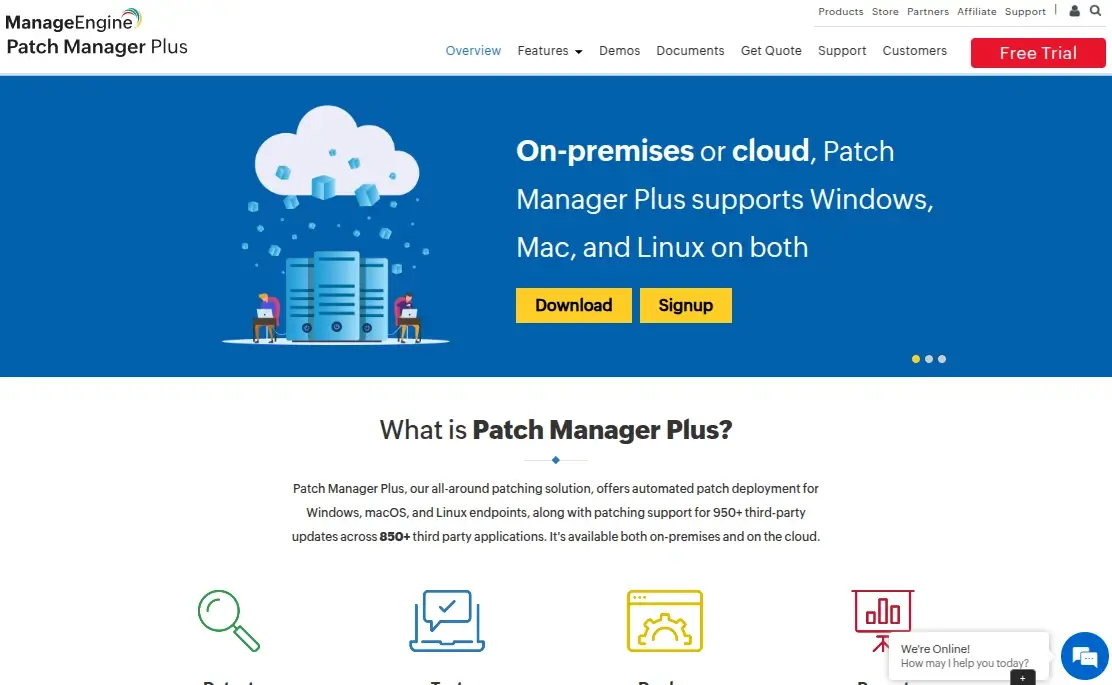
ManageEngine Patch Manager Plus
ManageEngine Patch Manager Plus is an automated patch management solution that provides enterprises with a single interface for all patch management tasks. It offers a single dashboard to manage, monitor, and deploy patches for Windows, macOS, and Linux systems.
The solution continuously scans systems to detect missing patches, including operating system and third-party application updates. Based on the severity of these patches, ranging from low to critical, Patch Manager Plus quickly classifies system health, allowing IT admins to address vulnerabilities efficiently.
Whether endpoints are on the local network, across a WAN, in remote offices, or part of a WFH setup, Patch Manager Plus simplifies patch deployment from either a cloud console or on-premises setup, which ensures all devices remain secure and compliant with minimal effort.
By automating patching tasks, organizations can mitigate security risks, improve system performance, and maintain operational continuity without the headache of manual intervention.
1. Linux User and Group Management
Linux user and group management is a basic yet very vital aspect of system administration. Note that a user can be a person or a software entity such as a web server processes and files owner.
Correct user management definition (which can entail a user’s account details, groups a user belongs to, what parts of a system a user can access, what programs they can execute, enforcing password organization password policies, etc.) can help a system administrator in ensuring secure system access and operation of users within a Linux system.
2. Linux PAM
PAM (Pluggable Authentication Modules) is a powerful and flexible suite of libraries for system-wide user authentication. Each library of functions that ships with PAM can be used by an application to request that a user be authenticated.
This enables a Linux system administrator to define how applications authenticate users. It’s powerful, however, and very challenging to understand, learn, and use.
3. Server/Host-based Firewall
Linux ships with the Netfilter subsystem that offers packet filtering functionalities, all kinds of network address and port translation, multiple layers of APIs for 3rd party extensions, and more.
All modern Linux firewalls solutions such as UFW (Uncomplicated Firewall), firewalld, nftables (the successor of iptables), and more, use this subsystem for packet filtering to help regulate, protect, and block network traffic going into or out of a Linux system.
4. Linux SELinux
A project originally developed by the United States National Security Agency (NSA), Secure Enhanced Linux (or SELinux in short) is an advanced Linux security feature.
It is a security architecture integrated into the Linux kernel using the Linux Security Modules (LSM). It supplements the traditional Linux discretionary access control (DAC) model by providing mandatory access control (MAC).
It defines the access and transition rights of every user, application, process, and file on the system; it governs the interactions of these entities using a security policy that specifies how strict or lenient a given Linux system installation should be.
SELinux comes pre-installed on most if not all RHEL-based distributions such as Fedora, CentOS-stream, Rocky Linux, AlmaLinux, etc.
5. AppArmor
Similar to SELinux, AppArmor is also a Mandatory Access Control (MAC) security module that provides an effective and easy-to-use Linux application security system. Many Linux distributions such as Debian, Ubuntu, and openSUSE come with AppArmor installed.
The major difference between AppArmor and SELinux is that it is path-based, it allows the mixing of enforcement and complain mode profiles. It also employs “include files” to ease development, besides it has a far lower barrier to entry.
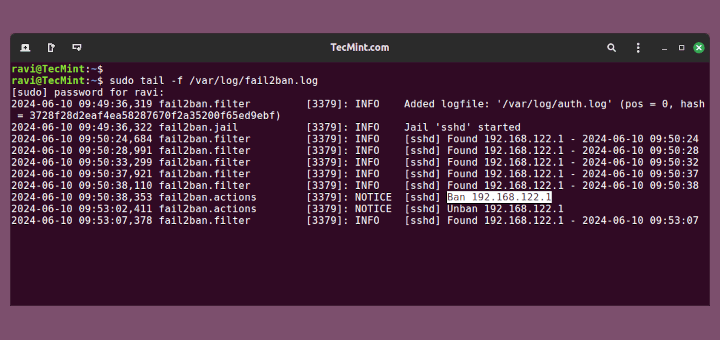
6. Fail2ban
Fail2ban is a widely-used server security tool that scans logs files for IP addresses showing malicious activity such as continued failed login attempts and more, and updates firewall rules to ban such an IP address for a specified time.
7. ModSecurity Web Application Firewall (WAF)
Developed by Trustwave’s SpiderLabs, ModSecurity is a free and open-source, powerful, and multi-platform WAF engine. It works with Apache, NGINX, and IIS web servers. It can help system administrators and web application developers by providing adequate security against a range of attacks, for example, SQL injections. It supports HTTP traffic filtering and monitoring, logging, and real-time analysis.
For more information, check out:
- How to Install ModSecurity for Nginx on Debian/Ubuntu
- How to Set Up ModSecurity with Apache on Debian/Ubuntu
8. Security Logs
Security logs help to keep track of events specifically related to the security and safety of your entire IT infrastructure or a single Linux system. These events include successful and failed attempts to access a server, applications, and more, activation of an IDS, alerts triggered, and much more.
As a system administrator, you need to identify effective and efficient log management tools and uphold security log management best practices.
9. OpenSSH
OpenSSH is the leading connectivity tool for remote login with the SSH network protocol. It enables secure communication between computers by encrypting traffic between them thus banishing malicious activities from cybercriminals.
Here are some useful guides to help you secure your OpenSSH server:
- How to Secure and Harden OpenSSH Server
- 5 Best OpenSSH Server Best Security Practices
- How to Setup SSH Passwordless Login in Linux
10. OpenSSL
OpenSSL is a popular, general-purpose cryptography library, which is available as a command-line tool that implements the Secure Sockets Layer (SSL v2/v3) and Transport Layer Security (TLS v1) network protocols and related cryptography standards required by them.
It is commonly used to generate private keys, create CSRs (Certificate Signing Requests), install your SSL/TLS certificate, view certificate information, and much more.
11. Intrusion Detection System (IDS)
An IDS is a monitoring device or software that detects suspicious activities or policy violations and generates alerts when they are detected based on these alerts, as a system administrator or security analyst, or any concerned personnel, you can investigate the issue and take the appropriate actions to redress the threat.
There majorly two major kinds of IDS: host-based IDS which a deployed to monitor a single system and network-based IDS which is deployed to monitor an entire network.
There are numerous software-based IDS for Linux such as Tripwire, Tiger, AIDE, and others.
12. Linux Monitoring Tools
To ensure the availability of the various systems, services, and applications within your organization’s IT infrastructure, you need to keep an eye on these entities in real time.
The best way to achieve this is through Linux monitoring tools, importantly, those that have issue detection, reporting, and alert generation capabilities, such as Nagios, Zabbix, Icinga 2, and more.
13. Linux VPN Tools
A VPN (short for Virtual Private Network) is a mechanism for encrypting your traffic on unsecured networks such as the Internet. It provides a secure internet connection to your organization’s network over the public internet.
Check out this guide to quickly set up a VPN in the cloud: How to Create Your Own IPsec VPN Server in Linux
14. System and Data Backup and Restore Tools
Backing up data ensures that your organization does not lose critical data in case of any unplanned events. Recovery tools help you restore data or systems to an earlier point in time to help your organization recover from a disaster of any magnitude.
Here are some useful articles about Linux backup tools:
- 25 Outstanding Backup Utilities for Linux Systems
- 7 Best Open Source “Disk Cloning/Backup” Tools for Linux Servers
- Relax-and-Recover – Backup and Recover a Linux System
- How to Clone or Backup Linux Disk Using Clonezilla
15. Linux Data Encryption Tools
Encryption is a premier security technique in data protection that ensures that only authorized parties have access to information that is stored or in transit. You will find a multitude of data encryption tools out there for Linux systems that you can leverage for security.
16. Lynis – Security Audit Tool
Lynis is a free, open-source, flexible, and popular host security auditing and vulnerability scanning and assessment tool. It runs on Linux systems and other Unix-like operating systems such as Mac OS X.
17. Nmap – Network Scanner
Nmap (short for Network Mapper) is a widely used, free, open-source, and feature-rich security tool for network exploration or security auditing. It is cross-platform, therefore it runs on Linux, Windows, and Mac OS X.
18. Wireshark
Wireshark is a fully-featured and powerful network packet analyzer, which allows for live capture of packets that can be saved for later/offline analysis.
It’s also cross-platform and runs on Unix-like systems such as Linux-based operating systems, Mac OSX, and Windows.
19. Nikto
Nikto is a powerful, open-source web scanner that scans a website/application, virtual host, and web server for known vulnerabilities and misconfiguration.
It attempts to identify installed web servers and software before performing any tests.
20. Linux Update
Last but not least, as a system administrator, you should perform regular software updates right from the operating system to installed packages and applications, to ensure that you have the latest security fixes in place.
$ sudo apt update [On Debian, Ubuntu and Mint] $ sudo yum update [On RHEL/CentOS/Fedora and Rocky Linux/AlmaLinux] $ sudo emerge --sync [On Gentoo Linux] $ sudo pacman -Syu [On Arch Linux] $ sudo zypper update [On OpenSUSE]
That’s all we had for you. This list is shorter than it should be. If you think so, share with us more tools that deserve to be known to our readers via the feedback form below.