One of the serious needs of a Linux system is to be kept up to date regularly with the latest security patches or updates available for the corresponding distribution.
In a previous article, we’ve explained how to configure automatic security update in Debian/Ubuntu, in this article we will explain how to set up your CentOS/RHEL 7/6 distribution to auto update essential security packages when needed.
Other Linux distributions in the same families (Fedora or Scientific Linux) can be configured similarly.
Configure Automatic Security Updates on CentOS/RHEL Systems
On CentOS/RHEL 7/6, you will need to install the following package:
# yum update -y && yum install yum-cron -y
Enable Automatic Security Updates on CentOS/RHEL 7
Once the installation is complete, open /etc/yum/yum-cron.conf and locate these lines – you will have to make sure that the values matches those listed here:
update_cmd = security update_messages = yes download_updates = yes apply_updates = yes
The first line indicates that the unattended update command will be:
# yum --security upgrade
whereas the other lines enable notifications and automatic download and installation of security upgrades.
The following lines are also required to indicate that notifications will be sent via email from root@localhost to the same account (again, you may choose another one if you want).
emit_via = email email_from = root@localhost email_to = root
Enable Automatic Security Updates on CentOS/RHEL 6
By default, the cron is configured to download and install all updates immediately, but we can change this behavior in /etc/sysconfig/yum-cron configuration file by modifying these two parameters to yes.
# Don't install, just check (valid: yes|no) CHECK_ONLY=yes # Don't install, just check and download (valid: yes|no) # Implies CHECK_ONLY=yes (gotta check first to see what to download) DOWNLOAD_ONLY=yes
To enable email notification that about the security package updates, set the MAILTO parameter to a valid mail address.
# by default MAILTO is unset, so crond mails the output by itself # example: MAILTO=root [email protected]
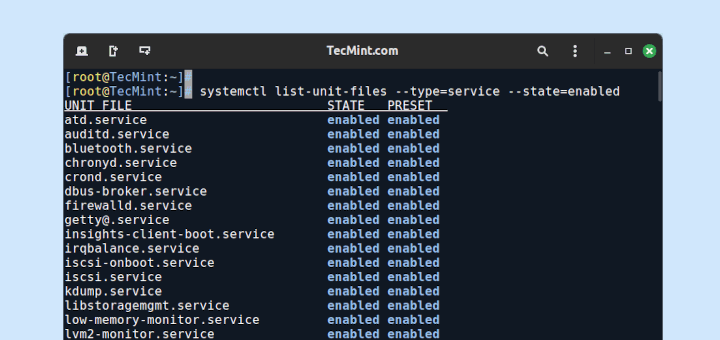
Finally, start and enable the yum-cron service:
------------- On CentOS/RHEL 7 ------------- systemctl start yum-cron systemctl enable yum-cron ------------- On CentOS/RHEL 6 ------------- # service yum-cron start # chkconfig --level 35 yum-cron on
Congrats! You have successfully set up unattended upgrades on CentOS/RHEL 7/6.
Summary
In this article we have discussed how to keep your server updated regularly with the latest security patches or updates. Additionally, you learned how to configure email notifications in order to keep yourself updated when new patches are applied.
If you have any concerns about this article? Feel free to drop us a note using the comment form below. We look forward to hearing from you.





Hi When you do patch like you update security,
from where system will get updated
Could you please clarify!
Is this called as os patching in Linux?
but how to check it working or not please tell
This information is dangerously incorrect: the yum command with the –security flag on CentOS does not work. Please see the following articles:
https://www.caseylabs.com/centos-automatic-security-updates-do-not-work/
https://www.centos.org/forums/viewtopic.php?t=59369#p251143
It would be nice if Mr. Cánepa would confirm the proposed problems with this HowTo’s application to CentOS, and possibly rewrite it to just apply to Red Hat. I already know about this issue, and came across this post looking for more novel solutions. Leaving this incorrect information out there in the wild seems irresponsible.
The point is that the CentOS project doesn’t supply the Security Errata which is necessary to perform security updates. They don’t provide updateinfo.xml, and thus the code `yum –security upgrade` above will do nothing to apply security updates. You should be able to verify this in the logs after running it for a week.
So, don’t get your hopes up.
If you want security updates, use RHEL or Scientific Linux; or use one of the third-party projects to do this work.
For more information about the lack of security RPMs for CentOS, see:
* petersouter.co.uk/the-story-of-errata-for-centos/
* grokbase.com/t/centos/centos-devel/14a1zyx1dd/yum-plugin-security-and-shellshock
* https://www.centos.org/forums/viewtopic.php?t=4296
CentOS have not security date into packages, so it can not be recognize as security. Did you check it, before wrote this article?
Did you actually read this article, or just took a quick glance at it? Please note what I actually wrote is, “…auto update essential security packages when needed…”. You can also refer to https://www.centos.org/forums/viewtopic.php?t=4296 if in doubt.
Gabriel, listen to the commenters above you – the point they are making is that CentoS DOES NOT PROVIDE SECURITY ERRATA. Your `yum –security upgrade` command, will always be no-op and return “No packages needed for security; x packages available”, regardless of whether there are known vulnerabilities in your installed packages.