A Dynamic Host Configuration Protocol (DHCP) server dynamically assigns IP addresses and other network configuration parameters to each device on a network. A DNS forwarder on a LAN forwards DNS queries for non-local domain names to upstream DNS servers (outside that network). A DNS caching server answers recursive requests from clients so that the DNS query can be resolved faster, thus improving DNS lookup speeds to previously visited sites.
dnsmasq is a lightweight, easy to configure DNS forwarder, DHCP server software and router advertisement subsystem for small networks. Dnsmasq supports Linux, *BSD, Mac OS X as well as Android.
It features a DNS subsystem that provides a local DNS server for the network, with forwarding of all query types to upstream recursive DNS servers and caching of common record types. The DHCP subsystem supports DHCPv4, DHCPv6, BOOTP, PXE, and a TFTP server. And the router advertisement subsystem supports basic autoconfiguration for IPv6 hosts.
In this article, we will walk you through the instructions on how to install and setup DNS/DHCP Server Using dnsmasq on CentOS/RHEL 8/7 distributions.
Installing dnsmasq in CentOS and RHEL Linux
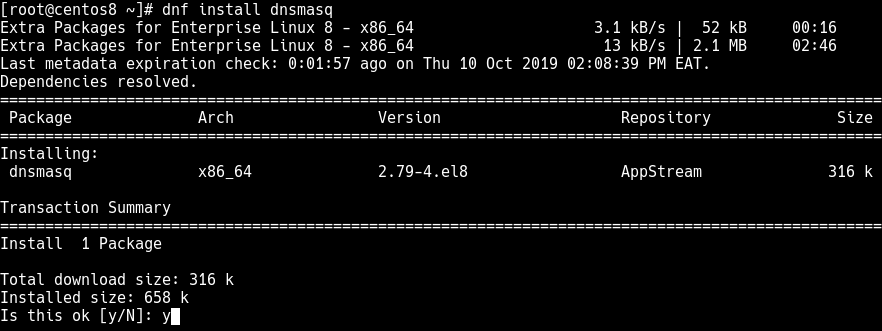
1. The dnsmasq package is available in the default repositories and can be easily installed using the YUM package manager as shown.
# yum install dnsmasq
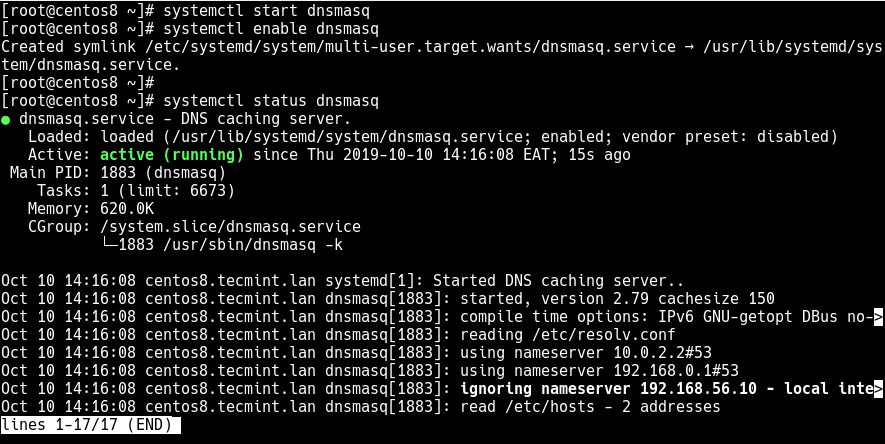
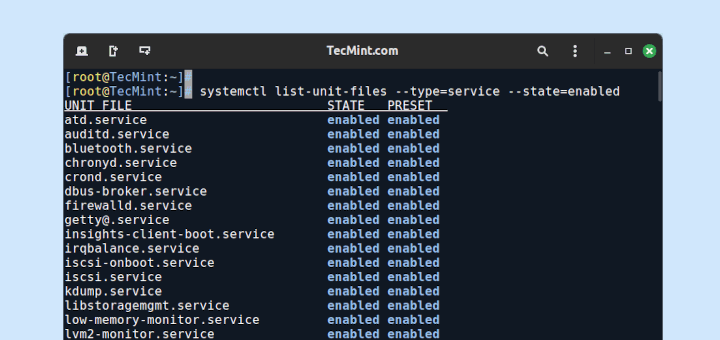
2. Once the dnsmasq package installation is complete, you need to start the dnsmasq service for now and enable it to automatically start at system boot. Besides, check its status to ensure that it is up and running using the following systemctl commands.
# systemctl start dnsmasq # systemctl enable dnsmasq # systemctl status dnsmasq
Configuring dnsmasq Server in CentOS and RHEL Linux
3. The dnsmasq server can be configured via the /etc/dnsmasq.conf file (which contains well commented and explained options), and user-defined configuration files can also be added in the /etc/dnsmasq.d directory.
DNS is enabled by default, so before making any changes, make sure to create a backup of /etc/dnsmasq.conf file.
# cp /etc/dnsmasq.conf /etc/dnsmasq.conf.orig
4. Now open the /etc/dnsmasq.conf file using your favorite text-based editor and make the following suggested configuration settings.
# vi /etc/dnsmasq.conf
The listen-address the option is used to set the IP address, where dnsmasq will listen on. To use your CentOS/RHEL server to listen for DHCP and DNS requests on the LAN, set the listen-address option to its LAN IP addresses (remember to include 127.0.0.1) as shown. Note that the server IP must be static.
listen-address=::1,127.0.0.1,192.168.56.10
Related to the above, you can restrict the interface dnsmasq listens on using the interface option (add more lines for more than one interface).
interface=eth0
5. If you want to have a domain (which you can set as shown next) automatically added to simple names in a hosts-file, uncomment the expand-hosts option.
expand-hosts
6. To set the domain for dnsmasq, which means DHCP clients will have fully qualified domain names as long as the set domain is matched, and sets the “domain” DHCP option for all clients.
domain=tecmint.lan
7. Next, also define the upstream DNS server for non-local domains using the server option (in the form server=dns_server_ip) as shown.
# Google's nameservers server=8.8.8.8 server=8.8.4.4
8. Then you can force your local domain to an IP address(es) using the address option as shown.
address=/tecmint.lan/127.0.0.1 address=/tecmint.lan/192.168.56.10
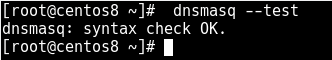
9. Save the file and check the configuration file syntax for errors as shown.
# dnsmasq --test
Configuring dnsmasq with /etc/resolv.conf File
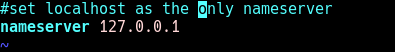
10. In this step, you need to make all queries to be sent to dnsmasq by adding the localhost addresses as the only nameservers in /etc/resolv.conf file.
# vi /etc/resolv.conf
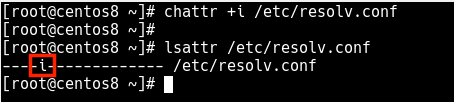
11. The /etc/resolv.conf file is maintained by a local daemon especially the NetworkManager, therefore any user-made changes will be overwritten. To prevent this, write-protect it by setting the immutable file attribute (disabling write access to the file) using the chattr command as shown.
# chattr +i /etc/resolv.conf # lsattr /etc/resolv.conf
Defining DNS Hosts and Names
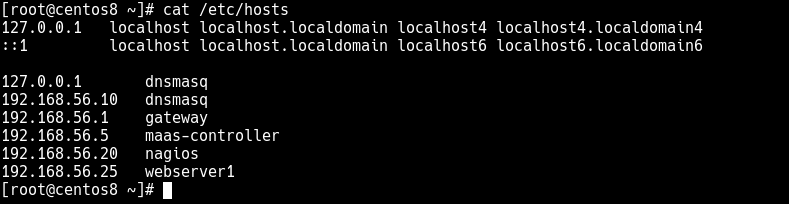
12. The Dnsmasq reads all the DNS hosts and names from the /etc/hosts file, so add your DNS hosts IP addresses and name pairs as shown.
127.0.0.1 dnsmasq 192.168.56.10 dnsmasq 192.168.56.1 gateway 192.168.56.100 maas-controller 192.168.56.20 nagios 192.168.56.25 webserver1
Important: Local DNS names can also be defined by importing names from the DHCP subsystem, or by the configuration of a wide range of useful record types.
13. To apply the above changes, restart the dnsmasq service as shown.
# systemctl restart dnsmasq
14. If you have the firewalld service running, you need to open DNS and DHCP services in the firewall configuration, to allow requests from hosts on your LAN to pass to the dnsmasq server.
# firewall-cmd --add-service=dns --permanent # firewall-cmd --add-service=dhcp --permanent # firewall-cmd --reload
Testing Local DNS
15. To test if the local DNS server or forwarding is working fine, you need to use tools such as dig or nslookup for performing DNS queries. These tools are provided by the bind-utils package which may not come pre-installed on CentOS/RHEL 8, but you can install it as shown.
# yum install bind-utils
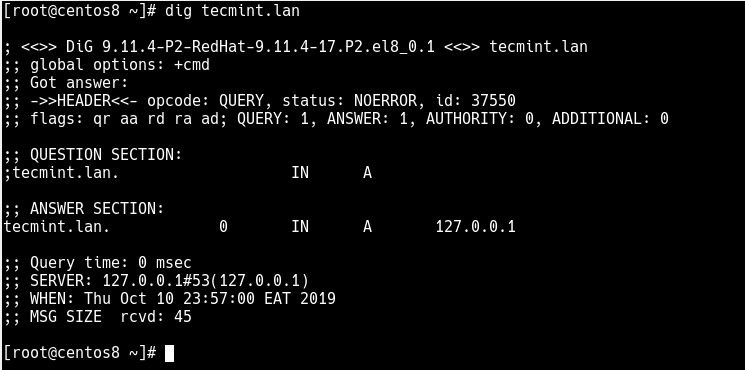
16. Once you have installed, you can run a simple query on your local domain as shown.
# dig tecmint.lan OR # nslookup tecmint.lan
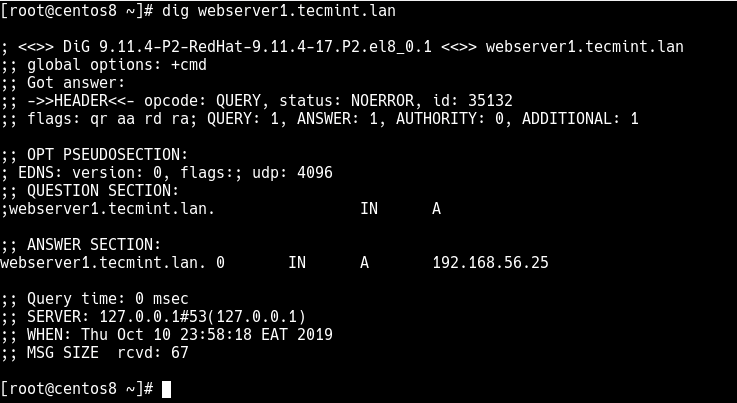
17. You can also try to query the FQDN of one of the servers.
# dig webserver1.tecmint.lan OR # nslookup webserver1.tecmint.lan
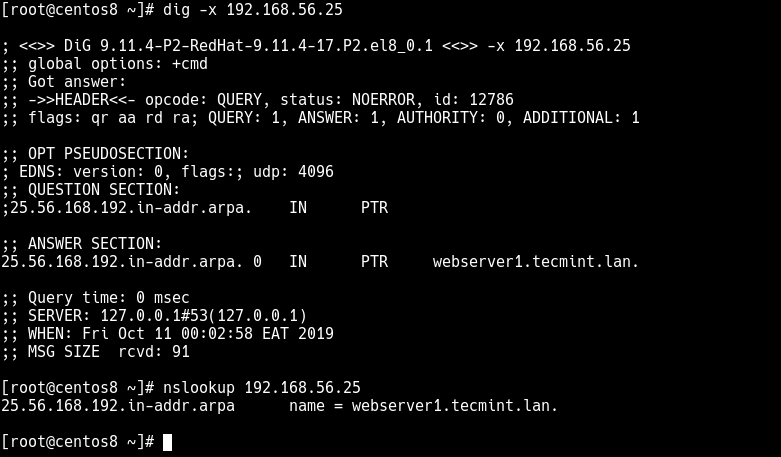
18. To test a reverse IP lookup, run a similar command.
# dig -x 192.168.56.25 OR # nslookup 192.168.56.25
Enable DHCP Server Using dnsmasq
19. You can enable the DHCP server by uncommenting the dhcp-range option and supply the range of addresses available for lease and optionally a lease time e.g (repeat for more than one network).
dhcp-range=192.168.0.50,192.168.0.150,12h
20. The following option defines where the DHCP server will keep its lease database, this will helps you to easily check IP addresses it has assigned.
dhcp-leasefile=/var/lib/dnsmasq/dnsmasq.leases
21. To make the DHCP server to authoritative mode, uncomment the option.
dhcp-authoritative
22. Save the file and restart the dnsmasq service to apply the recent changes.
# systemctl restart dnsmasq
That brings us to the end of this guide. To reach us for any questions or thoughts you want to share about this guide, use the feedback form below.





I think you did wrong with the resolv.conf permission part. It’s been overwritten from time to time due to another daemon controlling it.
It’s a link in the place. So instead of making it readonly, you shall do this:
Stop the systemd dns daemon running on port 53
Replace it with dnsmasq running on port 53.
Take back control of /etc/resolv.conf from //.
Unlink to get back control of the resolv.conf from ”, then overwrite.
How is the flow work:
System → resolv.conf (been controlled by other daemons **if not unlink**).
dnsmasq → hard-coded results /odoo.com/127.0.0.1 with wildcard match,**break;**
/etc/hosts with an exact match, **break;**
upstream DNS server, **break or timeout then continue
Other ns in resolv.conf if dnsmasq timeout, which would be several seconds.
Might need to edit`/etc/network/interfaces for persistent configuration, or the file `/etc/netplan/` on Ubuntu servers.
Very helpful article, thank you sir!
Why PTR Record is not working?
any idea?
Also, how to add a default search domain on dnsmasq?
How to force a domain name to an IPv6 address in dnsmasq6.conf
Thank you.
I had a question
Suppose I have several directories in the localhost
What should I do if, for example, I want to redirect each site to that directory as follows?
DNS resolves hostnames to IP’s or the other way around it has nothing to do with URI’s i.e address=/example1.com/127.0.0.1 resolves example1.com to ip address 127.0.0.1 nothing more.
If you want some kind of redirect to configure it inside of your web server DNS can’t do this
I want to block access to certain domains on the Internet for individual devices on my network by using the DNS notation. How do I do that with dnsmasq?
You just resolve those domains to localhost (127.0.0.1)
Yes, but how to point the devices to read that configuration? My idea was to reroute all connections (both in- and out-) received and sent by my iPhone to my Mac instead of the router. That way it would read my host’s file settings.
Also, how to make dnsmasq respect a custom proxy framework I already use to not screw things up and render connectivity unusable.
I would think you would have to configure your iPhone’s network settings to use the local DNS server.